Rugi
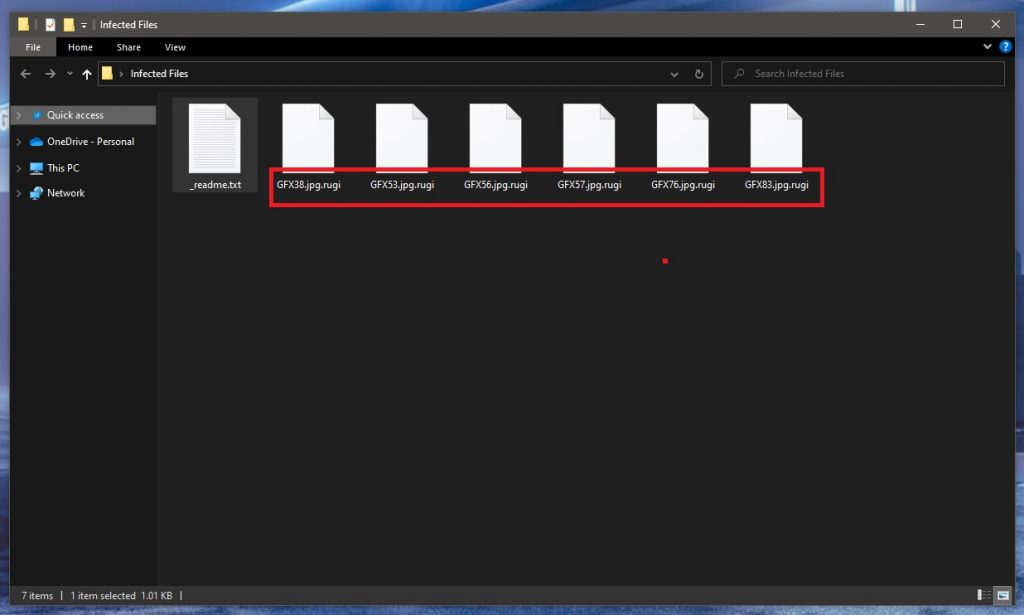
Rugi is a piece of malicious code based on ransomware which has been created to encrypt user data and render it inaccessible for an indefinite period of time. The victims of Rugi who want to access their files will have to pay a ransom to obtain a decryption key from the hackers behind the infection.
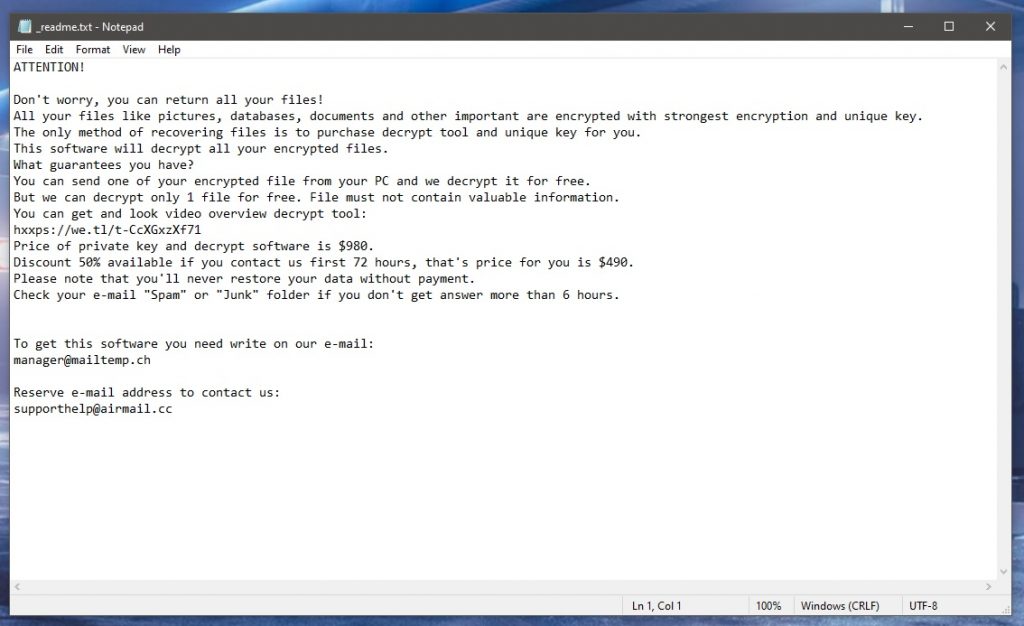
Ransomware viruses such as Rugi are a serious threat to the users’ personal or professional computer and can lead to loss of access to valuable personal or business-related data. The cyber-criminals behind these kinds of viruses employ various methods to extort money from their victims and do not hesitate to use threatening messages, ransom-demanding notifications, deadlines, and other tricks. Rugi, in particular, is an infection that encrypts the data found on a computer and holds it hostage until a certain amount of money is paid as a ransom. In order to return the data to its previous state, the victims are forced to transfer the money and are usually warned that there is no other way to recover their files
If you are on this page, you are probably searching for an alternative solution to remove the ransomware from your system and possibly get back your files without paying a ransom. And, just under this post, we are happy to provide you with some suggestions and a removal guide that may have exactly what you are looking for.
The Rugi virus
The Rugi virus is a ransomware-based virus intended to encrypt user files and keep them hostage for a ransom. The attack from the Rugi virus happens stealthily and includes encoding a list of file types and generating a ransom-demanding message on the victim’s screen.
Viruses like Rugi, Rugj, Rivd have a big advantage over most other forms of malware and this advantage comes from the way they operate. The ransomware infections are relatively non-intrusive and do not destroy or corrupt anything in the system, as opposed to Trojans or Worms. Encryption is their primary tool, but in its core, this is not a dangerous process but a method that protects digital data from unauthorized access. As we browse the Internet, we unwittingly use file encryption every day when we share sensitive information with others or when we buy things online. Therefore, many antivirus software programs out there do flag the file encryption as a harmful process and will not interrupt it while the ransomware runs it.
The Rugi file encryption
The Rugi file encryption is a malicious process used by cybercriminals to block access to user data until a ransom is paid. The Rugi file encryption runs in the background of the system and is typically not interrupted by most security programs.
Once it has been applied, the Rugi file encryption cannot be reversed in a way other than applying the corresponding decryption key. This key, however, is kept by the hackers behind Rugi and they demand a ransom for it. It is worth to mention, though, that there is no guarantee that the crooks will send the key to you if you pay the required money. Therefore, before transferring anything to them, we advise you to give a try to some alternative options. You can use our removal guide as a starting point. It will certainly help you remove Rugi, which is very important if you plan to give a try to some alternative file-recovery methods such as personal backups and system backup extraction.
SUMMARY:
| Name | Rugi |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Rugi Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Rugi files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment