The Shorturl.at Virus
The Shorturl.at Virus is a term that has been used to describe malicious activities associated with the misuse of the URL shortening service shorturl.at. Before we delve into this, it’s important to understand the context in which a URL shortening service like shorturl.at can be involved in cybersecurity concerns:
- Malicious Link Masking: Shortened URLs can be used to disguise harmful links. Because the actual destination of the link is hidden, attackers often use services like shorturl.at to trick users into clicking on links that lead to phishing sites, malware downloads, or other deceptive content.
- Phishing and Scams: Phishers may use shorturl.at to create links that appear harmless but redirect users to fraudulent sites where personal information can be stolen.
- Distribution of Malware: Malicious actors might use shortened URLs to distribute malware. Unsuspecting users click on a seemingly benign link, which then leads to a site that automatically downloads viruses, spyware, or other types of malicious software onto their device.
- Spam Campaigns: Shortened URLs are often used in spam campaigns, as they can bypass security filters that typically identify and block known malicious URLs.
Shorturl.at may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
That being said, it’s crucial to clarify that the service provided by shorturl.at itself is not inherently malicious and falls into the category of page-redirecting and ad-generating software such as browser hijackers. The platform is a tool for URL shortening, which has many legitimate uses, but the potential for misuse arises from how others choose to use the shortened links. Users affected by the Shorturl.at virus may notice a pop-up notifying that “Shorturl.at wants to show notifications”. If allowed, this could enable unauthorized alterations to their homepage and search engine settings, leading to recurrent redirects to predetermined websites.
Shorturl.at is an online service that provides URL shortening. This tool allows users to convert long URLs into shorter, more manageable links. Such shortened links are often easier to share, especially on social media platforms, in text messages, or in email communications where space is limited or where longer URLs might break. The service generates a concise link that redirects to the original, longer URL when clicked. This can be particularly useful for marketing, tracking click rates, or simplifying complex web addresses for easier dissemination.
The safety of using shorturl.at, like many URL shortening services, can vary. Generally, the service itself is legitimate and safe to use for creating shorter URLs. However, because shortened URLs mask the original destination, they can potentially be used to hide malicious websites. This means that while creating and sharing links via shorturl.at might be safe, clicking on shortened links from untrusted sources carries a risk. These links could redirect to phishing sites, sites containing malware, or other harmful content. Therefore, it’s advisable to use URL shortening services judiciously and be cautious when clicking on shortened links, especially if they come from unknown or untrusted sources.
Shorturl at
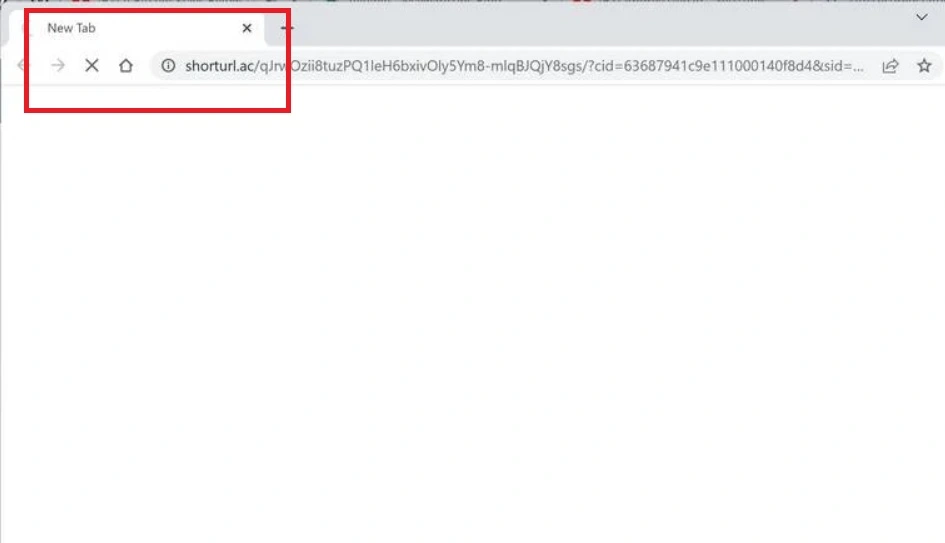
In the course of our research, we came across a user’s experience that delves into the potential threat of Shorturl at on iPhones. The user explained an incident where their curiosity led them to a Twitter thread about TikTok. As they scrolled through the intriguing content on their iPhone, a mishap occurred when they accidentally clicked on a seemingly sketchy link (the user shared the appearance of the “Soocaips.com/4/6235628” and “Shorturl.at/psyIK” links.), redirecting them to a peculiar webpage that they promptly closed.
