Rootiunik
Rootiunik is a Ransomware cryptovirus that people with malicious intentions use to encrypt user files. Rootiunik is designed as an extortion threat that targets different devices, prevents the owners from accessing their files and asking a ransom payment for providing a decryption key.
Ransomware infections like this one will typically rob you of the digital information that you need the most by encrypting it with a nearly unbreakable algorithm. If you ever want to access your encrypted information again, you will be required to pay a ransom to the hackers who control the infection. Rootiunik in particular is one of the latest variants of the ransomware class and what you can expect from it is to secretly encrypt the files on the victims’ computer and then force them to pay a rescue fee for decryption of the data in the form of a ransom. Since you landed on this article, however, we presume that you don’t want to pay anything to the hackers behind Rootiunik and are ready to try some other options to remove the infection and deal with its consequences. That is why, irrespective of what you intend to do in the future, we have published an extensive removal guide which we strongly recommend you have a look at. The guide provides guidance on how Rootiunik can be safely removed from the infected computer and some tips for recovering encrypted files without paying a ransom.
The Rootiunik Ransomware
The Rootiunik ransomware is an online infection of the cryptovirus class that seeks to block access to different digital files. Most often, the Rootiunik ransomware is aimed at the victim’s documents, file archives, images, audios, videos, databases and system records that are vital for the operation of the machine.

The primary concern regarding these widely distributed and troublesome Ransomware viruses is that even a strong antivirus will most times fail to protect you in time from such a threat. The thing is that even if you have a strong and reliable antivirus program installed on your computer, the Ransomware attack could pass under its radar for a simple reason – the encryption that is applied to your files is not actually harmful and does not destroy or in any way damage the information it locks. By default, file encryption is a common data protection method that is used to keep sensitive digital information away from unauthorized access and finds implementation in sectors like banking, online shopping, online payments, public institutions and more. The problem is that the same technique is used by threats like Rootiunik, Wrui, Cadq to restrict users of access to their own information by keeping the decryption key in secret and demanding a ransom in exchange for sending it to the victims. After the attack, the ransomware virus will typically display a ransom note on the screen of the infected computer where the crooks will ask you to pay a fixed amount of money in order to obtain a file decryption key from them. Unfortunately, even if you choose to pay the hackers, the future of your files is generally uncertain since the crooks may not give you the key intended for the the decryption.
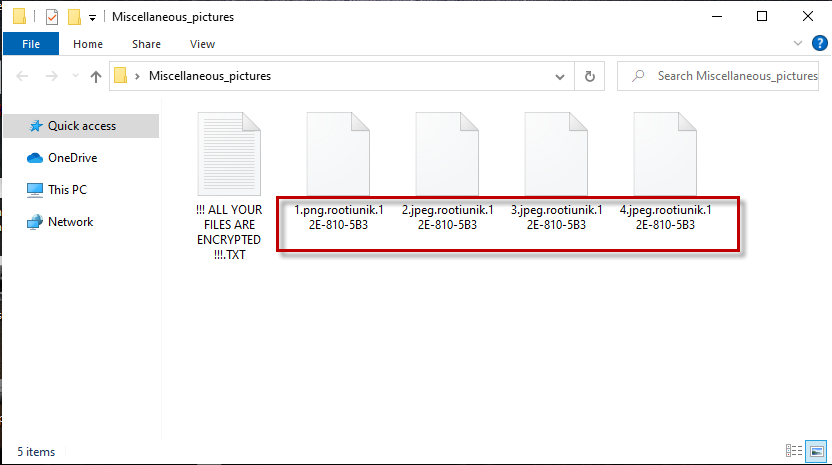
The Rootiunik file encryption
The Rootiunik file encryption is a malicious process that is activated as soon as the device is infected with the Ransomware. To reverse the Rootiunik file encryption that has been applied to their files, the victims are asked to pay a ransom fee to anonymous cyber crooks.
Checking out the alternatives available to save some of your files and your computer without paying a ransom is a good idea and you should definitely do so before you decide to transfer your money to the hackers. The removal guide below, for instance, can provide you with support in having Rootiunik removed and retrieving data from systems backups and it will cost you nothing to give it a try.
SUMMARY:
| Name | Rootiunik |
| Type | Ransomware |
| Data Recovery Tool | Not Avalable |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Rootiunik Ransomware Virus Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Rootiunik files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply