This page aims to help you remove Search.hr “Virus”. These Search.hr “Virus” removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
The following article features a full and thorough description of a program named Search.hr “Virus”. As being classified as a typical browser hijacker, it might work in this annoying way:
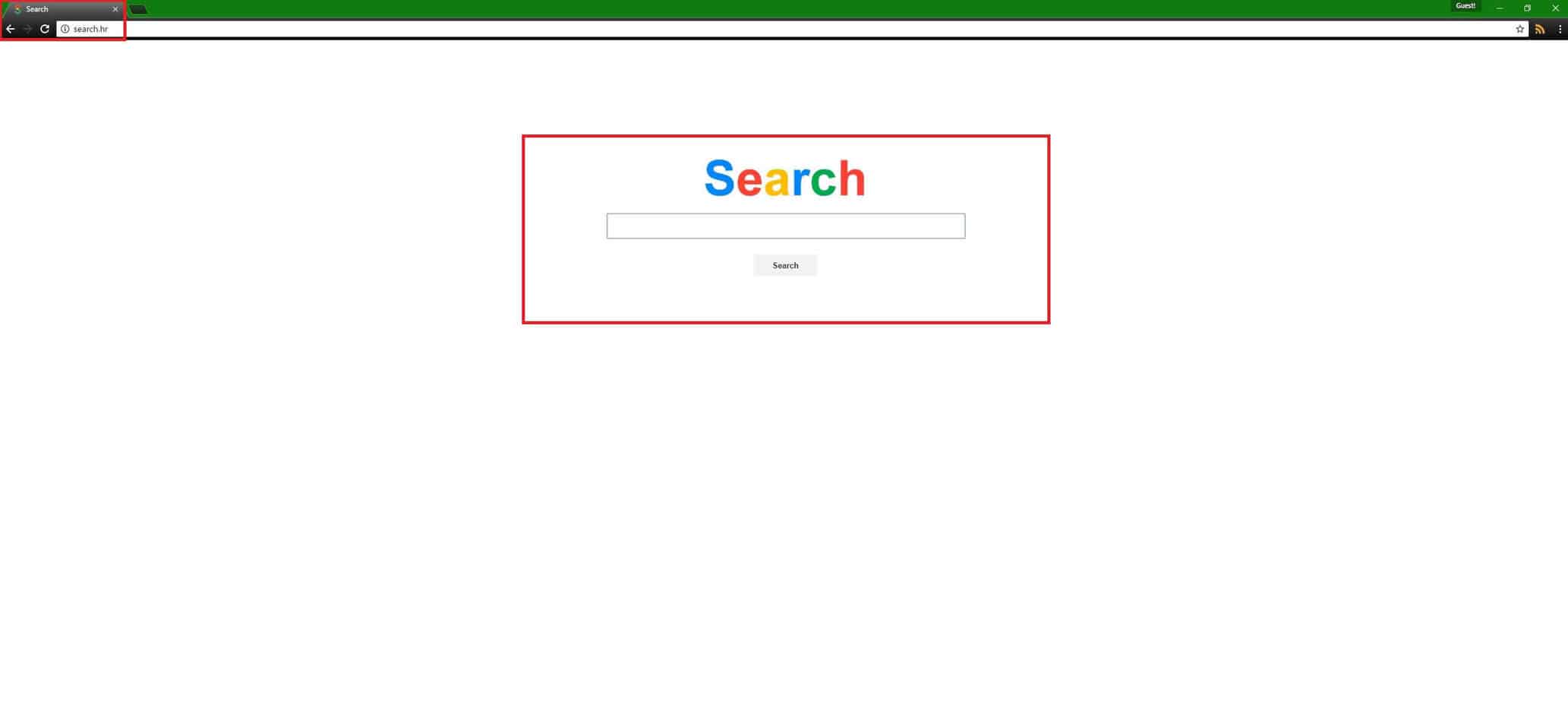
- Search.hr “Virus” could infect your computer with your unwilling (uninformed) approval and modify your browser apps after that. Neither Explorer, nor Opera, Firefox and Chrome might be safe when it comes to browser hijacker-related infections. Of course, all the other existing browsers could potentially get affected, as well.
- The way such a program might change the browser apps installed on your PC involves programming them to redirect you to unknown and unfamiliar web locations (normally to webpages you haven’t asked your browser to open).
- Furthermore, such a hijacker may result in the broadcast of a big number of online ads such as boxes, banners and/or pop-ups, which might irritate your web surfing activities.
- Also, Search.hr “Virus” may even substitute the homepages and/or search engines you usually use with new ones.
More details about browser hijackers in general, as well as about this specific version, are available in the text below.
A glance at the essence of all browser hijackers:
Search.hr “Virus” and all the programs related to it are normally seen as harmless. Still, all the existing hijackers could sometimes show somehow questionable features. Some of these suspicious traits include getting access to your browser’s databases and reviewing the information from there for the purpose of guessing what kind of products and services you might be interested in. Following that, you are likely to see just the pop-ups, the content of which supposedly matches your preferences and interests. However, the intensive ad production might make your machine slow down a bit. This possible negative consequence is entirely dependent on the processing power of your computer, though. Not every affected user experiences it.
The answer to the question, which is bothering you most: is this kind of software a virus or not?
Fortunately, there is absolutely no relation between the existing hijackers and any truly malicious programs. Nevertheless, we want to make the differences between them clearer by giving you an example. In order to show you that, we will compare a Ransomware version and Search.hr “Virus” (as an exemplary hijacker):
- You already know what Search.hr “Virus” is capable of. Any typical Ransomware program functions in an entirely different way. For example, when it comes to the way the two compared programs enter your PC, we can say that the virus will sneak into your system, research your hard disks in order to determine which your most favorite data is and will normally continue with encrypting it. A ransom-requiring notification will later be generated, informing you that your files are now inaccessible and you are supposed to pay ransom in exchange for them. Compared to that, a few browser-hijacker-invoked ads and redirections are nothing.
What is the most likely way to catch a program like Search.hr “Virus”?
As you may expect, no user in the world will willingly accept the installation of such programs like hijackers and Adware that will do nothing but disturb their browsing. That’s why their developers have to be especially creative in order to spread them in legal ways. One of the most common LEGITIMATE way of distributing advertising software is via the famous program bundles. These bundles represent many various apps, programs and games mixed together and offered for free on the Internet. Indeed, many bundles may contain some very fascinating programs and may really encourage you to download and try some for free. However, there is the point when you have to be especially careful – no bundle will infect you with hijackers or Adware on its own. You are the one who authorizes and controls the installation process. That’s why you should:
Master the way of installing bundles (and any other software) wisely and properly:
Here is the most basic advice:
- These installer options should always be ignored: Recommended; Easy; Automatic; Default; Quick. They will implement an automatic installation of the WHOLE CONTENT OF THE PARTICULAR BUNDLE or ALL THE FEATURES OF A GIVEN PROGRAM/APP. In this way, all sorts of infections may occur, as well as some unwanted modifications of your system as a whole.
- These installation features should always be preferred: the Customized or the Advanced. By choosing them you will get the control over the installation process and have the chance to opt in or opt out of features and programs.
Practice implementing a safe uninstallation process, as well. For that purpose, follow the steps we have prepared for you in the Removal Guide below.
SUMMARY:
| Name | Search.hr |
| Type | Browser Hijacker |
| Detection Tool |
How To Remove Search.hr “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment