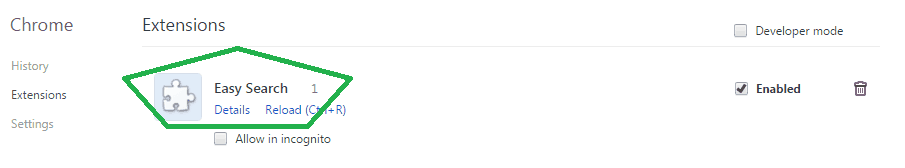
This article aims to assist you with removing Easy Search. These malware removal instructions are applicable for Chrome, Firefox and Internet Explorer. “Como desinstalar easy search” and “Remover easy search” are the two most popular phrases we were just flooded with by people who need help, signifying this threat is spread outside of english-speaking nations. The easy search “utility” is a malicious redirect that has one one thing on its sights: to manipulate scared users into either installing fake anti-virus software that takes your money, or to log in your credentials and steal any personal information and credit cards it can. Our personal goal here is to help anyone in trouble and assist with “Como desinstalar easy search” and “Remover easy search.” Our removal instructions do not requite any specific knowledge or software to be used.
PLEASE, READ THIS PART!
This content will help you to understand how dangerous the virus is; how to see it; and how it got introduced to your computer. Easy Search is considered as a regular computer program by many. In fact, these ‘many people’ don’t realize how catastrophic it could be. Because it has been wrongly ranked, most of the population around the globe today can’t even explain if they have gotten the virus on their computer until one day, but that day might come too late. Continue to read this article and you will be pleasantly surprised of how easy it is to spot the virus on time and that it is not at all difficult, even for the least tech-savvy folks out there, to remove it ON THEIR OWN, without paying crazy money to IT specialists.
How dangerous is Easy Search and how to recognize it?
The virus could be fatal in many ways. It appears in the form of advertisements, which is its famous mask. It is true that there are so many ads out there in the cyberspace that it is hard to carefully review them all and complicate to figure out which ones are real and which ones are not. However, any excessive amount of pop-up ads, flashing text boxes, banners that quickly show and hide are signs of Easy Search.
When your computer becomes poisoned with the malware you will quickly observe major slowness in its overall functioning. It could take hours for it to start, reboot or it may just get stuck and kind of freeze. Just imagine a person struggling with a couple viruses, well it will be the same situation with your computer — obvious and hard to deal with.
We suggest that you don’t underestimate even for a minute the affect that Easy Search could have. Hackers are gifted and really well taught on how to ‘get’ many devices simultaneously. If you are one of those unlucky people out there, they will want to take out as much personal information about you as possible. That would include, but not be limited to dates of birth, addresses (current and past), phone numbers, bank accounts, even browsing habits and most frequently visited internet sites AND access to your social media channels–very common now days to see your Facebook account, for instance, blocked by a ‘programmer’. They could use the last to distribute more malicious information and infect your friends or use your name and account for other illegal purposes, such as distributing inappropriate content. They could take advantage of your most precious data for identity theft purposes, laundering of money, illegal oversea wiring transfers are just a few of their bad intentions. We believe that you are here reading this article because you or someone you know has met with Easy Search, so we advise you to turn to the removal guide on the bottom of this article for detailed info on how to get rid of the malware!
How did Easy Search arrive to your PC?
There are as many active ways that could happen, which are not only theories, but a REALITY! Some of the tested and experienced methods include (this is not a full list):
- Software Bundling: you attempt to download a certain file, but you don’t notice the additional files attached to it. These are usually infected and spread the disease into your system quickly.
- Spam e-mail messages from advertising companies.
- Phishing e-mails: fake e-mails pretending to be sent by your friends.
- Clicking on some or even one of the pop-up ads mentioned above
- Through a social media account of one of your friends that has been hacked
There are many ways the virus could be spread, but the steps for removing it are the same: uninstalling, rebooting and scanning every single file you download from now on
SUMMARY:
| Name | Easy Search |
| Type | Browser Hijacker |
| Detection Tool | Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. Sponsored |
Easy Search Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply