*Source of claim SH can remove it.
Rulefloor.com
Rulefloor.com is classified as a browser hijacker, usually software like that is distributed through installation bundles and in most cases the user is not aware of these additional programs. Ads such as pop-up ads, banners and browser redirects tend to be the usual indications of an infection with Rulefloor.com.

If you are presently viewing this page, then you’ve probably had Rulefloor.com Virus installed on your PC without your knowledge or authorization. Ads such as pop-up ads, banners and browser redirects tend to be the usual indications of an infection with Rulefloor.com. This program is considered to belong to the software type referred to as browser hijackers and is specifically designed to do this, so don’t be surprised. If you notice any browser redirects, starting page modifications or similar issues, it is likely that the browser hijacker is responsible for them. We’ve added a guide below this post that will help you get rid of the browser hijacker. It’s going to assist you through the process of eliminating it in a couple of basic steps.
The display of annoying adverts is considered to be the central reason for the existence of browser hijacker products. The main purpose behind such apps like the Rulefloor.com virus, Main Captcha Top,is to make money through the ads shown by them on the basis of the pay-per-click practice. For each and every click made on the commercial, the Rulefloor.com virus owner acquires income.
Considering that typically the browser hijacker installs itself in the shape of a web browser extension, the commercials begin to pop-up after you start working with your web browser. Since, however, this type of advertising isn’t seen as illegal, the hijackers that are responsible for it are also not regarded as illegal software pieces. Actually, a lot of software owners use browser hijackers to further advertise their main products or even make some extra revenue. One distinguishing feature of a browser hijacker software programs is their aggressiveness when showing adverts. It’s likely that you’d be unable to use your browser because of the ceaseless barrage of pop-ups, box-messages and banners. This behavior is commonly mistaken for a pc virus invasion. Working with this invasive activity is usually very irritating, nonetheless, it is incorrect to regard browser hijacker as as some malicious virus. Harmful pieces of software the likes of viruses, Trojans and the rising in popularity Ransomware, are the real threats that people should become aware of. Certainly, you find it difficult to wait to get to our removal guide, then again, before you actually move on to it, there’s a handful of additional crucial info, related to browser hijacker, that you should learn. The term browser hijacker is a combination of Advertisement and Software – it means that browser hijacker products are designed with the intention to display Ads. Such ads are offered in all shapes and sizes – pop-ups, banners, messages, possibly even page redirects. The first trouble with those commercials is the fact that they cause it to become absolutely impossible to effectively use your internet browser. Hardly any of this can be a surprise – just think. the supreme purpose is to earn them some money every time you click on the Ads. browser hijacker tools operate the pay-per-click method so that they can make money for their manufacturers.
SUMMARY:
| Name | Rulefloor.com |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
Remove Rulefloor.com Virus
Users who want to remove Rulefloor.com as quickly as possible may try to use these quick instructions below:
- Launch the affected browser
- Tap on the browser’s settings icon and select More Tools (or Add-ons, depending on what browser you are using).
- Open the Extensions tab and in the list of extensions try to find the Rulefloor.com extension
- Highlight it and select Remove (or directly click on the Trash Bin icon next to it)
- Next, look for other extensions that you have not installed by yourself and remove them as well.
In case these instructions aren’t effective, please use the more detailed Rulefloor.com removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Firstly, we will advise you to Bookmark this page as you will need to refer back to it in order to complete the removal of Rulefloor.com.
Next, boot the computer in Safe Mode (use the link for help).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
After you have booted in Safe Mode, open the Task Manager (press CTRL + SHIFT + ESC keys from the keyboard). Once the window opens, select the second tab that says “Processes” (“Details” in Windows 8 and 10). This will display a detailed list of processes that are currently active on your computer. Look at them and try to figure out which processes are linked to Rulefloor.com and could be a source of your problems.

Once you find such processes, highlight them individually and Right click on every single one of them. From the menu that opens, select Open File Location. Scan the files found in that location with our free online virus scanner in order to determine if they are dangerous:

After you scan the files in the folders and detect that there are threats, end the processes related to these files and delete their folders.

Next, in the Run dialog (press Start + R key to open it) type appwiz.cpl

Click OK to run the command and you will enter the Control Panel.
Once inside the Control Panel, look for questionable or unfamiliar entries that could be related to Rulefloor.com and Uninstall them.
After that, open the Run dialog again (Start+R key) and type msconfig in the text field. Hit the Enter key of your keyboard. This will open the system configuration pop-up:

Select the Startup tab and carefully look through the list of applications there. Remove the checkmark from any apps that might be linked to Rulefloor.com or look suspicious and have an “Unknown” Manufacturer.

*Source of claim SH can remove it.
Next, again open the Run dialog but this time copy the following in the text field:
notepad %windir%/system32/Drivers/etc/hosts
Hit the Enter key to execute it and this will open a simple text file on your screen named Hosts.
In the text, head to where it says “Localhost” and see if there are different IP addresses under that section. See the image below:

If there are other IPs, this might be an indication that you have been hacked. Please, write us in the comments below this article for more instructions on how to proceed in this case.
In your Start Menu, open the Network Connections. Once there, do the following:
- Right-click on the Network Adapter that is currently in use
- Select Properties > Internet Protocol Version 4 (ICP/IP), then again click Properties.
- Set the DNS to Obtain DNS server address automatically.
- Next, click on Advanced and in the window that opens select the DNS tab. Remove everything in this field and click OK.


The instructions in this step will help you remove Rulefloor.com from your browser. Please complete them to prevent the problematic program from reappearing after a system reboot.
Attention! We are demonstrating the steps in Google Chrome but if you are using another browser, you shold do this for it as well.
Find the browser’s shortcut on your desktop and right-click it. Then, select Properties.

In Properties choose the Shortcut tab. Find the field where it says Target, and make sure that you remove everything after .exe.

![]() Remove Rulefloor.com from Internet Explorer:
Remove Rulefloor.com from Internet Explorer:
In case that IE is the browser that has been affected by Rulefloor.com, launch the browser and click ![]() (this is the menu icon at the upper left corner)Then, select Manage Add-ons.
(this is the menu icon at the upper left corner)Then, select Manage Add-ons.
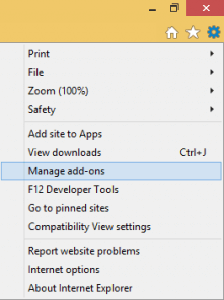
In the Add-ons list try to find the threat and Disable it.
Next, go to the gear icon ![]() once again and choose the Internet Options. Programs like Rulefloor.com may change the Home Page URL to whatever they want and if this is the case, place your preferred Home Page address and click on Apply.
once again and choose the Internet Options. Programs like Rulefloor.com may change the Home Page URL to whatever they want and if this is the case, place your preferred Home Page address and click on Apply.
 Remove Rulefloor.com from Firefox:
Remove Rulefloor.com from Firefox:
If Firefox has been your main browser and Rulefloor.com has hijacked it, click the menu icon ![]() at the upper left corner and choose Add-ons. Then click on the Extensions tab from the left panel. Remove any problematic or questionable extensions that could be related to Rulefloor.com from the list.
at the upper left corner and choose Add-ons. Then click on the Extensions tab from the left panel. Remove any problematic or questionable extensions that could be related to Rulefloor.com from the list.

 Remove Rulefloor.com from Chrome:
Remove Rulefloor.com from Chrome:
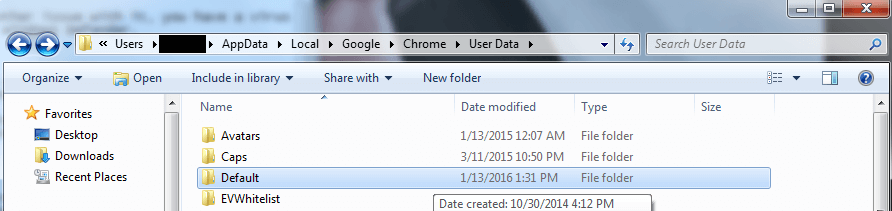
After you are done with the steps above, Close Chrome and navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. Find the Folder called “Default” and Rename it to Backup Default. After that Relaunch Chrome.

In this final step, you need to find and remove all traces of Rulefloor.com from the Registry Editor. For that, firstly open the Registry Editor (Type Regedit in the windows search field and press Enter).
In the Editor, press CTRL and F key combination and type the Name of the threat that you are looking for. The entries that are found with this or a similiar name should be deleted by right clicking on them.
Alternatively, if nothing is found with the help of the above methond, manually mavigate to the following directories and delete them:
- HKEY_CURRENT_USER/Software/Random Directory.
HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/Random
HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/Random
You can ask us in the comments if you are not sure what needs to be deleted. In case the guide isn’t effective in dealing with Rulefloor.com completely, we suggest that you download the professional removal program recommended on this page or use our free online virus scanner.

Leave a Comment