*Source of claim SH can remove it.
Windows Host Process Rundll32
Windows Host Process Rundll32, also known as rundll32.exe, is a legitimate system file and a critical part of the Windows operating system. It plays a vital role in the execution of dynamic link libraries (DLLs) and helps applications to share code across different programs. Rundll32.exe is responsible for launching functions stored within DLL files and is commonly used by Windows to run various system processes and services. However, due to its crucial role in executing code, some cybercriminals may use the name “rundll32.exe” to camouflage malicious programs and carry out unauthorized activities on a computer. In such cases, the malicious file might not be the genuine Windows Host Process Rundll32, but a disguised version that aims to compromise the system’s security.
What is Rundll32?
Rundll32, also known as “Windows Host Process”, is a legitimate Windows system file that plays a crucial role in executing dynamic link libraries (DLLs) in Windows operating systems. It acts as a mediator between the operating system and the DLL files, allowing them to be executed and utilized by various programs and processes. DLL files contain code and data that multiple programs can use simultaneously, promoting efficiency and reducing redundancy in the system. Rundll32 enables programs to call specific functions or routines within DLL files, thereby providing a way for software to share resources and functionalities.
Is rundll32 a virus?
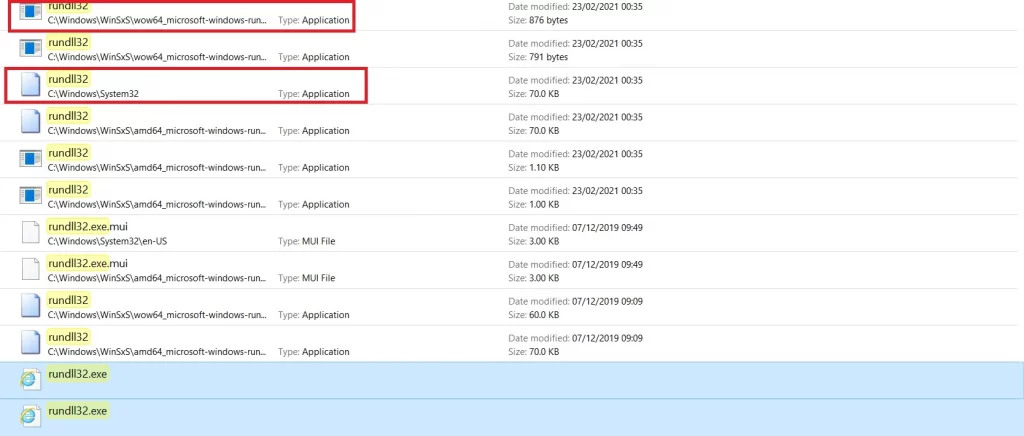
While rundll32 itself is not harmful, it has been targeted by cybercriminals who sometimes use its name to disguise malware and other malicious programs. Therefore, it’s important to note that the legitimate rundll32 is located in the Windows/System32 folder. If you detect that file on another system location or you suspect that rundll32 is acting suspiciously or causing problems on your computer, it’s crucial to run a thorough system scan with reputable antivirus software to identify and remove any potential threats.
Can I delete rundll32.exe?
Deleting or modifying the legitimate rundll32.exe file can lead to severe system issues, such as instability or errors, since it is essential for the proper functioning of the operating system. To verify the legitimacy of the rundll32.exe file in the System32 folder it is recommended to run a scan with reputable antivirus software that can help detect and remove any malicious versions of rundll32.exe that may have infiltrated the system.
The Rundll32.exe Trojan
The Rundll32.exe Trojan is a term used to describe a malicious program that disguises itself as the legitimate Windows system file “rundll32.exe.” This Trojan horse can infect a computer by pretending to be a legitimate system process while actually carrying out malicious activities in the background. Once the Rundll32.exe Trojan infiltrates a system, it can initiate various harmful actions, such as data destruction, theft of passwords and sensitive information, personal details, and banking credentials, which can be used for identity theft or financial fraud, remote access that allows hackers to gain unauthorized remote control to the compromised system, as well as distribution of other malware.
Rundll32.exe
Rundll32.exe is a perilous Trojan horse that operates in stealth, compromising a computer and initiating various malicious activities. While present on a system, Rundll32.exe can wreak havoc, causing destruction to personal data, siphoning passwords and banking credentials, and granting unauthorized remote access to hackers. If your computer has fallen victim to this Trojan, it is essential to remain composed and take immediate steps to safely and effectively remove it. Fortunately, you’ve landed on this page, where a comprehensive removal guide is available, enabling you to locate and eradicate the danger along with all its concealed components.
SUMMARY:
| Name | Rundll32.exe |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How to remove rundll32.exe
To try and remove rundll32.exe quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the rundll32.exe extension (as well as any other unfamiliar ones).
- Remove rundll32.exe by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of rundll32.exe and any other suspicious items.
If this does not work as described please follow our more detailed rundll32.exe removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the rundll32.exe app and kill its processes
Uninstall the rundll32.exe app and kill its processes
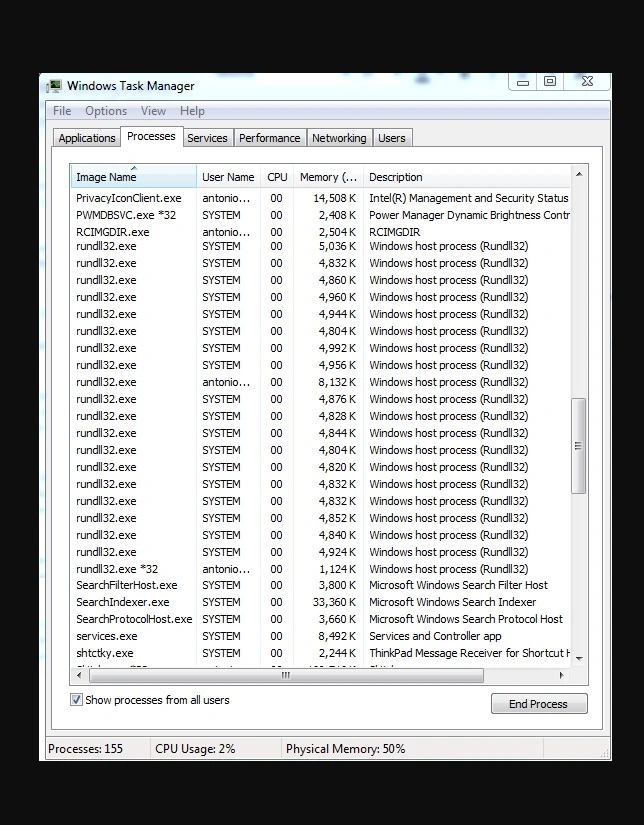
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from rundll32.exe. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to rundll32.exe, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to rundll32.exe.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo rundll32.exe changes made to different system settings
Undo rundll32.exe changes made to different system settings
It’s possible that rundll32.exe has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment