Sextortion email scams are a popular way for hackers to extort money from unsuspecting web users. If you are reading this page, you have most probably received a strange email message from a self-proclaimed hacker who claims to have compromised your computer through a Trojan Horse thus obtaining embarrassing photos and videos of you. This is known as a sextortion email scam and recently there’s been a new wave of these emails all over the Internet. Notable examples of Sextortion Email Scams are the Save Yourself Email Scam and Drive By exploit email malware .
What is a Sextortion email?
A sextortion email is a particularly unpleasant email BitCoin scam. The sextortion email’s purpose is to threaten and intimidate the victims so they would pay a ransom to stop the blackmailers from releasing compromising content.
Sextortion email examples:
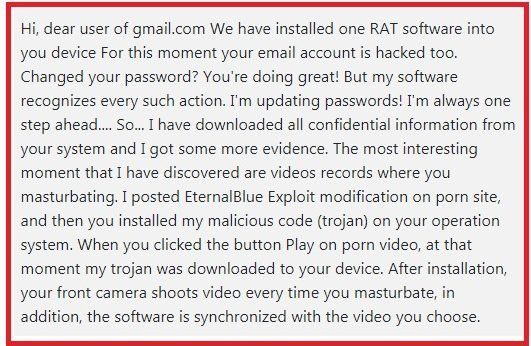
Sextortion Email Scam
The online crooks behind the sextortion email usually send a message where they state that, with the help of a Trojan Horse hidden inside the machine, they have accessed some sensitive personal information, mostly images and videos related to nudity and porn, your email passwords, etc. The blackmailers threaten to distribute that information everywhere online, including to your contacts list and social media, if you don’t pay a certain amount of money to their BitCoin wallet within a given deadline. The good news is that receiving sextortion email messages does not automatically mean you have been infected with a Trojan Horse or another malware. In most cases, such messages are just a bluff, created to scare the web users into sending money to the extortionists.
How does the Sextortion scam work?
A sextortion scam is an email hoax which has been around the web since the middle of 2018. The sextortion scam’s creators would use different tricks to panic the receivers of the sextortion message into believing their device has been compromised by a malware.
Sextortion scam reports:
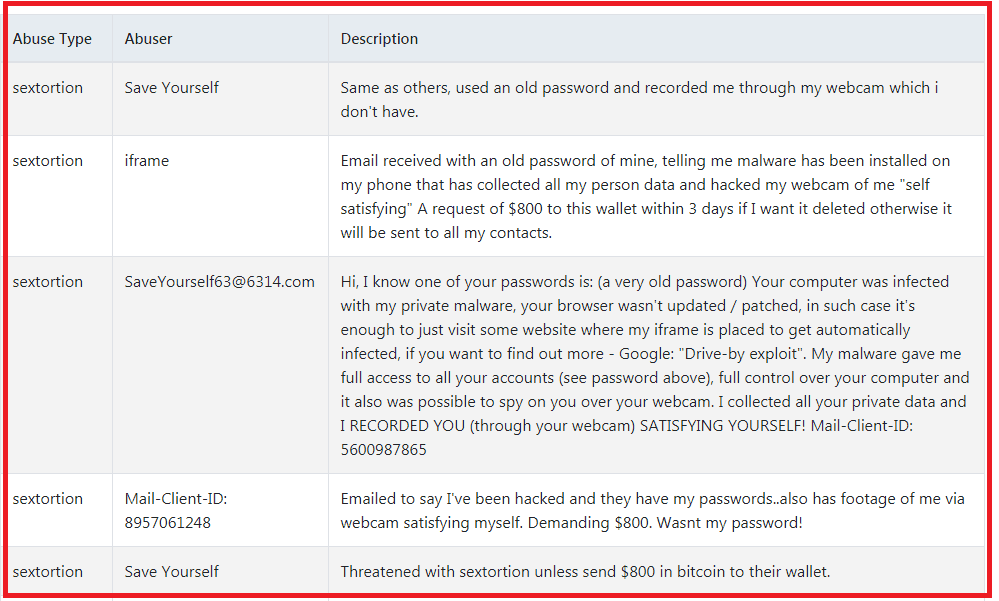
Examples of a sextortion scam
Criminals would often try tricking you into thinking they have obtained your real password or have hacked inside your webcam or mic via a hidden malware. They might even show you your old password or other personal information. Such tricks, however, are not solid proof that your machine has really been infected nor compromised. In most cases, the “hackers” don’t have any videos, photos or other compromising materials. They simply use information they’ve gathered from online data breaches or other accidental personal information leaks to scare you. Users who do their research quickly realize that this is a hoax and they don’t need to believe the email or send money to anyone.
Yet, sometimes, such emails may indeed be a result of a hidden infection such as a Trojan Horse. Therefore, even though there generally is no need to stress too much about the sextortion emails, it is a good idea to use a professional security tool and scan your computer. The guide below and the attached removal tool will help you check your system for hidden threats and remove them if there are any. It is also advisable to change your email’s password as an extra safety measure.
SUMMARY:
| Name | Sextortion Email |
| Type | Trojan |
| Detection Tool |
Remove Sextortion Email Scam Trojan
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment