TeslaCrypt Overview
READERS! BEGIN HERE, PLEASE! As far as any evidence suggests, TeslaCrypt may just be the most dangerous virus on the internet right now. It certainly is of the most dangerous type at least. Since you are here and I don’t want to waste your time, I just want to give you the heads up – right here, I will be outlining the main problems with this malware, an overview of what you can do to better avoid this situation in the future, and, of course, the removal section dedicated to its eradication. Here are the key things to understand:
- This is a “sister” virus to at least two other known entities: Alpha Crypt and Cryptolocker-V3. They operate in practically the same way, however each uses a different encryption method, so they are listed separately.
- This is extremely important: Do NOT pay the ransom. There are no guarantees your files will be ever unlocked, despite what the message claims. And honestly, there is no way to know that even if your files are returned, TeslaCrypt won’t return for a second round later on – after all, it wasn’t really “removed.”
And the most important:
- Despite what the picture claims, the code generated is not unique for your PC. Do not be fooled. These people are just trying to extort and take advantage of the fact you’re probably not knowledgeable with these things. TeslaCrypt is not special in any particular way. The supposedly unique RSA-2048 key that can not be replaced (at least the message says so) is already researched. In fact, in the removal section below, we will post a link for a TeslaCrypt-specific decryptor that should theoretically restore all your files. Theoretically because there are always newer and updated versions of Ransomware, and there’s no way which one exactly you were infected with.
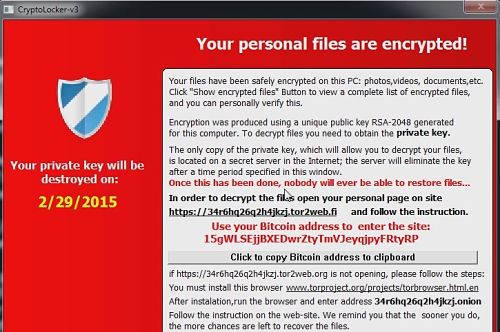
The message itself varies from version to version. In our sample, for which we designed this removal guide, TeslaCrypt displayed the following message with instructions. Please make sure it is the same. If it is not, leave a comment below, and we’ll contact you and try to solve your problem. The personal page that specifies the ransom (usually 500$) is:
- Encryption was made using a unique strongest RSA-2048 public key generated for this computer. To decrypt files you need to acquire the private key.
The only copy of the private key, which will allow you to decrypt your files,is located on a secret TOR
server in the Internet; the server will eliminate the key after a time period specified in this window.
Once this has been done, nobody will ever be able to restore files…
WARNING! TeslaCrypt adds extensions called .ECC and .EXX to your files. If you are seeing extensions with the .EZZ appendix, you are likely suffering from Alpha Crypt, which uses an entirely different method for encryption. Check out our other removal guide for Alpha Crypt.
After it has successfully encrypted your files, TeslaCrypt will create a custom .txt file that should be located on your desktop, together with a wallpaper/picture. These text file is named either HELP_TO_DECRYPT_YOUR_FILES.txt or HELP_RESTORE_FILES.txt while the picture will be called:
HELP_TO_DECRYPT_YOUR_FILES.bmp or HELP_RESTORE_FILES.bmp
How to Remove TeslaCrypt
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

I’ve read your article and it is very informative, you sound like experts on the matter. Am hoping you can help me with my Malware issue. On 5-22-15 my computer was attacked by what I believe to be Teslacrypt Malware, all of my files were encrypted and have a .exx file extension. From what I understand I need a unique decryption key specific to my encryption, but am very stuck as with how to go about the decryption process or how to access/locate this unique decryption key. Am willing to pay the ransom, but at this point, that no longer seems to be an option. Any help you can offer me is greatly appreciated.
I somehow missed your comment. Have you resolved your situation or you still need help? If so, please leave another comment and we’ll think of something to help you.
Thank you for responding to my comment on my malware encryption issue, I missed your reply as well. Have not resolved my situation, but am slowly understanding more about what happened to my files. Any suggestions you have would be greatly appreciated. My email is [email protected]. So hopefully we can communicate easier in the future.
If you can not restore to a previous date, then unfortunately, there is no solution for the encryption – at least for the time being. Researchers are trying to crack the code, but there’s not timetable for when anyone can expect them to succeed.