Satunians
In the event that your computer has recently been infected with a program called Satunians, you have landed yourself what is known as a browser hijacker. Programs like Satunians are usually installed by users without them realizing it, alongside other software.

This is a technique that is commonly referred to as program bundling. And as a result of it, potentially unwanted programs (or PUPs) like Satunians and Omnatuor are added to the installation manager of various forms of freeware and shareware as optional or extra installs. What this means is that although they are included in the setup, users can generally opt out of them – as long as they are in fact paying attention to the setup.
In most cases, however, users typically just go for the default installation settings, which is exactly what the developers count on, and that automatically installs any extra components that were added. What you should do in such cases instead, however, is opt for the custom or advanced settings. That way there will typically be a step in the installation manager that allows you to see what else has been bundled in the setup and you should be able to exclude those from the installation process.
But that’s for the future. At the moment, having Satunians installed in your Chrome, Firefox, Edge or whatever other browser you’re using, you have other concerns. Specifically, these may be revolving around the altered browser settings (e.g. changed homepage, different default search engine) and numerous popups, banners, links and other types of ads on your screen. In addition, you may have already also started experiencing page redirects to various websites, which is another common effect of software like Satunians.
If this is the case, then you’re likely seeking for a way to rid yourself of all these fairly annoying effects, and we can completely understand why that is. However, the only way you will be able to reset your browser configurations and once again be in charge of your web browsing experience is if you remove Satunians from your system completely. And the developers of such software rarely include that as an option. Hence, you will often need to fiddle around in your system in order to thoroughly clean out Satunians or whatever other hijacker you’re dealing with, so as to avoid leaving any residual components.
And for this reason our team of professionals has put together a detailed free removal guide, which you can find just below the current post.
It’s also a good idea to have this software uninstalled from your PC if you would like to make sure that its security remains intact. It just so happens that browser hijackers and similar application may sometimes unintentionally expose users to potentially dangerous web locations and therefore malware and viruses. So, in order to minimize the risk of landing some harmful ransomware or Trojan horse virus, it’s best to have the source of this risk removed altogether. And until then, try to abstain from interacting with any of the ads showcased by Satunians.
SUMMARY:
| Name | Satunians |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Banners, box messages, popups and different types of other ads that are present on all pages and websites you visit. |
| Distribution Method | Program bundles are the leading source for software of this type, but can also be distributed via spam and other hijackers or adware. |
| Detection Tool |
Remove Satunians Virus
To try and remove Satunians quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Satunians extension (as well as any other unfamiliar ones).
- Remove Satunians by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Satunians and any other suspicious items.
If this does not work as described please follow our more detailed Satunians removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Satunians from Internet Explorer:
Remove Satunians from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
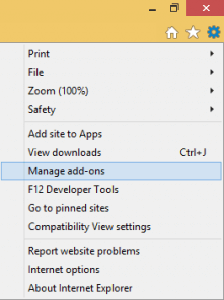
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Satunians from Firefox:
Remove Satunians from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Satunians from Chrome:
Remove Satunians from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
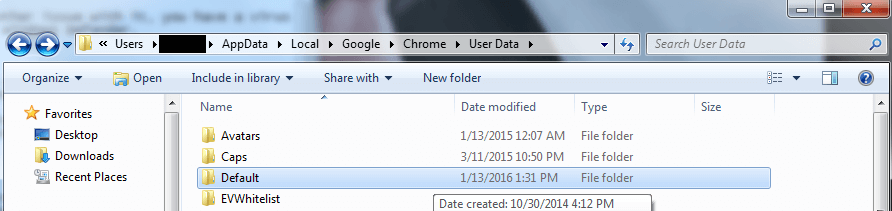
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment