This page aims to help you remove Topmedia24.me. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
“Topmedia24.me ads”, “Topmedia24.me produced ads”, “Topmedia24.me provided advertisements”, and other similar messages all over your screen could be the primary indications that your computer has been hijacked by an ad-generating software app called Topmedia24.me. A change in the homepage or the default search engine could be some other signs that your Chrome, Firefox or Internet Explorer might have been taken over by this program.
You may also find that it is quite difficult to remove those changes, the advertising messages, the new tabs, and banners no matter what you do. If you already know what we’re talking about, and are annoyed by the activities of this program, we’d suggest uninstalling it. For your convenience, in the manual removal guide below, we have described the exact steps you need to follow to remove the invasive software.
Is Topmedia24.me a danger to your PC?
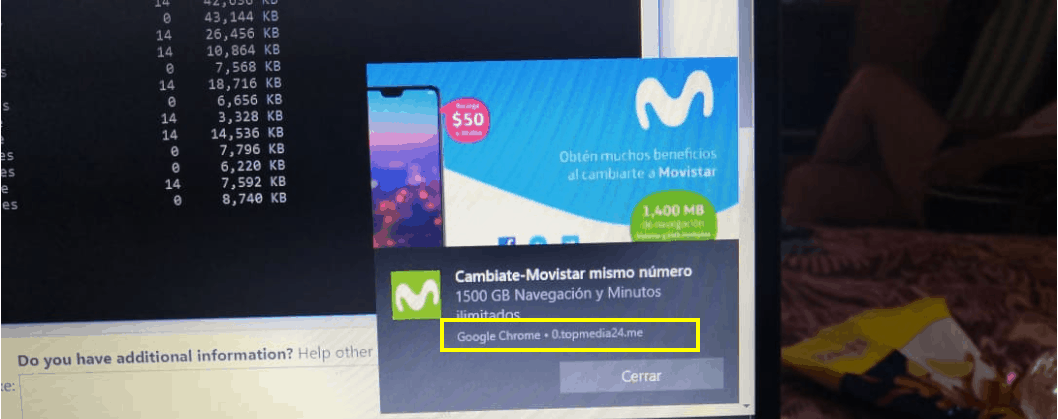
An ad appeared on your desktop and it has been constantly appearing with the address of topmedia24.me
Topmedia24.me is a Browser Hijacker application which does not represent a security threat and operates mainly as an ad-generating and page-redirecting tool. Generally, most of the programs from the Browser Hijacker category are perfectly legitimate, but studies reveal that this is not always the case. In some instances, such programs may accidentally prompt the web users to click on misleading links, or on fake pop-up ads, which may get their systems compromised with some computer infection, such as a Trojan Horse, or a Ransomware cryptovirus.
Therefore, whether you see messages, pop-up advertisements, banners, new tabs, videos or redirect links “Powered by Topmedia24.me” or by another similar program, be careful not to click on them. The main reason their ads, and the homepage/search engine changes related to them aren’t to be trusted is because they may expose you to some aggressive web content that you may not want to interact with.
In fact, due to the invasive activities described above, most of the web users often consider the Browser Hijackers as viruses. However, the Browser Hijackers are NOT hazardous malware and do NOT have the harmful abilities that threats like Trojans, Ransomware, and other harmful computer infections. At their worst, these pieces of software are potentially unwanted programs that produce advertisements to promote content from third parties and receive ad income via the Pay-Per-Click model.
They use some aggressive marketing practices to generate countless advertisements on the users’ screens in order to make pay-per-click profit for their creators. Regardless of whether you think this is a reasonable or somewhat invasive manner of making money through advertising, the fact is that such software does cannot directly cause any severe damage to your computer.
As regular web users, however, we should always have a choice on how to browse the internet, what advertisements to see, or what applications to install on our systems. That’s why, if you feel you’re bothered by this Browser Hijacker and its annoying ads, pop-ups, banners, and constant page-redirects, then you should uninstall the intrusive app.
How to uninstall Topmedia24.me?
There are two basic methods to remove Topmedia24.me, and its components from your computer. One of the options is the professional removal tool, and we highly recommend it if this is the first time you are dealing with such software. However, if you think you can handle the manual instructions from our guide, which is the other removal option, go ahead and give them a try in order to uninstall the pesky hijacker.
SUMMARY:
| Name | Topmedia24.me |
| Type | Browser Hijacker |
| Detection Tool |
Topmedia24.me Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment