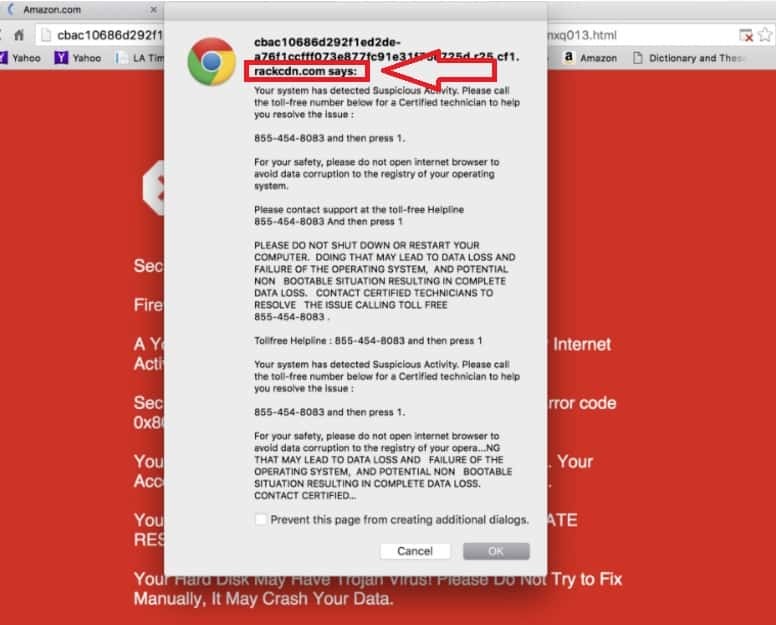
This page aims to help you remove the Rackcdn.com “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Stubborn pop-ups that continue showing up while you’re surfing the Internet may be very infuriating, there’s no doubt about it. They can effectively take control of your screen and affect your regular browsing in a very negative way. Because of that, it’s easy to see why you’d prefer to get rid of those commercials immediately.
Such ads are often the work of some Browser Hijacker such as the pesky Rackcdn.com. Helping you eliminate the Ads, however, is not the entire goal of this text – we’ll also teach you the best way to spot a Browser Hijacker well before it infects your PC and also tell you what activities to take for you to guard your laptop or computer.
Is the nature of these apps dangerous?
Despite Rackcdn.com not being an actual malicious software, it can still work as a backdoor for high-risk cyber-threats such as Trojan Horses or Ransomware. Not only are the Ads oftentimes fake, but they might be hazardous too. In the worst case scenario, by interacting with an advert, you could potentially be redirected to some illegal and virus-infested website. Nevertheless, there’s no need to worry – due to the fact this happens pretty rarely, you just need to be careful.
Browser Hijacker applications are also well-known for one more bad trait that they oftentimes possess – they tendency of tracking the user’s browsing activities. By spying on your internet activities, the Browser Hijacker could see what ads are best for your current interests. There’s a certain risk to such a behaviour though – your information might be resold to all sorts of people.
Lastly, there is the high probability of the Browser Hijacker causing your computer’s performance to become very sluggish. Software programs like this usually use quite a bit of the machine’s resources and this can result in errors and even system crashes.
The best ways to keep hijackers away
One of several possible strategies that Browser Hijackers use to get around is the software-bundling. Application bundles are frequently utilized to advertise various applications from the same developer and to also sneak Browser Hijackers in. Most often, the annoying app is combined with some free or cheap program that people may install onto their computer systems.
Quite common people say that Browser Hijackers get installed in a stealthy way without anyone’s knowledge or consent. This might be considered true, in a sense. However, specs for the added software applications which are getting installed alongside the main program are typically presented in the Advanced installation option. The problem is, few are the people who bother to have a look at it. What users typically do is, they neglect these settings and go with the regular installation instead. Needless to say, such information is also usually listed in the EULA but we all know that hardly anyone pays attention to that wall of text anyway.
An essential rule here is to make sure that you only go to dependable websites when acquiring new software. If you’re really in need to download a certain program from a suspicious a location, at least make sure you remember to utilize the advanced installation setting. This might appear to be a simple piece of advice but it will keep your Computer protected.
SUMMARY:
| Name | Rackcdn.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Rackcdn.com “Virus”
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone





Leave a Comment