This page aims to help you remove the Search Encrypt “Malware”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Are you facing difficulty navigating the web due to some nagging and aggressively popping ads, banners and pop-ups? Do you experience sudden page redirects? Has some strange new toolbar, a search engine or a homepage taken over your browser? If yes, then a browser hijacking program like Search Encrypt could be the most probable source of your disturbance. Stay on this page to learn how to safely uninstall it and remove all of its potentially unwanted modifications and ads, as well as how to reverse the settings of your Chrome, Firefox or Explorer back to normal.
How the Search Encrypt “Malware” operates
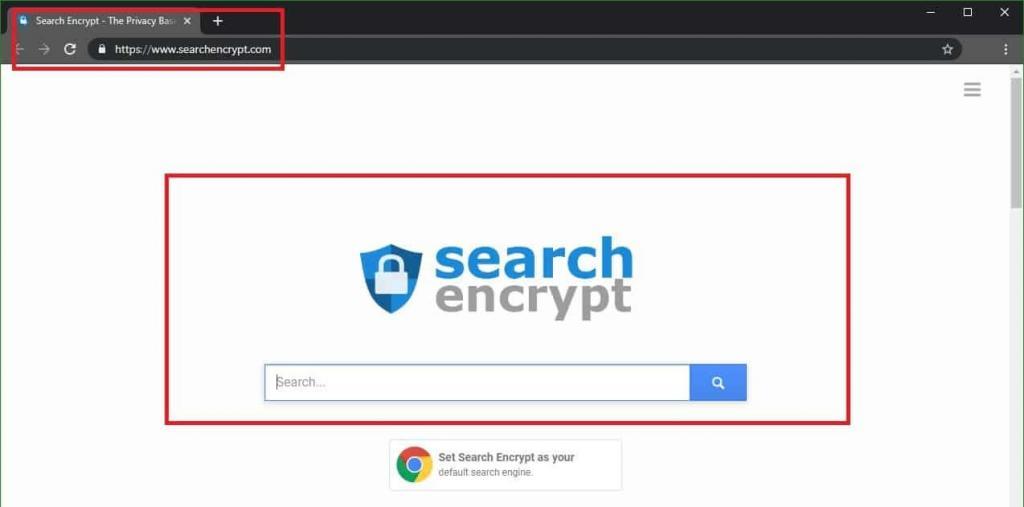
If you are seeing ads in your browser that are in some way related to the Search Encrypt “malware” or if your current default browser search engine has the its logo on it, then you definitely have this hijacker in your system and you may want to get it uninstalled with the help of the instructions that we have here. The Search Encrypt “malware” isn’t a very dangerous threat and you don’t have to bring your computer to an IT professional – you can most probably handle this yourself, as long as you have access to the right guidance. Though most users refer to it as the Search Encrypt “malware” – this won’t really harm the system or the files on your computer as it isn’t really a virus. In reality, the Search Encrypt “malware” is a browser hijacker and its main goal is to promote different products on your screen.
Browser hijackers – what programs are these?
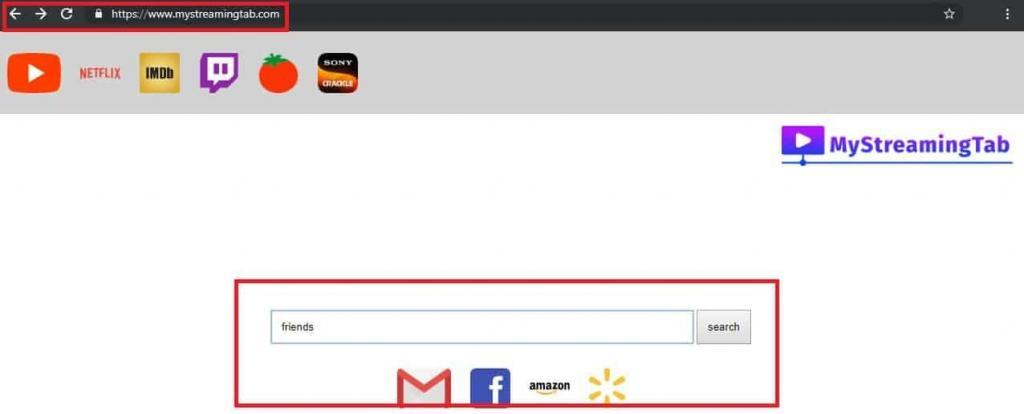
Browser hijackers are all the programs that tend to intrusively display all sorts of undesired advertisements on the users’ screens. These programs are also known to impose certain potentially unwanted changes to the users’ default browser such as homepage or search engine replacements or the installation of new toolbars.The Search Encrypt “virus” is a typical representative of this software category and as such, it is absolutely capable of taking over your browser in an above-described way and making it display tens of nagging ads.
