What is Total Access Network Scam ?
If annoying ads, banners, and pop-ups brought to you by Total Access Network, Amznsale.info, Amznsale.mobi keep torturing you every time you start your browser, this is the place where you could educate yourself regarding the ways to forever remove this software and its ads. The simple reason why you are seeing these adverts is the direct result of this invasive program’s presence in your laptop or computer, and, in particular, your browser.
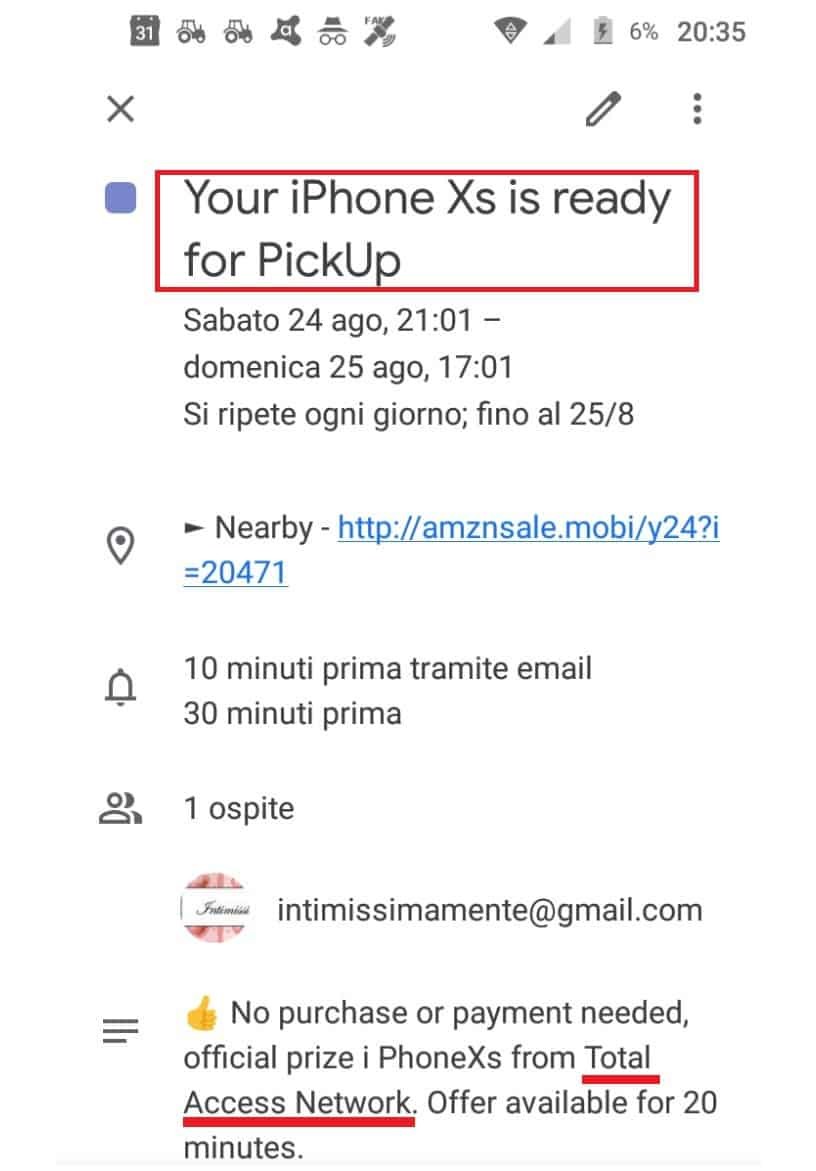
Total Access Network Scam will deceit you that you have won an iPhone
The cyber-security professionals refer to such software as browser hijackers. At the bottom of the article, you will find a detailed removal guide with steps that will show you an easy method to remove Total Access Network and rescue yourself from the aggravating ads.
How not to get any more hijackers installed in your computer
But exactly how did you install Total Access Network? When it comes to distributing that type of software, there are a number of possibilities. One of the most common methods are the junkmail messages that everyone receives from time to time. Torrent files are yet another popular strategy for distributing undesirable software applications of the browser hijacker type. You might open a questionable hyperlink and get sent straight to a website that is contaminated with a browser hijacker. Most frequently, though, Total Access Network gets installed onto people’s machines as part of a program bundle. Software bundles are combinations of applications specifically designed to both install some software for free, but still earn money from the browser hijacker included in them. Often, software developers employ browser hijacker bundles to market their more important programs, while gaining some additional money during this process. Keep in mind that the file-bundling method is actually a legal method for installing all sorts of applications in the users’ systems. It has to be said that in order for the bundled program to get installed onto your system, it does actually need your approval. The “Quick” or the “Default” installation setting is normally the reason why bundled installations are so successful – a lot of people opt for it without having a second though. The end result is that the browser hijacker gets installed in the computer and then it’s up to you to remove it.
Selecting the “Advanced” installation is, therefore, always the more sensible option. The advanced installation should hold all the details in case any unwelcome programs are added inside the file bundle and should present you with the option to leave them out. Understand that it is far better to avoid getting a browser hijacker than to later try to remove it and, for that reason, make a mental note of the tips we have here on how to ward off any potential browser hijackers coming your way. Simple and logical, they can spare you a lot of time afterwards.
One of the most beneficial bits of advice that we can provide you with would be to have a good and reliable security tool, that you update frequently. You might even go for a paid version for some further enhanced protection. Do not forget that your OS also needs regular updates. Acquiring a high quality ad-blocker is another great idea. As with the rest of your software – you must keep that frequently updated too or it may turn into a gateway for unwanted software. Last but not least, the most crucial bit of advice will be to stay away from risky webpages and to only download new programs and apps from sites that are popular, trusted and reliable. Otherwise, if you go to shady sites with low reputation, you may get infected with vicious programs like, for example, viruses and ransomware, so remain cautious when about to download anything from the net. The uninstallation and removal guide below contains all the important steps you need to in order to be able to get rid of Total Access Network.
SUMMARY:
| Name | Total Access Network |
| Type | Browser Hijacker |
| Detection Tool |
Total Access Network Scam Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Omg thanks for ur help. This has been taking over my phone. Greatly appreciated
I have gotten this Verizon survey uptin times, the first time I did it, I paid for the phone on apr 2 is when you took it out of my bank account. I keep getting the message “please confirm your iPhone”. I ‘m not paying for another, haven’t gotten the first one!!!! Send my iPhone.
OMG, i wish i had seen this b4 i fell for that “FREE I PHONE” and paid that $17.43 shipping! im wondering how to CANCEL that $14.00 monthly membership?
Can anyone please help me with this? i dont even see anything about canceling their membership! Of course it says that all you need to do is go to their Support@totalaccess[.]network to do this….please help??
They got me too and I’m looking for a way to communicate with this site..Nothing! Please help?
Hi sam, did you try following the removal guide?
How do I get my phone without paying for the tv services. $1 I already have a bundle service
Hi Becky, if you are seeing messages from Total Access Network you should try following the steps at the bottom of the article.