This page aims to help you remove Snatch for free. Our instructions also cover how any .Snatch file can be recovered.
Snatch Ransomware
Snatch is a ransomware infection that can extort money from web users by encrypting their files without their knowledge. Snatch demands a fixed amount of money from its victims in order to provide them with a decryption key needed to liberate their files from the encryption.
In the case of an infection with a Ransomware like Snatch , most users feel shocked, scared, and confused. After all, the Ransomware viruses are considered as some of the most harmful forms of online threats and the main reason for that is their ability to make it almost impossible for the victims to open their most important files stored inside the attacked machine’s hard-drives. That’s why many web users are ready to try every possible alternative that could potentially help them remove the infection and recover whatever could still be recovered. With this in mind, on this page, we have added a comprehensive removal guide that explains how to remove Snatch as well as how to recover your files from system backups whenever this is possible.
The Snatch virus
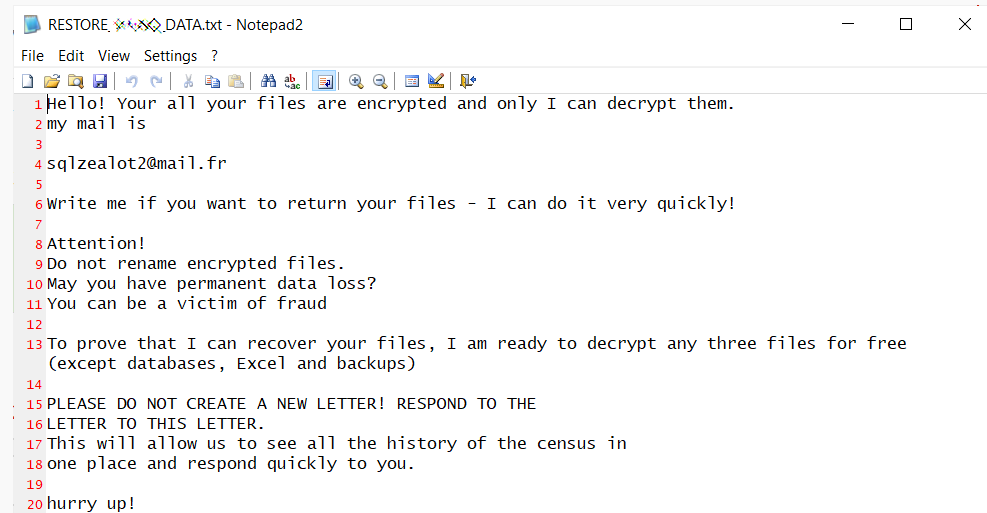
The Snatch virus is a money-extortion infection designed to encrypt user data and demand a ransom for its decryption. After the attack, the Snatch virus typically displays a ransom-demanding message on the screen of the victims and requests a money transfer to a given cryptocurrency wallet.
Ransomware viruses such as Snatch are incredibly lucrative pieces of malware that generate huge profits for their criminal developers. One of the factors that has proven to be very beneficial to the popularity of these threats is the fact that most antivirus programs do not detect the ransomware-based viruses in the system. This is because the file-encryption, in general, is a method that does not destroy or corrupt anything on the system. And since there is no actual damage, there is nothing that can trigger an action from your security software. The file encryption is simply used to keep digital data inaccessible to those who don’t have the matching decryption key. Therefore, if you get infected with Snatch , there’s little to no chance that you’ll get warned about the infection before your files get encrypted and the ransom-demanding notification gets displayed on your screen.
The Snatch file decryption
The Snatch file decryption is a sophisticated procedure that can decipher the information that has been encrypted and return it to its previous state. To activate the Snatch file decryption procedure, the victims need a special decryption key which the hackers offer in exchange for a ransom payment.
Nonetheless, we may give you some alternatives to paying the ransom and you should definitely give them a try because complying with the ransom demands of the cyber criminals behind Snatch does not give you any guarantee about the future of your files and your computer. In fact, the statistics show that there is a large number of victims who have transferred huge amounts of money to pay the ransom and and have gotten nothing in return. Oftentimes, the crooks behind the ransomware either disappear without sending a decryption key or they send a key that turns out to be ineffective and fails to recover the encrypted data. So, instead of risking their money, we encourage our readers to first remove Snatch from their systems (which will keep it from further encrypting new data) and then give a try to the file-recovery section from the guide below.
SUMMARY:
Remove Snatch Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply