This page aims to help you remove the Amazonaws Virus. In case you are wondering what is amazonaws and why is s3 amazonaws being flagged as a potential computer virus we are here to answer those questions for you.
In this article we are going to do our best to shed some light on the amazonaws virus and explain why a seemingly reputable Amazon service has been accused of wrongdoing, it is a somewhat complex situation so if you are amongst the affected users we recommend reading through this initial information first before plunging into our removal instructions. The reason why we ask this of you is you need to familiarize with the issue first, because s3 amazonaws is not malware per se. Bear with us and we will try to explain in as much detail as possible.
Amazonaws
Amazonaws is a legitimate cloud service that some online databases flag as a browser hijacker – a type of sites and apps that cause unwanted browser changes. Amazonaws may be deemed a hijacker because hackers sometimes use it for malware distribution.
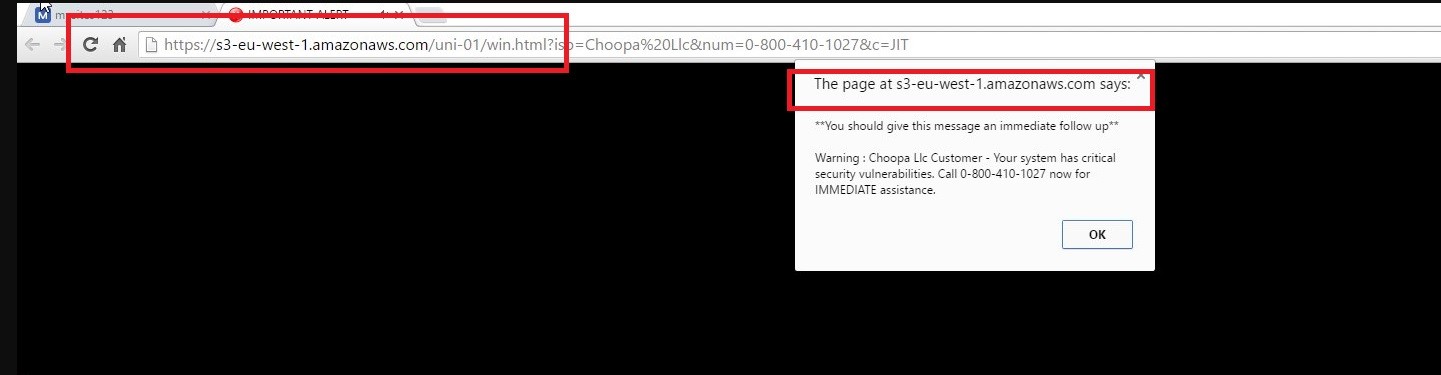
The Amazonaws Virus will display pop up windows and messages
A number of users have reported various problems with the service being labeled “unsafe” or “malicious” by Chrome and Firefox amongst others. The typical symptoms for a Browser Hijacker are present:
- Whenever you click on a link you are being redirected to another website. A definite symptom of a Browser Hijacker infection.
- The unwanted pop-up ads are also present of course. While seeing references to the domain in question (s3.amazonaws.com) is definitely not problematic in itself, the fact that users can essentially store more or less any file in S3 makes it virtually impossible to know whether someone uploaded malicious files are there.
- In the past the AWS (Amazon Web Service) credentials have been a common theme for hacker attacks so it’s also quite possible that an account owner has been compromised. If you are among the affected and recognize the clear cut signs that you are in fact dealing with an amazonaws virus then it is high time you start reading our removal instructions, there is absolutely no reason why you should not remove this from your system right this instance, again you will be removing the amazonaws virus, not the legitimate service. It can contend with one of the more dangerous viruses our there Zeus Virus.
What is Amazonaws?
A most important question indeed. S3 Amazonaws is an online cloud based storage web service. The S3 actually stands for Simple Storage Service. It has been around since March 2006. It has been most commonly used for file hosting, web hosting and as a storage for backup systems. So far so good, nothing wrong with this service at first glance. And you would be right to assume so for the most part. As we already mentioned s3 amazonaws is not a malware. So why is it being flagged as a potential virus, more specifically the type known as browser hijacker by a number of online databases?
The Amazonaws Virus
The Amazonaws virus is a browser hijacker element that enters the browser without the user’s informed permission. The Amazonaws virus is known for making unwanted browser changes and triggering automatic redirects to the Amazonaws site, which is actually a legitimate cloud storage service.
In essence, the amazonaws virus is a “browser hijacker” or possibly a malware. Browser hijackers are not legally considered to be a crime, but are merely crude promotional tools. Unlike normal advertisements, browser hijackers come bundled with free software and other programs. This usually requires a warped variant of user consent to infiltrate your PC. They reside in a legal grey area with no consensus from the online community whether you clicking on “next” in an installer is a consent. So, the browser hijacker basically tries to make you go to a specific websites or search engine to promote it and divert traffic towards it.
A far scarier situation is if a malware is the one responsible for your problems. In that case, things may be dire. The files responsible for the infections may have brought something else on your PC as well and your personal information may be exposed. Frequent examples of malware include stealing all sorts of personal information from you, including accounts and passwords to sensitive websites, like online banking credentials, amazon, ebay, alibaba and so forth. Depending on whether the malware in question is a trojan horse, the hacker may even have a direct access to your PC. The most disturbing violations even include the ability for the perpetrator to see you through webcams. While the chances of this last part actually happening are slim, we advise you to be extremely cautious when reading the steps in our guide below. In case you really do have a malware in your system, and you fail to take actions, you may end up with a Ransomware (see our Spora Ransomware Removal Guide for example) in your system – and that can be particularly disastrous if you do not have backups of your important files.
SUMMARY:
| Name | Amazonaws |
| Type | Browser Hijacker or Trojan |
| Detection Tool |
Remove S3.Amazonaws Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Hi Rehaan,
Did you go through the rest of the guide?
You are most welcome William. We are glad we could help you. Keep us posted if you have any other difficulties:)
Hi David,
you should delete these IPs
Hi Hannah, try running Notepad as admin first (search for notepad, right-click -> run as admin). Now open Notepad, select File-> Open and manually navigate to the file in C/Windows/System32/Drivers/Etc
Hi Schmoop,
at this point i would suggest to you to download SpyHunter from one of our banners above and use the free scan feature. The scanner will locate any infected files where you can delete them manually. Keep us posted if you need further help.
Hi Random Guy,
what do you mean you cannot find the notepad?
Hi Simz,
by delete we mean to erase them from the hosts file. Treat it as a normal text document and just delete them.
Thank you HowtoRemove. Do i save the notepad after i delete the text? It says that i dont have permission to save in this location (Windows > System32 > drivers > etc) and says i need to contact the administrator to obtain permission, or i can save to the documents folder instead. What should I do about that?
Hi Sims,
you should not delete all the text. Only the IPs that are suspicious. Keep us posted for if you need further help.
MacKeeper IS the virus. It said that I had four viruses and there IS NO WAY that a website can scan my computer. https://uploads.disquscdn.com/images/94f25c963b8414f03c86ec2d465bcbeff068bac89ae4681cff8f6c7400f97557.png
Need help. I’m a hacker victim
What is the exact issue you are facing?
Malware Spyware hacked my chrome