This page aims to help you remove Search.mysecurify.com Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Recently, our “How to remove” team has been contacted by a number of users, who have been complaining about a program named Search.mysecurify.com. According to the reports, most of the people don’t know how this program has become part of their system, but they have noticed that Search.mysecurify.com has changed the settings of their main browser and has started to spam their screen with various aggressive ads, banners, pop-ups and redirect links. Most of the users have detected a new search engine or a replacement of the default homepage with another URL. If this has happened to you, then you should know that you might be dealing with yet another representative of the Browser Hijacker family. The Browser Hijackers are pieces of software which, generally, are not malicious and don’t share the harmful characteristics of popular threats such as Viruses, Ransomware or Trojans. Yet, they have the ability to hijack browsers like Chrome, Firefox, Explorer and others, and use them as a platform for aggressive online promotion.
In most cases, programs like Search.mysecurify.com can be a bit difficult to deal with, especially when it comes to their uninstallation. Therefore, even though, we want to note once again that they are not computer threats, you may still need the assistance of a professional removal tool or a manual removal guide to remove them. The good news is that, on this page, you will find everything you need in order to do that. Just make sure you carefully read the information in the next paragraphs and follow the instructions in the Removal Guide below.
What exactly is Search.mysecurify.com Virus?
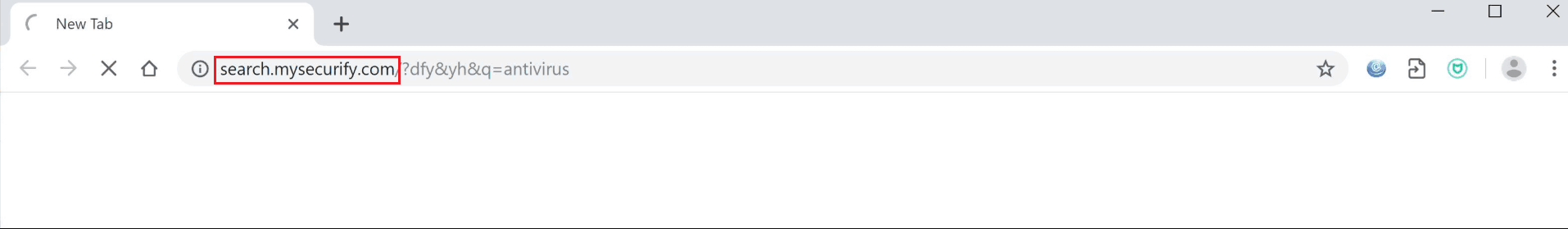
The Search.mysecurify.com Virus will redirect your searches and display Pop-up ads.
The online marketing industry is a big thing and Browser Hijackers like Search.mysecurify.com are just one of the tools the marketers use to promote different products, services and offers on the users’ screen. Still, a common confusion among the people who end up with a program of this kind on their computers is to think they have been infected with a virus. This is because the Hijackers tend to be a bit aggressive in their advertising attempts and typically tend to take over the main browser by introducing some potentially unwanted changes to its homepage or the main search engine. They also tend to mess with the browsing experience by initiating automatic page-redirects to different websites filled with ads, banners, colorful boxes and offers. Such invasion in your web browser can definitely be unpleasant, but, compared to what a real Ransomware cryptovirus can do, is just a mere irritation.
What you may not know, however, is that those popups, banners, and hyperlinks that are constantly thrown at you from every single corner of your monitor are actually all paid advertisements. The software developers, associated with browser hijackers like Search.mysecurify.com, get paid on a pay-per-click basis every time you visit or click to the above-mentioned advertisements. This is how the so-called Pay-Per-Click and Pay-Per-View marketing strategies work.
Now that you know a Browser Hijacker isn’t some dangerous malware, you still may want to remove it for a number of reasons. The constant ads disturbance, the frequent page-redirects, the browser unresponsiveness can all be good ones. Whichever is your reason, feel free to use the Removal Guide below as a starting point to restore your previous browser’s settings.
SUMMARY:
| Name | Search.mysecurify.com |
| Type | Browser Hijacker |
| Detection Tool |
Search.mysecurify.com Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment