*Source of claim SH can remove it.
Table Of Contents
If you suspect that this infection may currently be present on your computer, it is essential that you take the necessary actions to check your system and remove anything that may be a threat to its safety.
Before we get to the guide, however, we should tell you a bit more about SAntivirusKD.sys and the Trojan horse threats in general. Unlike other common malware types, the representatives of the Trojan horse family can be used in different ways as they don’t have one single purpose. This makes them one of the most versatile forms of computer threats that you could encounter, which is also why they could be so unpredictable. This is especially true about newer Trojan horse versions such as SAntivirusKD.sys. Due to insufficient research data because of the recent release date of SAntivirusKD.sys, we can’t tell you with certainty the end goal of this threat. What we can do, however, is give you several examples of what this infection may do in your computer if it gets there:
Trojans are well-known for their espionage abilities. They are oftentimes used as tools for collecting sensitive personal data from the attacked victims. Depending on what the acquired data is, it could be used for blackmailing, harassment, banking theft, and more.
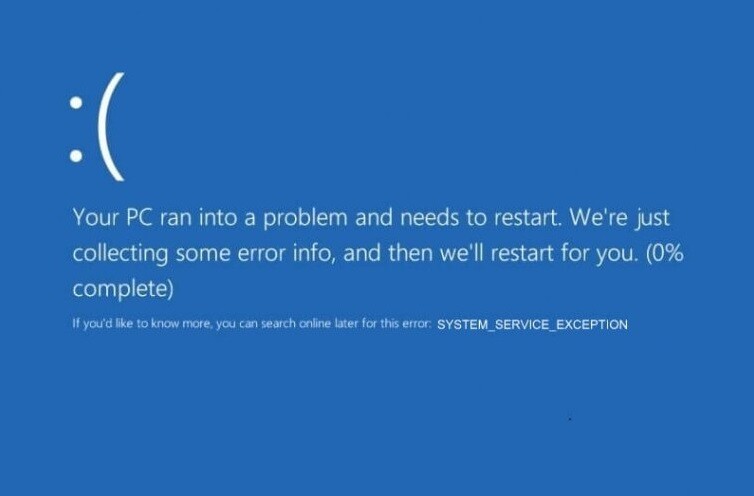
The SAntivirusKD.sys Blue Screen
The SAntivirusKD.sys Blue Screen is a common symptom of infection with the Trojan Horse virus of the same name. If you experience the SAntivirusKD.sys Blue Screen on your computer, you should restart the machine, check it for malware, and remove any detected threats.
Infections like the SAntivirusKD.sys blue screen can take control of certain settings and processes in the attacked computer. In those cases, the SAntivirusKD.sys blue screen can trick the user into providing the virus with admin rights, which allows the Trojan to then launch different processes and use the computer’s system resources (alongside those of many other infected machines) for cryptocurrency mining, spam distribution, DDoS attacks, and more.
A lot of times, the representatives of another widespread malware category, the infamous Ransomware viruses, get distributed with the help of disguised Trojan horse viruses that are used as backdoors for the Ransomware into the victim’s computers. This use of the Trojan horse infections is particularly common at the moment.
Ways Trojan horses are distributed
There could be many ways to distribute a Trojan but most of them usually revolve around tricking the potential victims into downloading the virus themselves. This could be done by disguising the threat as some seemingly useful program and then uploading it to a file-sharing or torrent site. It could also be done by sending the disguised Trojan via a misleading e-mail or using a social media platform. Luckily, if you adhere to some general online safety habits, such as avoiding spam messages and not downloading software from sites that spread pirated programs, and if you use your common sense while browsing the web, you should be pretty well protected against such viruses in the future. Also, having a reliable security tool installed could greatly reduce the risk of landing a Trojan, which is why we advise you to get one in case you currently don’t have such a program.
SUMMARY:
| Name | SAntivirusKD.sys |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Santiviruskd.sys blue screen fix
One possible Santiviruskd.sys blue screen fix is to boot into Safe Mode which should isolate the problem that’s causing the blue screen. This Santiviruskd.sys blue screen fix, however, isn’t permanent and should only serve as the first step towards troubleshooting the underlying problem.
The first thing that must be done when troubleshooting this (or any other) software problem is to get your machine into Safe Mode. With Safe Mode enabled, the system won’t allow programs and processes that aren’t essential to be activated and so, hopefully, this will keep the malware from operating while you are in Safe Mode, thus stopping it from interfering with your attempts to delete the virus. You can learn how to enter Safe Mode on your machine from this link.
Remove SAntivirusKD.sys

Before you get to the more advanced steps from our removal guide, we suggest you try deleting any hazardous and potentially unwanted apps from the computer because sometimes this may be all that it takes for the virus to be removed. Here’s a quick way to do this which could save you lots of time:
- First. go into your Control Panel from the Start Menu, find the Uninstall a Program button and select that.
- Explore the list of software items that you will see next and look for applications and programs that seem to have been installed on your computer without your permission. Also be on the lookout for items that have been recently installed on your machine, around the time you started having problems with the SAntivirusKD.sys virus.
- Select any program or app from the Uninstall a Program list you deem unreliable, suspicious, and potentially linked to the Trojan Horse virus and uninstall it by clicking on the Uninstall/Change button located at the top of the current window.
- If there is an uninstallation wizard, follow the steps in it but be sure to select the NO option if you come across the following screen in order to avoid getting more malware installed on your PC:

- In case the situation doesn’t improve after the uninstallation or if you weren’t allowed to uninstall the suspicious app(s), then you should proceed with the more detailed steps from the next lines.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Access the Task Manager (Ctrl + Shift + Alt from the keyboard), select Processes and look for processes with suspicious names and/or ones that use unusually large portions of the RAM memory of the computer or if its CPU. You may or may not see the SAntivirusKD.sys in there – Trojans tend to disguise their processes by giving them names that won’t raise suspicion in the victims. Therefore, if you think that a given process may have something to do with the infection, it’s best to look up its name on the Internet. If your research tells you that the process in question isn’t a legitimate one, then you should right-click on it in the Task Manager and select Open File Location.

From the directory where the suspicious process’ files are located, scan each of the files there by dragging them to this free online malware scanner:

If any of the files gets flagged as malware, return to the Task Manager and kill the process by right-clicking it and selecting End Process Tree. After that, go to the directory of the malicious process and delete the whole folder in which the malware files are located.

Press Ctrl+R together, type msconfig and press Enter. Then go to Startup and assess the items in the startup list – ones that have an Unknown manufacturer as well as ones that with odd and unusual names that you don’t recognize should be disabled by removing the tick from the checkbox in front of them. After that, click on Apply and then on OK so that the changes you’ve just made would be saved.


Place the notepad %windir%/system32/Drivers/etc/hosts line in your Start Menu search field and open the first icon from the results of your search. This is the Hosts file of your computer and it is a common target for a variety of malware threats. The way you know if your Hosts file has been hacked is by looking at what’s written below LocalHost. In normal circumstances, there shouldn’t be anything there but if you see some strange IP addresses under Localhost, this likely means that you have malware on the computer. However, not all IPs there come from viruses or malware – some are added by legitimate programs that need to make changes to the Hosts file in order to function properly. Therefore, it’s best if you copy the IPs you see under Localhost and send them to us via the comments section. We will have a look at them and tell you if you must delete them.

If we tell you that the IPs you’ve found in your Hosts file are likely connected to the malware, delete them from the text file as you would delete any regular text and then select the File menu and click on Save to save the changes to the file that you have just made.

This next step involves deleting items from the Registry of the computer, where lots of essential system settings are stored. You must always be certain that you aren’t deleting the wrong thing when working with the Registry Editor or else your system may experience negative and unforeseen consequences. Because of that, we strongly recommend that you always consult us through the comments section about deleting a given item from the Registry if you aren’t sure that said item ought to be deleted.
Now, to open the Registry Editor, type regedit in the Ctrl + R (Run) search box we mentioned earlier and hit Enter. Windows will ask you whether you are certain that you want to allow the app to introduce changes to the system – confirm by clicking on the Yes option.
Next, in the Editor, press Ctrl + F to evoke the Registry Editor search box and type in it the name of the SAntivirusKD.sys virus. Click on Find Next and if anything gets found, select it and then press Del from the keyboard to delete the item. Click on Find Next again and keep deleting items that carry the name of the virus until there’s nothing left with that name.
Afterwards, locate these directories in the Registry Editor and look at the folders contained inside them. If you see any folders that have names that seem randomly generated (e.g. long strings of seemingly unrelated characters), then delete them in the same way you did above. Here, however, it is important to be certain that what you are deleting isn’t something that shouldn’t be removed so it’s better to first ask us in the comments about it before you do anything.
- HKEY_CURRENT_USER > Software > *Oddly-named folder*
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run > *Oddly-named folder*
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main > *Oddly-named folder*

Hi, I’m in the middle of deleting this virus through the registry, the ones I am looking at, under ‘data’, are all numbers, dashes and Hashtags.
Are ok to delete??
Hi Dan,
can you upload a picture somewhere, and link it in the comments?