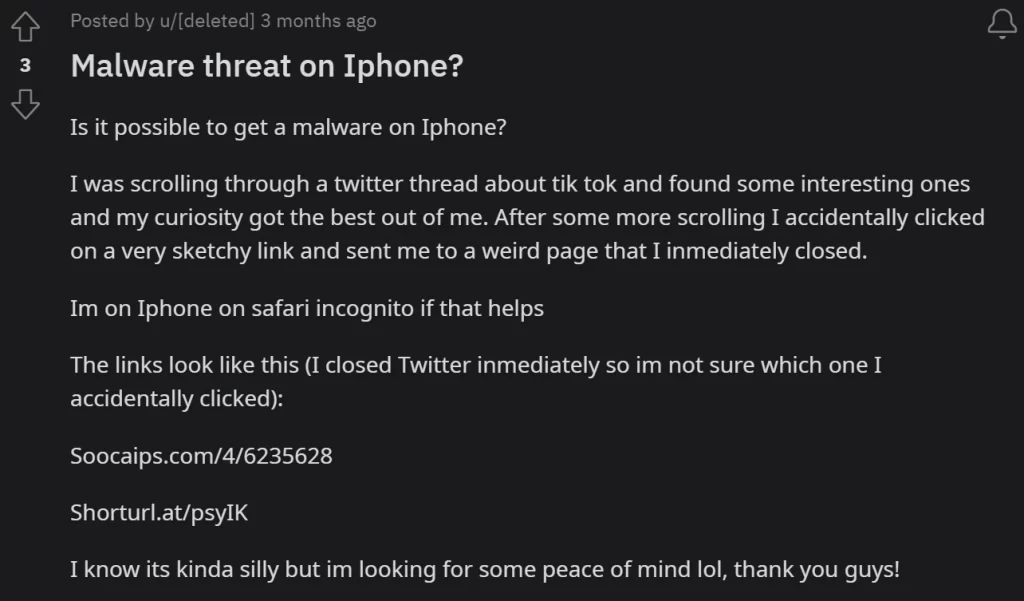
Despite swiftly closing Twitter and not being certain which link was inadvertently clicked, the user expressed concern, particularly as the websites seemed to fall into the category of commonly encountered ones claiming the user had won a cash prize or warning about a virus. What compounded their unease was the realization that it wasn’t a pop-up or a secondary window that opened but rather a direct interaction with the questionable website.
If you have a similar experience and want to protect yourself, we recommend you to follow the instructions in the Shorturl at removal guide below. Also, in the future, be cautious when clicking on shortened links, especially if they come from unknown or untrustworthy sources. Use security software that can detect and block malicious websites, and consider using tools or browser extensions that reveal the true destination of a shortened URL before you click on it.
SUMMARY:
| Name | Shorturl.at |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Shorturl.at Virus Removal
To try and remove Shorturl.at quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Shorturl.at extension (as well as any other unfamiliar ones).
- Remove Shorturl.at by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Shorturl.at and any other suspicious items.
If this does not work as described please follow our more detailed Shorturl.at removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Shorturl.at app and kill its processes
Uninstall the Shorturl.at app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Shorturl.at. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Shorturl.at, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Shorturl.at.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Shorturl.at changes made to different system settings
Undo Shorturl.at changes made to different system settings
It’s possible that Shorturl.at has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Shorturl.at from your browsers
Remove Shorturl.at from your browsers
- Delete Shorturl.at from Chrome
- Delete Shorturl.at from Firefox
- Delete Shorturl.at from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.


Leave a Reply