This page aims to help you remove .Rectot Virus Ransomware for free. Our instructions also cover how any .Rectot file can be recovered.
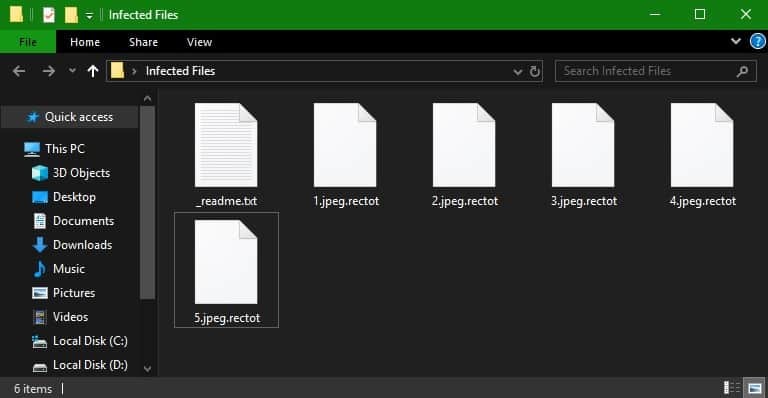
.Rectot Virus is a new strain of the Stop Ransomware. After the system is infected, the virus leaves a _readme.txt file with the following instructions:
ATTENTION!
Don't worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-6COaKAec5A
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
[email protected]
Reserve e-mail address to contact us:
[email protected]
Our Telegram account:
@datarestore
Introduction to Ransomware
The following paragraphs that you’re about to read are going to provide you with vital details concerning a dangerous virus program known under the name of .Rectot Virus. Such a noxious virus could seal all valuable documents which you may have on your PC hard-drive without your knowledge or approval. As soon as the encryption process has been completed, the the virus’ victim usually receives an unnerving note from the virus saying that their files have been locked up using a sophisticated crypto-code and that a ransom needs to be paid in exchange for the access to the computer files. The notification’s purpose would be to give instructions to the user regarding how to make the money payment and have it sent to the online criminal who has infiltrated the Machine. The idea is that, after the demanded money is sent to the hacker, the user will be sent a decryption code that could allow them to regain access to their private computer files. In case the requested ransom is not paid, the victim is threatened to never gain access to their data files again. Whether or not you are a current victim of the noxious .Rectot Virus or just someone who is willing to learn how Ransomware programs function together with the way one can possibly eliminate them, you should definitely read the next lines as well.
How the .Rectot Ransomware Works
Ransomware is unlike other, more common types of malware that customers generally face on the internet. Ransomware cryptoviruses operate in different ways and can’t be compared with any other sort of common viruses like Trojans, for example. What sets apart Ransomware from the other malware categories is that Ransomware would normally not seek to inflict any damage to your PC or destroy anything saved on your disks. Because of the initial lack of real damage at the beginning of the contamination, this Ransomware is capable of staying hidden from most forms of security software that the computer of the harassed user may rely on. The truth is, the encryption of your essential files might stay concealed and your anti-malware application may not be able to spot it as this ransomware is not programmed to destroy anything on your PC – this virus only renders your files unavailable. That’s how this form of malware can achieve its plan and why it only gets exposed when the damage has already occurred and the targeted date files are made not reachable. The signs and symptoms of the appearance of .Rectot File on your system are usually missing for the duration of the encryption process which makes it nearly impossible to spot the virus in time.
Bitcoins and Payment – the Ransom
Online hackers who utilize .Rectot Virus and other types of Ransomware usually attempt to get under the skin of the user and exploit their likely lack of knowledge and their current emotional state. Due to this, it is even more critical that you learn more about Ransomware so that you know how you can handle this sort of virus. First of all, consider this – the most popular ransom payment technique demanded by cyber criminals who use Ransomware would be the infamous bitcoin currency. The key reason why we mention this is because of the fact that bitcoins are virtually untraceable. Through the use of bitcoins, the online hackers who’re currently blackmailing you will be able to preserve their anonymity. Sadly, there haven’t been many examples where hackers terrorizing someone through Ransomware have been revealed in the end. On the flip side, in many cases customers who have sent the requested ransom money have later on realized that the decryption key would still not be sent to them. With everything that we have mentioned so far, it should be obvious why going for the the ransom transaction is generally seen as a bad idea. Something that we can offer as an alternative method for fighting off .Rectot Virus is our removal guide below. Despite the fact that we can’t assure you that the guide will work in your case, it certainly won’t hurt or cost you anything whatsoever to give it a try.
SUMMARY:
Remove .Rectot Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply