The WebHelper Virus
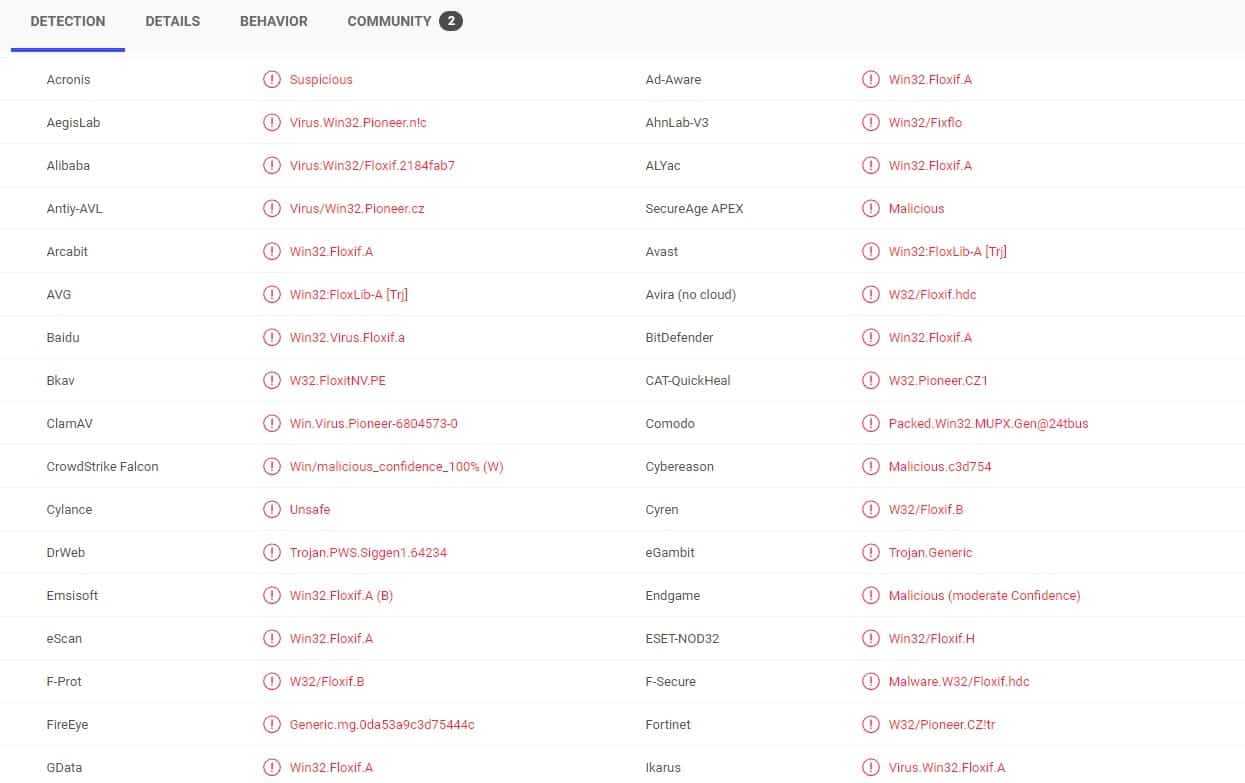
Multiple anti virus programs detect the WebHelper virus
There are probably not many computer users who haven’t heard about the nefarious Trojan Horse infections. After all, the infamous Trojan Horses are one of the most commonly encountered, as well as some of the most damaging malware programs one could get inside their system. A new example of a dangerous Trojan Horse virus is the newly detected WebHelper, which is going to be the focus of the next few paragraphs. Here, you are about to learn some basic information about this malicious software piece, and you will also find out how you can potentially deal with it in case it has entered your computer.
The WebHelper Trojan Horse is a sneaky piece of malware that can come to you disguised as something that doesn’t raise suspicion, and, better yet, that seems interesting to you, so that you’d be enticed into interacting with it. A common example is when Trojans like WebHelper are presented to the user under the guise of a program or a game installer. Of course, you wouldn’t download such an installer from the official site of the software that is used as disguise, which is why most installers that are hidden Trojans typically come from sketchy sites, known for spreading illegal and pirated software. On the outside, however, the installation .exe file would likely look pretty normal, leading the user to interact with it. Upon opening the infected file, the victim would probably be asked to provide their Admin permission to the file, allowing it to make changes in the system. Should the user give their permission, the Trojan would immediately get activated and would get down to business. What’s even worse is that it would now have Admin privileges, meaning that to would be able to access, and modify nearly all system settings, software, and data on the computer. Naturally, this would allow the hackers behind the virus to do all kinds of things within the attacked system. What happens next depends on what the cyber criminals are after, and what their end goal is.
Possible consequences of the WebHelper attack
Due to lack of sufficient research, and because the virus is quite new, we can’t tell you the exact type of harm that WebHelper may cause. Such Trojans are known for their unpredictability, and their versatile abilities, so you could expect anything from them. From personal espionage and attempts to acquire some sensitive data, such as banking numbers, to making use of your computer’s RAM, CPU, and GPU for cryptocurrency mining, from personal harassment and blackmailing, to insertion of more malware such as Spyware, Rootkits, and Ransomware cryptoviruses, a Trojan Horse could cause damage and harm to your computer, and to your virtual privacy in a number of ways. The important thing, however, is to never wait for the damage to become apparent. You should always seek to stop the malware program in its tracks, before it has managed to cause anything serious. Hopefully, with the help of the guide and the professional system security program below, you should be able to take care of the infection with as little harm caused as possible.
SUMMARY:
| Name | WebHelper |
| Type | Trojan |
| Detection Tool |
Remove WebHelper Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment