This page aims to help you remove SoundMixer.exe Virus. Our removal instructions work for every version of Windows.
SoundMixer.exe
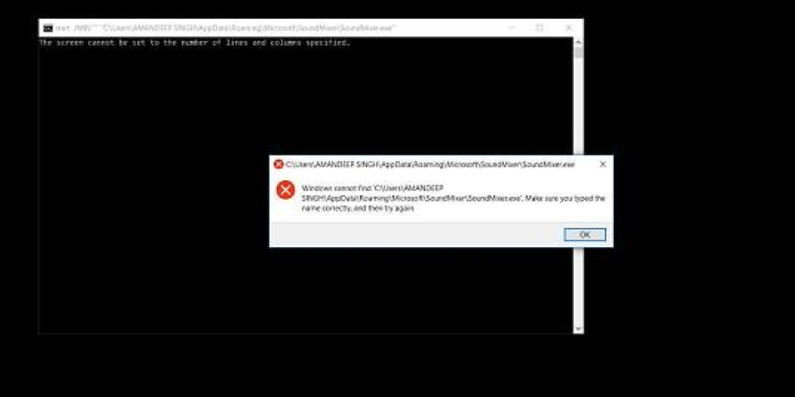
The Soundmixer.exe virus classifies as Potentially Unwanted Program (PUP). These types of programs corrupt important files of your OS and add their own entries in the system. Once installed, SounderMix.exe triggers a variety of errors and damages every aspect of your daily computer activities.
The information on this page might be exactly what you need if your system has been infected with a malware called SoundMixer.exe. Here, we will talk about the specifics of this new online threat, its malicious abilities and the most effective methods to remove it from your PC. We will also give you some helpful information on prevention and protection, so don’t miss the next lines and stay with us until the end. There, you will find a detailed Removal Guide and a trusted malware removal tool, both of which you can use to remove SoundMixer.exe Virus from your system. After all, you don’t want this Trojan to corrupt your machine or turn you into a victim of a cybercrime, right?
The SoundMixer.exe Virus
The Soundmixer.exe Virus also exists in the internet space as smvss.exe or Sound Mixer. It is included already into the list of potentially unwanted programs (PUPs) and should be avoided. If your screen shows a Soundmixer.exe error, you have to scan with professional anti-malware software, because of the probable presence of PUP or crypto-miner on your PC. Malwares, as you have probably heard already, are very dangerous computer threats.
Most of the computer users look at them with fear because these infections can cause really serious issues. What is more, in many cases no one can tell you what exactly these issues could be. The criminals, who develop such types of malware, use those viruses for a number of criminal tasks and they can usually reprogram Trojans and make them carry out tasks that are different from the initial purpose of the virus. This means that if SoundMixer.exe has managed to sneak inside your computer, it can do all sorts of criminal deeds. For instance, you should be prepared to face various kinds of system malfunction, sudden crashes, system errors and unusual unresponsiveness to some of your software and system processes. This could be a result of the attempts of the Trojan to manipulate vital system tasks and gain remote control over them. SoundMixer.exe Virus may also provide the hackers with complete access to the PC and all the information that you keep on it. They can easily steal your files, delete or corrupt them, gain access to some confidential information about you, your work and your personal life and family or steal your usernames, passwords, banking details and credentials. And this is not everything – with the help of SoundMixer.exe, any nasty virus, including Ransomware, get snuck into your system and cause even more harm. Trojans often operates as a backdoors and provides cover for various other infections to perform their malicious tasks. Still, it is difficult to determine the exact purpose and aim of a Trojan infection in each separate instance unless the consequences of the infection have already become apparent. That’s why, we urge you to remove SoundMixer.exe immediately in order to prevent harmful consequences similar to the ones, described above. Use the instructions in the Removal Guide below or the professional SoundMixer.exe removal tool for assistance.
SoundMixer.exe tries to remain hidden and performs its malicious task in secret!
It is typical for Trojan viruses to use stealth in order to infect the victim’s computer. SoundMixer.exe, for instance, may appear as a legitimate-looking software update request, a free download link, an interesting web ad, a file, an email attachment or anything else really. The moment you click on the piece of content that is used to distribute the malware, however, you will likely get infected without any visible indication. Sadly, you may not even come to know about the threat unless your antivirus detects it or unless some major system malfunction indicates the presence of the virus.
How to stay safe?
Dealing with SoundMixer.exe is important but keeping your machine safe in future is also an something that should be taken care of. Protecting your PC from future infections is the best way for dealing with any sort of malware. For that, we advise you to improve your system’s safety in a number of ways. First, you should update your OS to the latest security patches. Make sure you also update any software on your PC which you regularly use and uninstall those programs that are simply lying around taking up space and providing potential vulnerabilities for the hackers to exploit. An outdated program could easily be compromised and is an actual vulnerability for your computer. Investing in good antivirus software is also a must. In most of the cases, if provided with the latest virus definitions, a reliable security tool should be able to detect most Trojan threats on time (even new ones like SoundMixer.exe) and notify you about them. Of course, when it comes to prevention, you should be really careful and vigilant when browsing the web – don’t click on everything suspicious that might pop-up on your screen and stay away from sketchy and unfamiliar web pages.
SUMMARY:
SoundMixer.exe Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Reply