*Source of claim SH can remove it.
Search Daemon
Search Daemon is a Mac program that can integrate unnecessary components into popular Mac browsers, including Safari, Firefox, Chrome, and others. The users who have Search Daemon installed on their system can find unauthorized modifications to the search engine and/or the homepage of their browsers.
Search Daemon is a form of unwanted Mac software that causes disturbances in Safari and redirects the user to random pages. Search Deamon could also modify certain browser elements like the starting page or the toolbar without user approval.
The good news is that these modifications can be reversed and, on this page, you can find out how to do that. Below we have prepared a removal guide and a professional removal tool that can be used to successfully uninstall Search Daemon all the changes that it has imposed without your approval.
The people who currently have this program on their Mac device can quickly detect it, as it not only changes the browser’s search engine and homepage settings but also spams the screen with pop-up advertisements, banners, intriguing offers, and discount deals that cannot be removed unless clicked on. The strange program also redirects the users’ searches to websites that promote specific products and services and also add additional toolbars and buttons to the browser’s toolbar.
The majority of users have issues using their web browser after the imposed updates and find it difficult to navigate the web when their screen constantly gets filled with banners, pop-up ads, and similar aggressive commercials. Many people find it irritating that the newly set search engine generates primarily sponsored search results that redirect to websites that normally don’t have much to do with their actual searches. Others find the homepage modifications annoying and seek methods to remove the imposed web address but without much success.
Search Daemon on Mac
Search Daemon on Mac is an unwanted add-on app introduced to Mac browsers without the knowledge of the user which can take over the browser and cause performance issues. Search Daemon on Mac can make settings changes, replace the search engine, and redirect the browser.
The browser hijackers, in general, are programs that cannot cause harm to a computer. They don’t have file-encrypting abilities like Ransomware and cannot destroy the system like Trojan viruses. Although this news can be calming, the hijackers remain software that is commonly regarded as unwanted. The reason is such programs can make numerous unauthorized changes to key browser settings (such as the homepage, the default search engine, the new tab page, etc.) and redirect users to web content that is irrelevant or sketchy. A program like Search Daemon, for instance, can interrupt your web browsing by filling your screen with various pop-up advertisements, full-page banners, and offers that link to various pages.
The Search Daemon Virus
The Search Daemon virus is known for installing ad-generating and page-redirecting components inside the default Mac web browser. After imposing its changes, the Search Daemon virus starts to display pop-up ads, colorful banners, and notifications on the screen and to redirect users to specific websites.
The Search Daemon Virus is rogue Mac software and it will control what you see in your browser in its attempts to advertise certain low-ranking sites. The Search Daemon Virus isn’t directly threatening to the system but could become a gateway for more dangerous programs.
The newly set search engine typically delivers sponsored search results and places them on top of the page while the new homepage automatically loads a particular domain each time a new browsing session is started by the user.
The SearchDaemon app
The SearchDaemon app is a program designed to redirect traffic from Mac browsers to predefined websites. When a user has the SearchDaemon app installed in their browser, they will automatically be rerouted to specific URLs that promote some products, services, or software.
Some people may find it challenging to uninstall the browser hijacker and to successfully remove its browser modifications. Fortunately, the instructions in the removal guide below will assist them and help cope with the unwanted software quickly and without any risks for the system.
SUMMARY:
| Name | Search Daemon |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
Search Daemon Mac Virus Removal
The Search Daemon Mac Virus Removal can be completed manually or with the help of an anti-malware tool. If you want to remove the Search Daemon Mac Virus, we suggest you combine the manual removal steps with the use of a reliable malware removal app.
If the Search Daemon Mac Virus has added an extension to your Safari browser, removing said extension could make the whole problem go away and remove the need to go any further into this guide, so this is the first thing we suggest you do when troubleshooting this issue.
First, access your Safari browser, select the Safari Menu, go to Preferences, and open the section labeled Extensions.
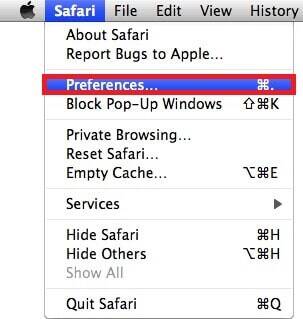
In there, you will see the different add-ons that are installed in the browser. If there’s one named Search Daemon in there, select the Uninstallation button next to it to remove the unwanted extension.

If you don’t see such an item on that page, know that the browser hijacker’s extension could have a different name. Look for an extension that you may not have installed yourself or one that simply looks suspicious and unneeded. In case you cannot figure out which of the extensions is the one responsible for the problems in the browser, delete all of them, one extension at a time, so as to find out which one is disrupting your browsing experience and later reinstall the other ones.
Once you think you have removed the browser add-on that has hijacked your browser, you should restart the Mac and see if the situation has improved. In case it hasn’t, continue with the following instructions.

*Source of claim SH can remove it.
If the Search Daemon hijacker is keeping your browser open and you cannot close Safari (this may happen sometimes), go to the Apple Menu and select Force Quit. Then, in the window that pops-up on your screen, click on the Safari entry and then on the Force Quit button to close the browser.
Though rarely, force quitting the browser may not work, in which case you must restart the computer so do this if you are not able to close Safari.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Now it is time to find the process that Search Daemon is running and kill it. For this, you will need to go to the Activity Monitor of your Mac (Utilities > Applications > Activity Monitor). Once you get there, you must find the hijacker process among the list of currently running processes. This might be difficult since you will probably not see any processes named Search Daemon. In case you do see such a process, select it and then select the Quit Process (or X) button to end that process. However, if you cannot find one named Search Daemon, you will have to look for other red flags such as excessive consumption of resources (RAM and Processor time) as well as an unusual name. Another suspicious sign is if a given process doesn’t seem to be linked to a program that is running on your Mac at the moment. However, such processes could be OS-related ones so it is always good to first look up their names before you quit them. If you accidentally quit a system process, it is possible that the computer may become unstable so you have to be careful.
After you have pinpointed the process that is related to the browser hijacker, select it from the Activity Monitor and then click the Information icon to show a window with more details about that process. In that window, click on the Sample button and then on Save. Save the sample file on a location that you can easily access – saving it on the Desktop would be best.

Now it is time to scan the sample file for malicious data – drag and drop that file onto the anti-malware scanner you will see below and let the latter do its job of scanning the file.
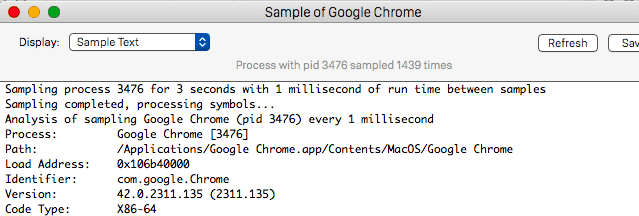
If the scanner finds anything potentially malicious in the file you tested, this means that the process you sampled is probably not supposed to be running and is most likely linked to the hijacker so you must Quit it like we explained above. After you are done with that, you can move the sample file to Trash to delete it.


Now, you must start the browser to clear it but the tabs and pages that the hijacker may have previously opened in it must not be allowed to load or else this may interfere with your attempts to restore Safari to its normal state. Therefore, when opening the browser, make sure that you are holding down the Shift key. If when the browser opens there are still hijacker pages and tabs loaded in it, then you must disconnect your Mac from the Internet and try starting Safari in this way again.
- Obviously, if your Internet connection goes through a physical Ethernet cable, you must remove he camble from the computer to stop the connection. If you are using wireless Internet, then you can either turn off the router for your Wi-Fi or you can press down the Option key, open the Wi-Fi menu (top of the screen), and select Turn Wi-Fi Off. When you complete the guide and need to bring back your Internet, go back to the Wi-Fi menu and select the Turn Wi-Fi On option.

When you are in Safari, the first thing you should do is check its extensions again as we explained at the beginning of the guide. In case you notice that an extension that you have removed earlier has somehow gotten back inside the browser, delete it again.
Next, go to the Privacy section of Preferences, click the option labeled Remove All Website Data, and confirm the action. This will delete all site-related data from your browser, including cookies and cached files but it will also log you out of your online accounts so you’d have to log in manually the next time you visit their respective sites.

After Privacy, go to General and in there see if the homepage of Safari has been changed without your permission. If it has been replaced, restore the address that you prefer to be set as your browser’s homepage.
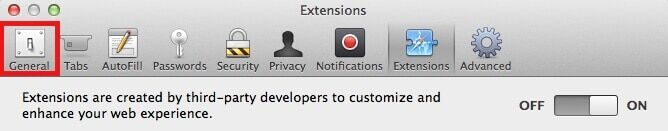
It is very important to not allow the hijacker-imposed homepage address to remain in your browser. In some instances, this could lead to sudden redirects to hazardous pages and the display of unsafe and misleading online ads. The hijacked homepage of your browser is one of the main tools that the hijacker uses to push its agenda.

Finally, open the History menu of Safari, select Clear History, set it to the longest time period (from the beginning), and click on Clear Browsing History. This is usually not necessary to remove the hijacker’s influence from your browser but it may still help in some instances so it won’t hurt if you do it.

Any other browsing programs present on your Mac need to be cleaned too because most hijackers would target all the browsers in the system and not only the main one.
![]() Removing ads from Firefox for Mac:
Removing ads from Firefox for Mac:
To check the extensions of Firefox, go to its Menu > Add-ons > Extensions and do the same you did with Safari in the previous steps – look for unusual and potentially unwanted extension items and delete them from the browser.

Afterwards, you should clear the rest of the browser – information on how to do this can be found inside this guide.
![]() Removing ads from Chrome for Mac:
Removing ads from Chrome for Mac:
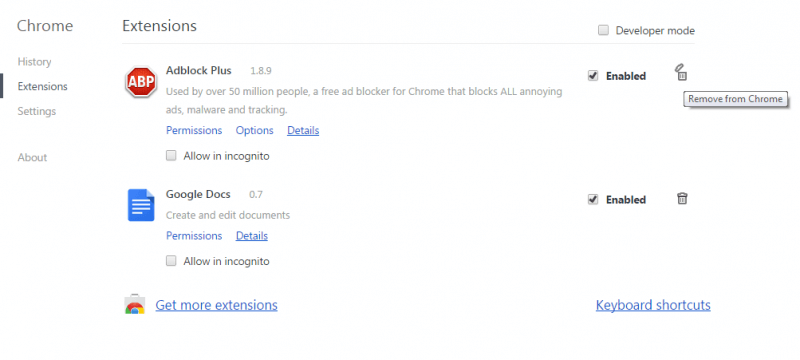
For Chrome and some other Chromium-based browsers, open the menu of the browser, go to More Tools/Options > Extensions. Here, you must also find any items that shouldn’t be in the browser and may be causing disturbances and remove them by selecting the Trashcan icon next to them.
Now, you must check the search engines that Chrome uses so go to Settings, type Search in the search box on the Settings page, and select the Manage Seach Engines result. Under these settings, you should see what the current search engines that Chrome uses are. If there you see engines you don’t recognize and/or ones you think could be unwanted or harmful, remove them, leaving only the search engines that you are sure you can trust.
Finally, you must clean the browsing data for Chrome and to find how to do that, visit this link for more instructions.
Final Notes
In most cases, completing the steps we’ve shared here should ultimately result in the full removal of the unwanted browser hijacker malware from your Mac. However, on the off chance that this guide was not enough or if you have stumbled upon any obstacles while trying to complete it, you can always share with us your problem by writing us a comment and posting it down below. We will try to get back to you as quickly as possible with a relevant and helpful reply.

Leave a Comment