*Source of claim SH can remove it.
RestMinder
RestMinder is a potentially unwanted software utility that reminds the user to take breaks from their PC screen but also performs some questionable activities. RestMinder is known for using system resources and gathering system data during breaks, and it can also make unwanted browser changes.
While the primary RestMinder function of reminding you to take breaks from your computer’s screen can be helpful and beneficial to you, the potential downsides that come with having this app in your system shouldn’t be overlooked. Different cyber-security researchers and companies have detected questionable activities coming from this app that has led to it being categorized as a PUP (potentially unwanted program) and/or as a browser hijacker.
Some of the reasons you might be better off finding an alternative to RestMinder are that it can use your system resources (including cellular data) during your screen breaks, gather data from your computer, and introduce changes to the browser that can interrupt your normal online experience.
What is RestMinder?
RestMinder is a utility app that reminds you to take screen breaks, but it is regarded as potentially unwanted because it’s known to perform other actions in the system without user permission. RestMinder can gather user data, hijack your browsers, and exploit system resources.
One of the more noticeable problems with RestMinder is that some of its versions may take over your main browsers or even all browsers on the computer and make changes to their homepage and default search engine. RestMinder may also cause your browsers to frequently page-redirect you or to display intrusive notifications and pop-ups on your screen.
In addition to the negative effects that RestMinder may have on your browsers, this potentially unwanted software can also gather data from the browsers and from your system and then send it to online advertisers without your permission. Types of data that can be gathered by RestMinder are the IP address of the device, its geolocation, current charging state, network status, last time seen online, and more. Admittedly, the knowledge about the data-gathering activities of RestMinder isn’t kept from the user – you can read all about it in the Privacy Policy section on the app’s site. However, this doesn’t take away from the fact that RestMinder is capable of collecting a lot of types of data from your computer and there’s hardly anything you could do about it other than have the program uninstalled.
Furthermore, while you are taking a break from your PC, RestMinder uses the opportunity to use some of your system and Internet resources to gather data from public Internet resources. Basically, during the 5-minute period users are away from their PCs while taking the recommended break, their computers are working for RestMinder’s owners. Again, this information isn’t kept from the user, but you’d need to specifically read the Terms and Conditions/Privacy Policy section on the RestMinder site to become aware of it.
Is RestMinder a malware virus?
RestMinder is not a malware virus – even though the program is commonly considered potentially unwanted, it is unlikely to cause any damage to the system it’s installed on. However, though RestMinder isn’t a virus, it’s still recommended that it gets uninstalled.
As mentioned before, some versions of the app can affect the users’ browsers, making unwanted changes in them and causing them to display obstructive advertising content. While, for the most part, this type of behavior would be more annoying than harmful, it’s still important for the safety of your system that you keep our browsers clean from any third-party elements that can cause sudden redirects to unknown sites or spam obstructive notifications and pop-ups on your screen. There’s simply no guarantee that the content you get exposed to in this way is safe, which is why it’s necessary that you get rid of the software that’s causing triggering this.
RestMinder version 1.0.0.1
RestMinder version 1.0.0.1 is a potentially unwanted app that functions as a reminder utility for taking breaks away from your screen. RestMinder version 1.0.0.1 isn’t harmful but can cause aggressive browser redirects and can exploit the resources of your system.
The app itself is unlikely to cause any sort of direct harm to your computer or to any of the data you keep stored on it. However, its use of your system data can lead to undesired slow-downs and other performance issues, and its changes in the browser and the potential page redirects it may cause could lead to you getting exposed to online scams and even sites used for malware distribution.
SUMMARY:
| Name | RestMinder |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How to Remove RestMinder
To remove the RestMinder virus, clean your computer from potentially malicious programs, quit any Trojan Horse processes that may be running, and restore any system settings that have been modified without your approval.
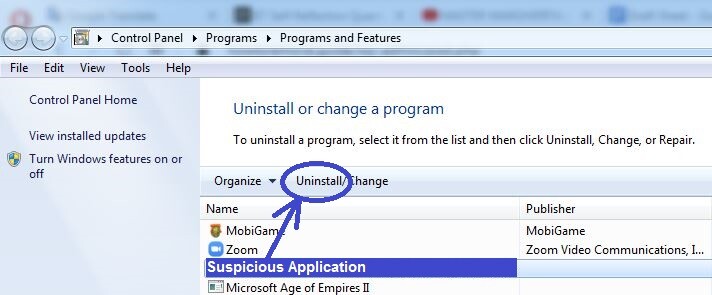
- Use the Programs and Features list to find and delete any questionable programs that are present on your PC.
- Disable suspicious processes in the Task Manager.
- Clean the Startup items and the Hosts file from rogue entries, and also reset the DNS settings.
- To remove the RestMinder virus, clean your system’s Registry from items that the virus has added there.
These four steps provide a summary of the cleaning process that you must complete in order to get rid of RestMinder. For further details on how to perform each of the steps, please, read on.
Extended Guide
We always tell our readers to bookmark the webpage of the guide or to have it open on their smartphone before they start completing the removal steps. System restarts will be required during the guide and if you have bookmarked the page or have opened it on another device, this will make the whole process easier, as you won’t have to search for this page all over again.
Step 1
Trojan threats like RestMinder are often known to get distributed with the help of free and seemingly harmless programs or apps. Therefore, if you have recently downloaded any software on your computer that was free and/or was downloaded from a suspicious source, it’s possible that this software was the cause of the Trojan Horse infection.
For that reason, we suggest that the first thing you do is go to Control Panel > Programs > Programs and Features and check the list of program installs for any questionable entries (especially ones installed not long before the Trojan started showing its symptoms). In case you find anything that you think may be a threat, select it from the list, select the Uninstall option, and complete the uninstallation process by following the on-screen steps shown in the uninstallation manager.
Here, it is very important to make sure that you do not allow the uninstaller to keep any of the programs data on your computer! If the uninstaller asks whether you’d like to keep any personalized settings for the program you are trying to delete, do not agree to that, and perform the uninstallation in full.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Search for the Task Manager tool in the Start menu and open it, then click on its second tab (the Processes one), and search the listed items for ones that seem linked to the virus. We suggest sorting the list by the amount of CPU or memory used by each process so that you’d see the ones that are consuming the most resources at the top. This is because most malware processes require large amounts of processing power and RAM (virtual memory) to function and so it is likely that the RestMinder process would also be using up a lot of resources.
See if you can find an unfamiliar or suspicious-looking process that is also resource-intensive and look up its name. In most cases, if the process is malicious, this will come up in the search results as there would probably be posts from other users or even security experts that warn about that process. If this turns out to be the case, right-click the process in the Task Manager and click on the first option (Open File Location).
All the files in the following folder must be scanned for malware – we recommend using the following free online scanner for the scan of the process files.


If malicious code is found to be present within any of the scanned files, this means that you should quit the rogue process and then delete all of its data. To disable the process, simply right-click it again and then select the End Process button. After that, delete the files from their location folder, but not it is possible that some of the files cannot be deleted at the moment. It’s okay if that happens – simply carry on with the guide and complete it. Once it is finished, try to delete the entire file location folder of the rogue process.
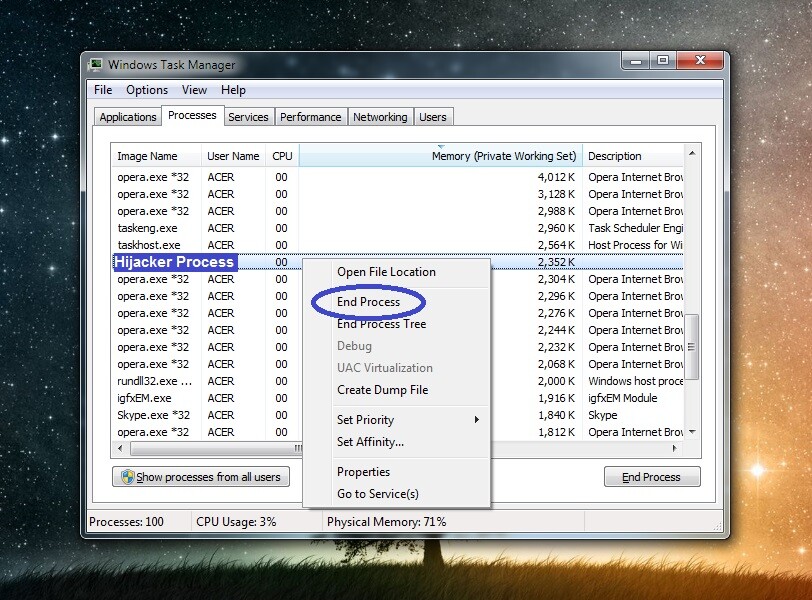
Note: If the opinions and posts you’ve read online about the suspected process are conclusive about the process’ malicious nature, you should stop that process and get rid of its files even if none of the said files get detected as threats when you scan them.
Step 3
Put your computer into Safe Mode to stop the malware from restarting its processes and hindering the completion of the next steps – the linked page will bring you to a guide that will help you with entering Safe Mode.
Step 4
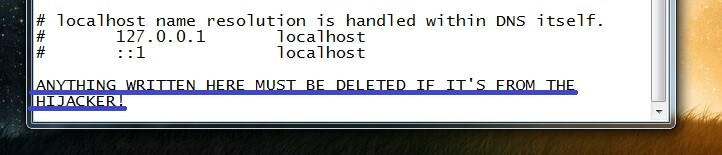
Press together the Windows key (the one with the Windows Logo) and the R key, and then paste this line “%windir%/system32/Drivers/etc/hosts” in the newly-opened Run window.
Hit Enter and select Notepad if you are required to choose a program with which to open the file. When the Hosts file shows up, have a look at the text in it, focusing on what’s at the end of the text. If the file hasn’t been modified by RestMinder, the last thing written in it should be “Localhost”. If anything is written after that, you need to copy it, paste it in the comments below this post, and wait for our reply. We will soon tell you if the text from your Hosts file is related to the virus and whether you’d have to delete it from the file.
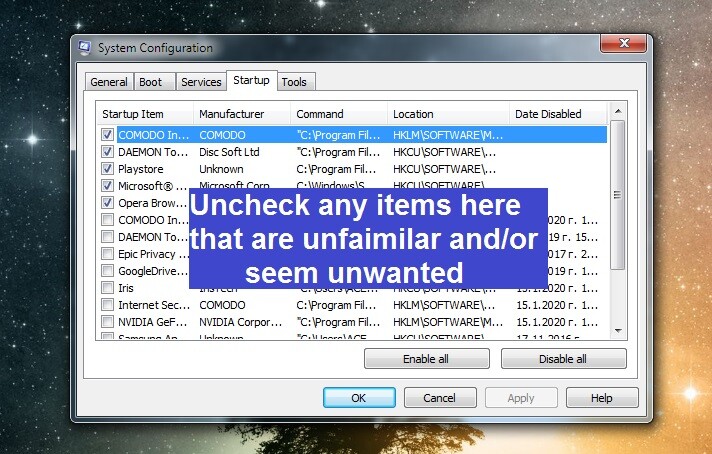
Use Run again by typing in it msconfig and hitting Enter. This will open the System Configuration settings – there, you must visit the Startup tab, check it for suspicious or unknown programs or apps, and disable the ones you don’t think you can trust. After that, click on OK so that the changes to the Startup items are saved.
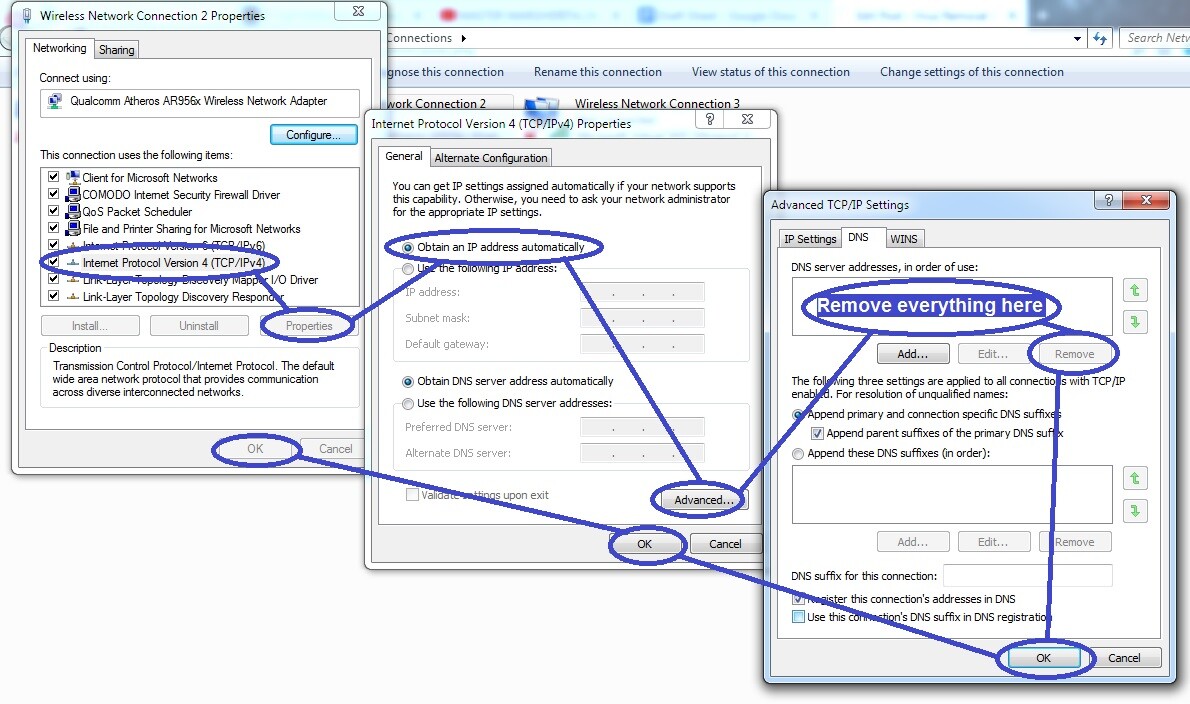
The final thing you need to do in this step is type ncpa.cpl in the Run window, click OK, then find the network your computer is connected to from the ones listed in the newly-opened window, and right-click on its icon (the network that you are connected to will be the only one without an X in its icon).
Open the Properties of your network, click on Internet Protocol Version 4 (find it in the list), and select the next button that’s labeled Properties. In the following window, check these two options if they aren’t already checked:
- Obtain an IP address automatically
- Obtain DNS server automatically
Next, click on the Advanced button, open the DNS section and, if there are any IPs listed in the list, remove them, after which click OK on each open window.
Step 5
Be warned that while completing this step, you must be extremely cautious – do not delete any items you aren’t certain are from the virus. Otherwise, you may cause further problems for the system. When in doubt, our advice is to contact our team by writing us a comment down below and wait for our reply before you perform the deletion.
Access the Registry Editor of your system by typing regedit in the Run window (see the previous step), clicking on OK, and then select Yes (if asked for permission to run the program).
When in the Registry Editor, evoke the search box by pressing Ctrl and F and type the virus’ name (RestMinder). Select Find Next to initiate the search. Only the first related item will be shown (if there are any items for that search) – you must delete it and search again. The goal is to eventually delete all items that are linked to RestMinder.

One other thing that needs to be done in the Registry is to check the locations we’ve listed below for questionable items with long and random names. For instance, if you see an item with a name like this: “f049th2409tu50hy309u4itgj094“, you should most probably delete it since it may be linked to the virus. To reach the locations that you need to check, simply expand the folders to the left until you find them.
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Step 6
If the problem with RestMinder persists even after you’ve done everything from the guide, you may need to use the help of a specialized program that will clean the computer for you. You can find such a tool on this page – it’s powerful deep-scanning abilities will find every last bit of data related to the Trojan and eliminate it while also ensuring that the virus doesn’t return in the future. Often, the manual removal of a Trojan could be way too difficult to complete by regular users and so eliminating the threat with the help of a professional anti-malware tool may be the safest option in such situations.

Leave a Comment