Trojan.Multi.GenAutorunTask.a
Trojan.Multi.GenAutorunTask.a is a dangerous piece of computer malware that can cause different types of damage in the infected system and in the user’s virtual security. Although many users refer to Trojan.Multi.GenAutorunTask.a threat as virus, the fact is that a computer virus and a Trojan Horse are two different things because, unlike the viruses, the Trojans do not normally replicate themselves inside the infected system.
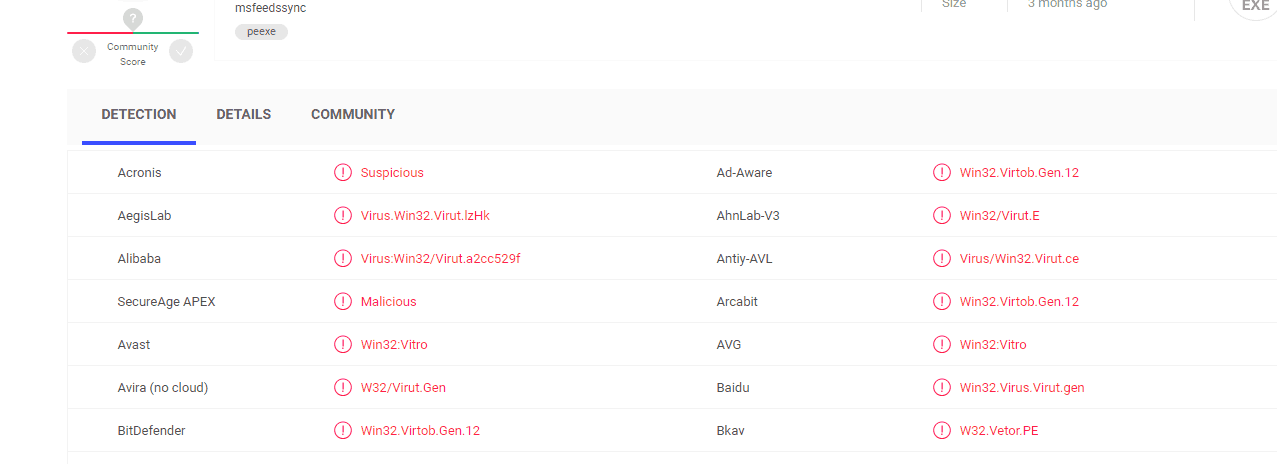
VirusTotal report shows that many anti virus programs detect the Trojan.Multi.GenAutorunTask.a virus
This, however, certainly doesn’t take anything away from their ability to cause harm. In fact, the representatives of this malicious software category are among the most problematic and also the most versatile forms of computer malware you could get your computer infected with.
In the present article, we will mainly be focusing on Trojan.Multi.GenAutorunTask.a, which is a new malicious program that has been categorized as a Trojan. Our goal is to inform our readers about the most important characteristics of this threat, and to offer those of them who have already gotten their systems infected a reliable solution that would allow them to remove the insidious infection.
What can be expected from a Trojan.Multi.GenAutorunTask.a infection?
As mentioned earlier, the Trojans are highly versatile threats, and due to that it is oftentimes difficult to determine their exact goal. In many cases, the malware would be silently operating in the system without showing any signs of its presence and its end goal would remain a mystery even to those who have somehow spotted the infection. Regardless of the goal of the Trojan, however, it is crucial tat the infection gets removed immediately, so as to prevent it from causing any more damage than it already has.
Still, to give you an idea of what you may be facing if Trojan.Multi.GenAutorunTask.a is present in your system, here are several examples of what such a virus may be able to accomplish.
Trojans are oftentimes used to take over the computer, and force it to conduct tasks that haven’t been approved by the user. Such tasks could be the unauthorized distribution of spam letters that contain the Trojan or some other harmful program (such as a Ransomware cryptovirus), the carrying out of Denial of Service attacks targeted at popular sites, the mining of cyber currencies such as BitCoin, that get directly sent to the hacker’s online wallets, and more.
Oftentimes, the Trojan is actually a secondary tool used to deliver the primary infection to the attacked computer. In this case, the Trojan is called a backdoor, and the threat that it carries is oftentimes a Ransomware cryptovirus – a malicious piece of malware that locks the user’s files or screen, and keeps them that way until the victim pays a ransom to the hackers.
Trojans are also known as advanced espionage tools. They may gather sensitive information about you and use that to blackmail and harass you. And should an infection like Trojan.Multi.GenAutorunTask.a acquire your debit or credit card numbers, the hackers behind the malware would most definitely drain your banking accounts without you realizing anything before it’s too late.
SUMMARY:
| Name | Trojan.Multi.GenAutorunTask.a |
| Type | Trojan |
| Detection Tool |
Trojan.Multi.GenAutorunTask.a Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment