This page aims to help you remove the Topernews.me Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
What is the Topernews.me Virus?
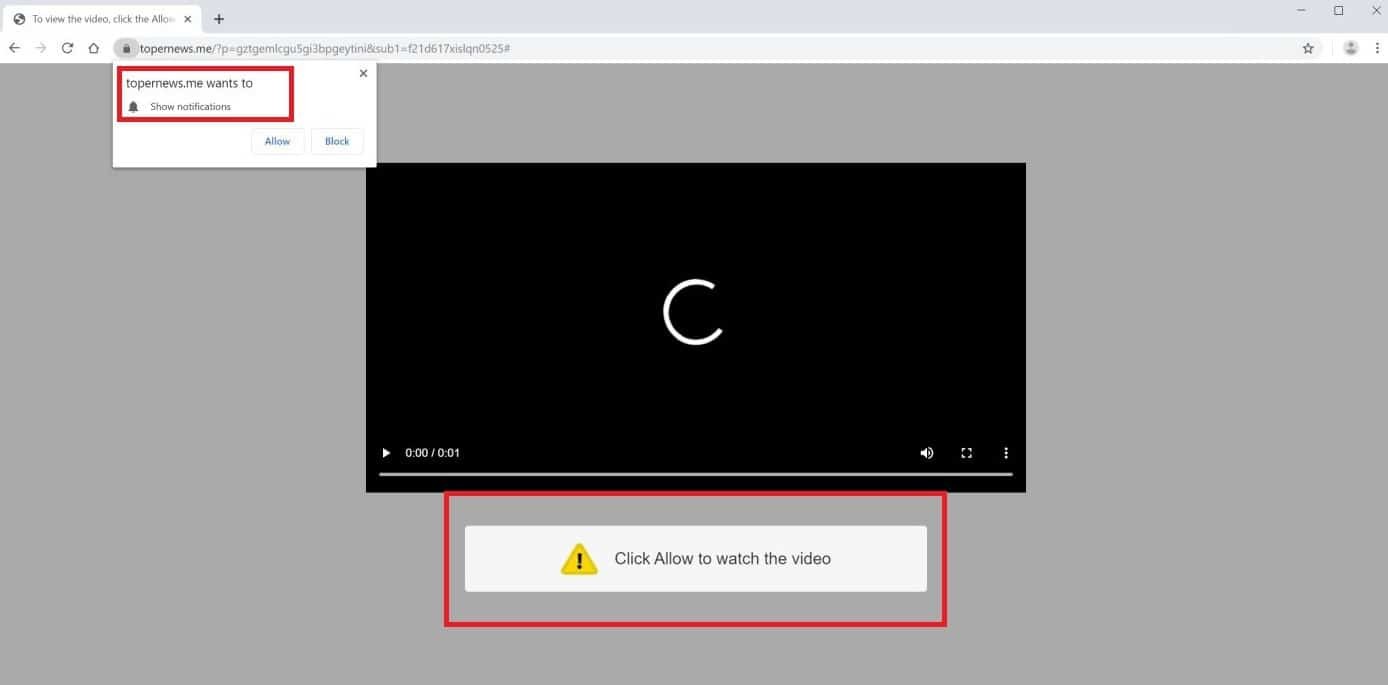
The Topernews.me Virus will display pop up messages and notifications
Maddening promotional messages, ads, pop-ups, and banners that are constantly displayed on your screen are most probably the reason you are reading this page and you should know that they are a result from the effort of a Browser Hijacker program. The main reason why all those advertisements are believed to be a worry is for the reason that they can make it nearly impossible to effectively use your Internet browser. If you’re looking for a way to delete the commercials plus the Hijacker program which is making them, then look no further and simply scroll down to the removal guide section. There you will find instructions on how to remove one recently reported Browser Hijacker, called Topernews.me, which could be the source of your disturbance.
The good news is this type of software is generally not malicious and you have a good chance to safely get rid of it without facing the negative consequences that a real virus (such as Ransomware or Trojan) would leave on your system.
Protection and prevention
There are numerous ways for an ad-generating program like Topernews.me to get on your computer, the majority of which include some type of stealth installation. Probably the most popular strategies are fake links in file-sharing sites, torrents, and the notorious spam e-mails. The winner here is surely the software bundles strategy. Using this strategy, the unwelcome application is bundled with some third-party program which is usually either free or cheap. But software bundles are not always utilized to spread Browser Hijackers. They could also be employed by programmers to market other products made by them, making this technique legitimate. Simply downloading a file that contains a Hijacker isn’t really enough to get your PC in trouble, in most of the cases. The issue occurs when you agree to automatically install that file and give your consent to permit it to customize your machine. Such approval is often received by exploiting the user’s lack of attention during the installation process of the main program. Many people don’t read the small text and the Custom/Advanced settings and are more comfortable with using the Default installation settings which install the entire software bundle. But this is, in fact, what could get you a program like Topernews.me, Total Recipe Search Toolbar, The Goodcaster or other potentially unwanted software by default. If you have recently installed a new program and Topernews.me appeared after its installation, then it is likely you did this mistake as well. This is why file bundling is so widely used – it is possible to give your consent for the installation of all applications put inside a given software package while thinking that you are only going to install just one single program. However, only a little practice is enough for you to learn to opt for the “Advanced” installation settings every time you run a new setup and by doing that you will get familiar with what actually gets installed and will always have control over the programs and additional components that become part of your system. Fortunately, if you skip this option, removing the Browser Hijacker is not really a very difficult task when you know what you’re doing. To understand how to deal with Topernews.me, go ahead and try our removal guide underneath this article or simply use the suggested professional removal tool to get rid of the unwanted program in a few seconds.
SUMMARY:
| Name | Topernews.me |
| Type | Browser Hijacker |
| Detection Tool |
Topernews.me Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment