This page aims to help you remove RecordedYou. Our removal instructions work for every version of Windows.
If you think (or know) that a Trojan Horse named RecordedYou is presently residing in your system, even if there’s no visible harm done to anything, you should take immediate measures to eliminate the threat before anything bad happens to your data, computer, or virtual privacy. The Trojans like RecordedYou are advanced tools used in many different kinds of cyber crimes. Here, we will give you some examples of what a Trojan Horse infection may be capable of doing, but you should remember that those are only examples – there could be many other malicious activities that such an infection may be able to carry out, which won’t be mentioned here.
The threat of the RecordedYou Email
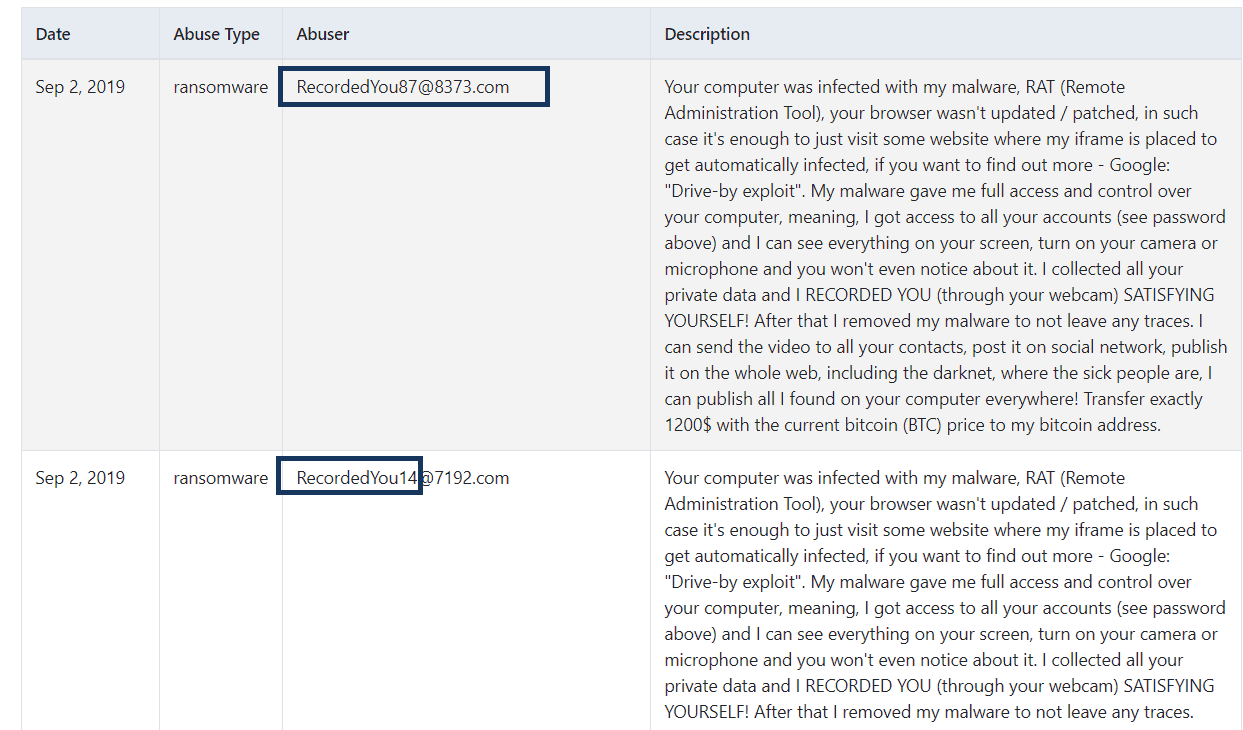
A screenshot of user complaints by the RecordedYou Email
A typical thing about this sort of malware infections is that they are able to get elevated privileges in the attacked computer – this is the basis for everything else they may try to do later on. Elevated (or administrative) privileges means that a user or a program with such rights would have all the access that the computer’s Admin would normally have. Needless to say, this opens a whole world of opportunities to a Trojan that manages to gain this sort of access, and most Trojans do. However, they do not typically do it on their own. Instead, a Trojan would normally rely on the carelessness of its victims to gain Admin rights in the machine. This is why so many Trojans like RecordedYou are presented to their potential victims in the form of some file – for example, a fake installer for some popular game or program. Of course, such files aren’t distributed through official sites of the game/program that the Trojan is disguised as. Instead, such data can typically be found in sketchy sites and sites that distribute pirated content – one more reason why visiting such sites and downloading stuff from them is a bad idea. Once the infected piece of data gets executed on the computer by a user with Admin privileges, the disguised Trojan would gain all the access and control it needs to complete its agenda.
As you have probably already guessed, there is an incredible variety of harmful things that a rojan with Admin rights may be able to do. For instance, it may run processes of espionage in your system, it may keylog your keystrokes, screen-capture everything you do in your computer, and even mess with your software and data. In addition, some Trojans are used as covert downloaders for Ransomware and other threats that could silently enter your system with the help of the Trojan. And those are only some of the more common examples. We can’t go into detail about the whole variety of things that a Trojan the likes of RecordedYou may be capable of conducting. Instead, it is way more important to tell you that the threat must be removed ASAP regardless of its end goal, and for that we have prepared a guide that can allow you to liberate your infected system from the threat that RecordedYou represents:
SUMMARY:
| Name | RecordedYou |
| Type | Trojan |
| Detection Tool |
RecordedYou Email Spam Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment