This page aims to help you remove Track.nuxues.com “Virus”. Our removal instructions work for Firefox,Chrome and Internet Explorer, as well as every version of Windows.
If you scrolling trough the Windows News App, each new page load – and with that loading of payed Advertisement, opens up scam/pishing sites.
The Track Nuxues Virus
The track nuxues virus is a rogue site categorized as a browser hijacker by major AV companies. It displays all the hallmarks of browser hijacker virus – redirects that lead to shady landing pages.
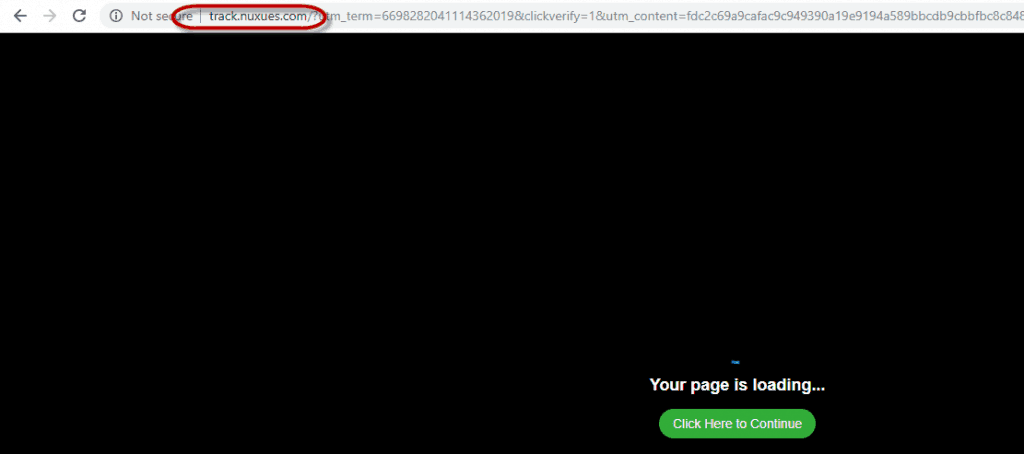
The landing page the track.nuxues.com virus leads to.
After a few seconds, the redirect proceeds to another website (note that this can change in a few days), currently Mobsu.net. The pages Track.nuxues.com redirects to seem to be language and location specific
Irritating ads invading your monitor? Track.nuxues.com “Virus” is probably what’s triggering them. You would likely want to know where these emerging ads originated from and why your browser sends you to unknown marketing webpages as you’re searching for something else entirely. Computer experts label products similar to Track.nuxues.com as Browser Hijackers. Under this brief article, we have given our guests an in-depth guide that will help you do something about the intrusive software program.
Is this some sort of a malware infection?
Whenever people run into Browser Hijackers, they tend to inaccurately believe their device has been attacked by a virus. However, this is actually not really the case – computer viruses are malevolent pieces of coding built for an exact job – for instance, spying, data annihilation and more. Ransomware is a type of destructive computer viruses we can use as an example. A Ransomware will lock all private documents in a computer and blackmail its user for ransom money for the files’ liberation. When compared to a Ransomware or a Trojan, a Browser Hijacker is more irritating than dangerous and if you use the proper instructions, it should actually be rather easy to remove it with no downsides.
We outlined the distinctions between computer viruses and Browser Hijackers to make our subscribers better understand the characteristics of Track.nuxues.com. Nonetheless, it is still better to not allow a hijacker to freely operate in your system.
Regrettably, the law states that any program that will not carry out criminal activities is not malicious and no matter how annoying it is, it wouldn’t be forbidden or deemed illegal. This is certainly the loophole Browser Hijackers exploits to prosper.
Security in the future
Understanding how to protect your PC from getting “attacked” by Track.nuxues.com is vital. If you know how to recognize unsafe websites, torrents and unreliable pieces of software, you’ll have the most effective protection for your machine.
Probably, the most prevalent method via which Browser Hijacker applications are spread continues to be the file bundles. This means that when customers get a computer software they would like to install, they could get a Browser Hijacker which is bundled in the installation as a “bonus” element. The Browser Hijacker may be concealed in the advanced/custom options menu in the setup wizard. The primary reason why this strategy succeeds is simply because almost all customers choose the quick installation that installs any added/bonus (and likely undesirable) programs by default. It is therefore a good idea to visit the EULA before deciding to install any new software. Of course, as this is a very boring activity, just select the advanced settings and in there find out if any questionable programs have been included. In the advanced settings, you are able to choose to leave out of your computer system everything that appears to be suspicious or shady by simply unchecking it. By doing this, you could certainly save yourself a great deal of time that you would have certainly otherwise spent on seeking ways to eliminate the Browser Hijacker. Our last piece of advice for you would be to get programs exclusively from sites that are trustworthy and honest, while avoiding any dubious or questionable ones.
SUMMARY:
| Name | Track.nuxues.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Track.nuxues.com Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

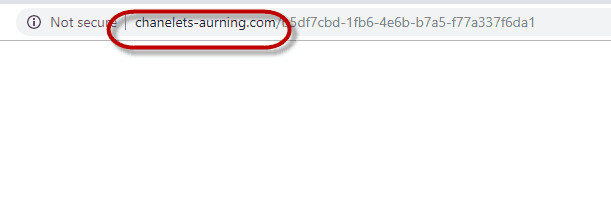

Just a few websites forward me to nuxues. Why not every website? What triggers chanelets-aurning? Have these sites been infected?
Looking forward to your reply.
Kind regards,
Jan
Have you completed the instructions from the guide? This may help you deal with the annoyance.