Ecleneue Virus
Ecleneue Virus is part of an advertising scheme used by website owners for additional revenue. Adware products inject pop up advertisements on website you visit with the aim of generating revenue. Many computer users are careless or at least not very considerate with regards to the sites that they visit and the things they download from them.
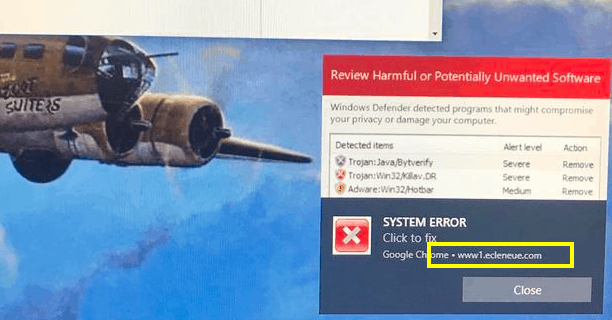
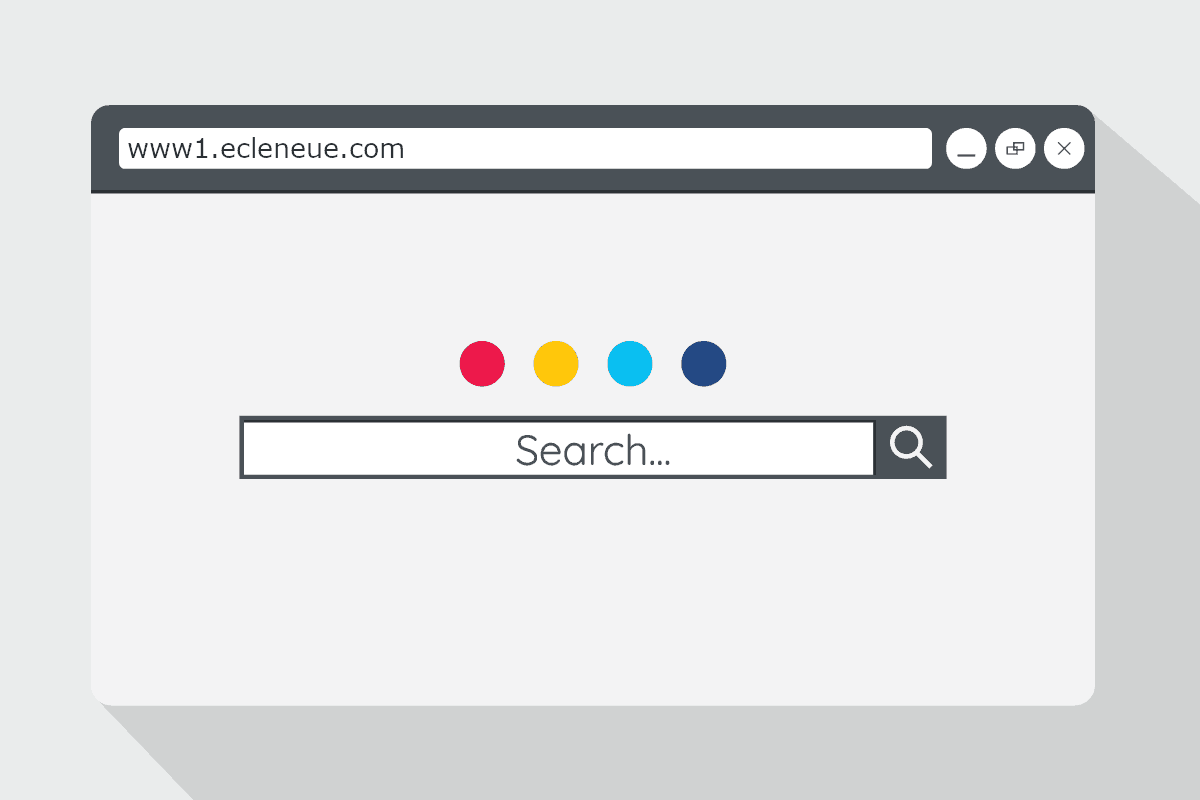
This is oftentimes the main cause behind Ransomware and Trojan Horse infections as well as infections with other insidious malware programs. However, even less dangerous software such as the browser hijackers can land inside the computer if the user isn’t cautious on the Internet and if they download software from unreliable sources. One browser hijacker that we’ve recently learned about is the so-called Www1.ecleneue.com Virus and it is an app capable of changing the search engine of the main browser in the computer as well as imposing a new homepage on it. The purpose of those changes, however, isn’t to help the users but to allow the hijacker t issue intrusive ad-generation and page-redirects. Chrome, Firefox, Safari, Edge and other popular browsers can all get affected by applications like ecleneue Virus – it doesn’t matter how advanced and secure the browsers is.
Ecleneue Remove
How to remove Ecleneue ? Here is a quick tip:
- To remove Ecleneue from Chrome go to Settings (upper right of the Chrome browser).
- Then go to Extensions. Look for Ecleneue and any other suspicious extensions.
- Remove Ecleneue and other suspicious extensions by clicking the remove button.
- Now go back to Settings.
- Make sure that Search Engine and Default browser are the ones you want.
One of the reasons why the hijacker apps are so effective is precisely because they are not illegal and malicious viruses. Even though they are still widely regarded as unwanted software, there is a distinct difference between malware the likes of Spyware, Trojans and Ransomware, on the one hand, and browser hijackers, such as Searchmine.net on the other hand. However, if Www1.ecleneue.com is in your computer right now, we assume that you want it uninstalled ASAP and seeing as how you are currently reading this article, it’s likely that you haven’t been able to remove the invasive app yourself. This is hardly surprising – the hijackers are known for their ability to remain on the system and be difficult to remove through regular means. We, however, can help you with this situation as long as you give a try to the guide for removing Www1.ecleneue.com which you will see further down this page. Just make sure that you execute each step exactly as it’s explained and that you consult us via the comments section in case you have any doubts regarding what to do at any particular step. It’s really important not to accidentally delete something that is not related to Www1.ecleneue.com “Virus” or else you may cause more complications to your system.
What you must know in order to not get more hijackers installed inside your computer system
The most important thing to understand about the browser hijacker distribution methods is that you don’t really need to be visiting any sketchy sites or to be downloading illegally distributed software in order to land such an app. As we already mentioned, this form of software isn’t really malware and could get distributed through regular means such as file-bundling. This is, in fact, one of the most common ways in which browser hijacker software gets distributed. The app gets bundled with a software installer that carries some main program which is the one that the users would be typically interested in. However, if the default setup settings are chosen and the installation configuration isn’t customized, the bundled hijacker would likely get installed in the system by default, alongside the main program.
SUMMARY:
| Name | Www1.ecleneue.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Www1.ecleneue.com Virus Pop ups
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

THANK YOU SO MUCH!! you have no idea how much this has helped me. thank you again, you’re a lifesaver!! <3