There is a lot of money in the way that browser hijackers operate because these pieces of software basically serve as advertising tools. Many vendors, advertisers, and software developers use them to promote their services and products and ensure greater exposure to their ads. With this idea, pieces like the Search Encrypt “virus” are specially developed to expose or redirect the users to certain sponsored messages, ads or websites and prompt them to click on them. This way, the people, who stay behind the hijackers, can benefit from the clicks (through Pay-Per-Click), the website traffic and the eventual sales they make.
The users, whose browser has been hijacked, however, may have to endure a constant flow of intrusive pop-ups, banners, ads, in-text messages, new tabs and sudden page redirects. Such aggressive advertising activity is generally not malicious, but is often referred to as potentially unwanted and may heavily decrease their web experience and cause irritation and browsing disturbance. Unfortunately, there is no way to disable or stop the ads through some menu or some settings and even uninstalling the affected browser may not remove them. That’s why, for a lot of users, the permanent solution to save themselves from the stream of nagging ads is to uninstall the browser hijacker.
Search Encrypt may employ some aggressive marketing practices!
There are a few more good reasons to rid your system of the Search Encrypt “malware” and similar programs. Browser hijackers are often programmed to extract browsing-related data from the affected browser. This way, they can silently collect information about the users’ browsing queries, latest web activities and interests and employ this information in various aggressive advertising practices such as intrusive ad-generation or sponsored ads positioning on your screen.
The developers claim that such data collection activity is only used to improve the users’ exposure to more relevant ads and has no intention to cause any harm, nor can it compromise their passwords, login credentials or confidential data. In a way, this is true, because browser hijackers are not typical viruses and definitely cannot cause any major damage to the computer. Unlike the real malicious threats like Ransomware, Trojans and other viruses, programs like the Search Encrypt “malware” do not contain malicious scripts. In fact, security experts consider them to be pretty harmless, compared to a Ransomware infection, for example, because they cannot destroy your files or your system in any way. What is more, if the data collecting, the frequent page redirects, and the aggressively popping ads are disturbing you, you can easily remove the browser hijacker and save yourself from the annoyance without any harmful consequences.
How to get rid of the Search Encrypt “Malware”?
Programs like Search Encrypt are often found inside different free installers, torrents, free download links, different spam messages, shareware or freeware sites and automatic setups. That’s why, to avoid them, it is best if you generally stay away from some non-reputed software sources and their free installation wizards. When you run a new setup, let’s say of some desirable new program, make sure you carefully read the EULA and customize the installer through the given “Advanced/Manual/Custom” option. Don’t use the “Standard/Automatic/Recommended” one, because this way, you may unknowingly give permission to some potentially unwanted program (or a tricky virus) to become part of your system, in case that it is bundled inside the installer.
Now, to uninstall Search Encrypt, you need to first correctly detect it. You can use the instructions in the removal guide below for that and make sure you carefully follow them. At some point, you may need to interact with important system files, so double check what you have to delete before you do anything and, in a case of a doubt, scan your system with the professional tool. It will help you identify the correct browser hijacker files and eliminate them without any risk for your system.
SUMMARY:
| Name | Search Encrypt |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
How to Remove Search Encrypt Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply