RSA-4096
This page aims to help you remove the RSA-4096 Virus and its encryption. These RSA-4096 Virus removal instructions work for all versions of Windows. The “all of your files were protected by a strong encryption with rsa-4096” message that accompanies the virus is what gives it its name.
Ransomware viruses are among the nastiest types of threats your computer is exposed to. This particular branch of viruses focus on encrypting the users data and making it unreadable. A payment is demanded for the code needed to recover this data. Ransomware viruses are not new – the first reported samples date back to the nineties, but they have become hugely popular with criminals due to the fact that many people prefer to pay the money instead of finding a safe and free solution.
All Of Your Files Were Protected By A Strong Encryption With RSA-4096
Readers have lately been recorded to receive the following when their PC boots, dubbed as the “all of your files were protected by a strong encryption with rsa-4096” message:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
NOT YOUR LANGUAGE? USE https://translate.google.com
What happened to your files ?
All of your files were protected by a strong encryption with RSA-4096.
More information about the encryption keys using RSA-4096 can be found here: http://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen ?
!!! Specially for your PC was generated personal RSA-4096 KEY, both public and private.
!!! ALL YOUR FILES were encrypted with the public key, which has been transferred to your computer via the Internet.
Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server.
What do I do ?
So, there are two ways you can choose: wait for a miracle and get your price doubled, or start obtaining BTC NOW, and restore your data easy way.
If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment.
For more specific instructions, please visit your personal home page, there are a few different addresses pointing to your page below:
<Removed>
If for some reasons the addresses are not available, follow these steps:
1. Download and install<Removed>
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar:<Removed>
4. Follow the instructions on the site.
IMPORTANT INFORMATION:
Your personal pages:
<Removed>
On how the RSA-4096 Virus operates
Ransomware viruses are unique in that the consequences from them are not removed once the virus is uninstalled. The most famous and successful viruses of this type were called Cryptowall and Cryptlocker and they managed to earn their creators in what is estimated to be over $10 million in bit coins. It is understandable why these viruses are growing more popular with hackers with every passing day. It is highly likely the “all of your files were protected by a strong encryption with rsa-4096” message is actually one of these two viruses in disguise.
Basically once inside your computer the virus will target all of your data storing files – program related components are not targeted. Affected files are encrypted – a process which uses a predefined key to make the files unreadable to anyone who does not have the key. The files themselves are not changed – the encrypted copy is is an entirely different file from the original, which is deleted.
Paying the ransom asked by the RSA-4096 Virus is a bad idea
The messages spawned by the RSA-4096 Virus may warn you that all of your data will be lost if you attempt to recover it in any other way then paying them the ransom they demand. This is a lie.
The methods described in this guide do not modify the encrypted copies in any way, but they are also not perfect. It may not be possible to recover all of your files, but it is definitely worth trying them before making any hasty decisions. If you have very important files that remain encrypted after our instructions you can always decide to pay the ransom. That is, however, a really bad idea. Remember that these people are criminals and any money they receive will be used to improve their virus and release new copies of it. The recovery system is also automated any should any problem occur you’ll get nothing for your money. These people are in under to obligation to keep up their end of the bargain – you are totally at their mercy.
SUMMARY:
| Name | RSA-4096 (this is the encryption model – the actual virus can be one of many things) |
| Type | Ransomware |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
RSA-4096 Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
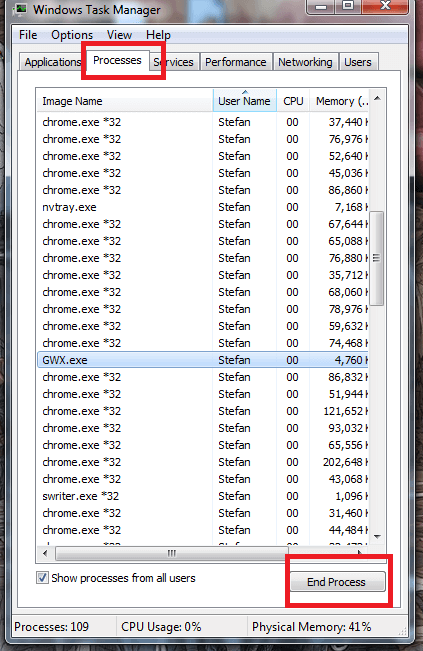
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply