[email protected]
[email protected] is a typical ransomware cryptovirus that can function on most Windows operating systems. [email protected] encrypts the files on the infected machine and then blackmails its victims for money.
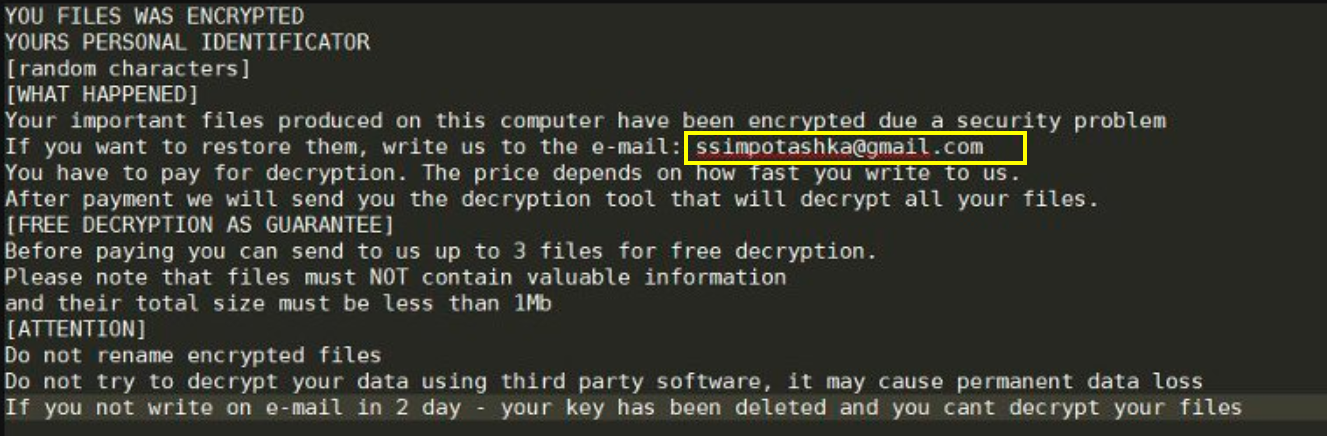
To be more specific, [email protected] demands that the victim users pay a certain amount of money in exchange for a decryption key. And this decryption key, in turn, is needed in order to undo the encryption of the virus. After [email protected] has encrypted your data, you will find that it becomes utterly useless. No software or program will be able to recognize the format of the data, and therefore it will not be able to be opened or viewed.
Ransomware such as [email protected] can affect most commonly used data types, such as images, videos, audio files, MS office and other such documents, etc. And if you happen to be a company or organization, the consequences of an attack like this can prove to be quite disastrous. This is why ransomware has become a highly profitable extortion scheme. And thanks to the emergence of Bitcoin and other cryptocurrencies that provide full anonymity for their transactions, the cyber criminals who are responsible for these viruses have pretty much lost any and all fear of persecution.
The good news, however, is that you aren’t doomed to have to empty your pockets in order to get your data back. There are alternative means available to you, and in the following removal guide we will tell you about some of them. But what’s no less important is that you follow the steps in the first part of said removal guide, as these will help you locate and remove [email protected] from your system. If you do not do this, any files you manage to decrypt or otherwise recover will most likely get encrypted immediately after.
The [email protected] virus
The [email protected] virus usually operates in complete stealth and most antivirus software proves helpless to counteract it. Variants like the [email protected] virus are, therefore, best prevented from entering your system than fought off post-infection.
The hackers typically use a handful of common techniques for the distribution of this and other malware types. For example, malvertisements (which is fancy talk for fake online ads) are one of the leading methods of distribution for ransomware like [email protected]. Hence, we would recommend trying your best to minimize your interaction with any and all online ads.
Next up are the traditional spam messages (emails, social media, etc.) that seem to never get old. These usually contain and attached file that may seem harmless, but actually contains the virus. And another very common way of getting infected is by interacting with pirated or illegal content that you can download from various sketchy sources.
Now that you know the potential ransomware sources, you can learn to avoid them better. But perhaps the best way to ensure your immunity to such attacks is to back up your files on a regular basis and keep copies stored on a separate drive.
The [email protected] file extension
The [email protected] file extension prevents any program from being able to read the encrypted files. You can see the [email protected] file extension at the end of each locked file name.
SUMMARY:
[email protected] Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply