This page aims to help you remove Search SweetIM. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
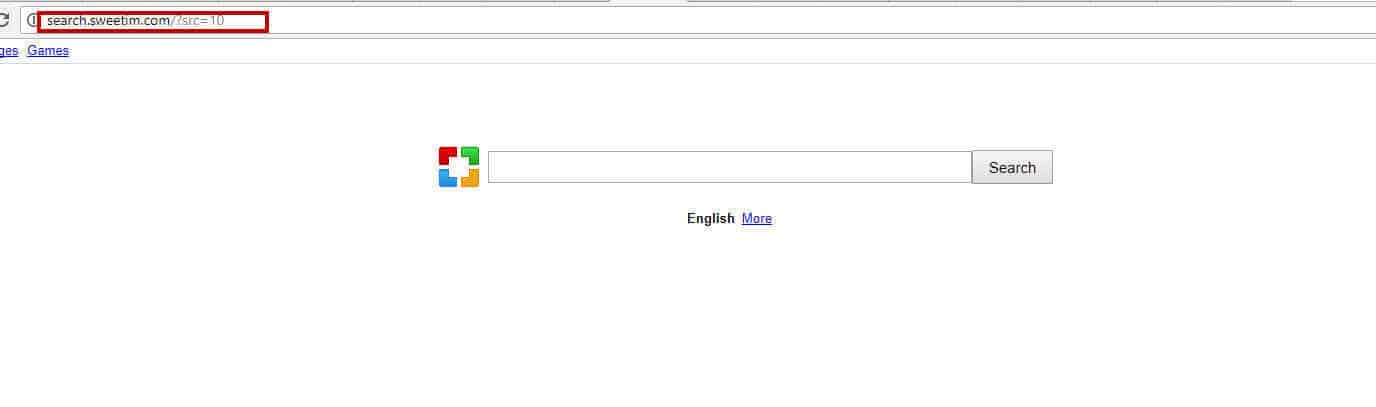
SweetIM is a browser hijacker, designed to redirect online users to certain sponsored web locations. This program often installs a new search engine or homepage to your Chrome, Firefox or Internet Explorer and starts to generate various pop-ups, banners, and ads on your screen while you are browsing the web. In fact, the new search engine is nothing more than a potentially unwanted component that is used to generate pay-per-click revenue. Oftentimes, the users who are exposed to the browser hijacker’s activity complain that this software creates chaos on their computer by changing the browser settings and starting to continually redirect their searches to various insecure domains. If you’ve already noticed redirection activity to some sites that you don’t know or don’t want to interact with, it’s a good idea to scan your computer with reliable antimalware software. On this page, you can find such software, or alternatively, you can try to manually detect and remove the browser hijacker with the help of the removal guide below. Fortunately, SweetIM is not as serious as a real virus (such as a Trojan horse, Ransomware or Spyware), so you do not have to be a genius to remove it from your system. All you need to do is to carefully follow the instructions in the next lines and run a deep scan with the professional removal tool.
Is it worth adding Search SweetIM to your browser?
As we have already mentioned above, many people, who face browser hijackers like SweetIM, find their activity quite annoying. The reason is such software can “occupy” Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, Safari, and other browsers installed on your computer. Once it has become part of your system, the hijacker forces you to use an unreliable search engine that is known to provide users with incorrect search results and misleading text ads. The most unpleasant feature of this browser hijacker is the tendency to lead you to insecure pages or sketchy ads that prompt you to click on them and are usually very hard to remove. If you want to be safe, you should be very careful with any search result, provided by SweetIM, since you never know how safe it is and where it may lead you to.
Generally, browser hijackers are not considered malicious, since it does not contain harmful codes and its primary purpose is to advertise and bring profits through clicks. However, if you notice that your browser is redirecting you to gaming sites, aggressive sales offers, adult content, or other sketchy web locations, it is advisable to remove the hijacking software before you have unknowingly bumped into some well-camouflaged Trojan horse or Ransomware cryptovirus. This is the main reason why we recommend uninstalling SweetIM once you have found that this program has managed to take over your browser.
Finally, we also want to warn you of the tracking cookies that go along with this hijacker. The program usually installs some data-tracking components, which are typically used to track computer users and collect non-personal data, such as most commonly used search terms, most visited web pages, location, and other similar details. The developers may claim that this information is used for marketing purposes, however, you should consider the possibilities of this data being compromised and falling into the hands of some hackers. They can use it as and when they want and this will do no good for you.
Spreading browser hijackers on the internet
Potentially unwanted programs (PUPs) of this type are typically distributed using a bundling technique. This technique is normally used by the browser hijacker developers to hide unwanted applications as extra components in free software installers, different torrents, installation managers, automatic wizards, shareware platforms and free download links. Unfortunately, this method has proven to be quite effective. Its effectiveness consists in hiding the hijacker under “basic” installation mode. When installing new software, the majority of users do not pay attention to prearranged fields that allow the installation of optional software. So if you are currently dealing with SweetIM, you should know that it has probably infiltrated your system that way.
Fortunately, there is a very easy way to protect yourself from the installation of potentially unwanted programs. You basically have to choose User, Custom or Advanced settings and unmark the apps that have been suggested to you. In case you found these tips after installing the browser-hijacker on your system, below you will find a detailed removal guide with step-by-step instructions on who to uninstall SweetIM and remove all of its components from your browser. Additionally, the SweetIM removal tool can also check your operating system and detect other files, that may cause harm.
SUMMARY:
| Name | SweetIM |
| Type | Browser Hijacker |
| Detection Tool |
Search SweetIM Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment