This page aims to help you remove the StartFenster Virus. These StartFenster removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
You are interested in our article because the program we are discussing here – StartFenster, has apparently caused some changes in your browser. You have probably found out your computer had been infected when you experienced the main symptoms which include the appearance of plenty of online pop-up, banner or tab ads, the replacement of your default search engine and browser homepage or unusual redirection to certain online locations, every time you try to use your browser, no matter whether it is Chrome, Firefox or another popular one.
StartFenster
In terms of its nature, experts classify StartFenster as a browser hijacker. Hijackers are exactly the type of software that could be responsible for the different behavior of all of your browsers, as they affect them in the aforementioned way.
Browser hijackers are not particularly harmful to your computer, though. They can only alter the usual settings of your browsers. They might annoy you with the number and the intensity of the displayed various advertisements, and such a production could result in a noticeable slowdown of your machine. However, no virus threats can be found in StartFenster’s typical behavior. Nor can this hijacker produce copies of itself, destroy any data on your PC or steal any account or banking details. It is also not able to lock up your files, as typical viruses like the Ransomware-based ones do. StartFenster could simply advertise newly-developed homepages or send you to places that are new and need to be promoted, but no hazardous effect usually come from this.
The StartFenster Virus
StartFenster is a browser add-on that hijacks the settings of commonly used browsers like Chrome, Firefox, and Edge and installs some ad-generating components in them. Thr StartFenster Virus optimizes the browser for online advertising by replacing the main search engine and the homepage URL with commercial-filled ones.
Still, some users may be concerned about the legal point of StartFenster’s nature. Actually, displaying pop-ups, boxes and other ads is NOT forbidden by any national or international law. The pay-per-click marketing applies to almost all hijackers, as this method ensures that the developers who distribute StartFenster and other ad-generating software will be paid for doing so on the basis of the number of ads you see and the ones you open. In fact, this is an excellent money-making strategy. For such money-earning purposes, many programmers include browser hijackers and Adware in the software mixtures they create. These program packages are known as bundles and contain many diverse programs. Most importantly, you can download them for free, which helps for spreading StartFenster, as users could be very much tempted to check what kind of programs such bundles contain and some might even find it necessary to use a program from such a mixture. Of course, this is not the only efficient distribution method that browser hijackers use. Other ones could be torrents and shareware, as well as movie or video-streaming web pages; spam letters and their corresponding attachments or even documents and visiting contagious websites. However, when it comes to the infection process, downloading a bundle is not the only condition. The following paragraph focuses on the actual contamination process.
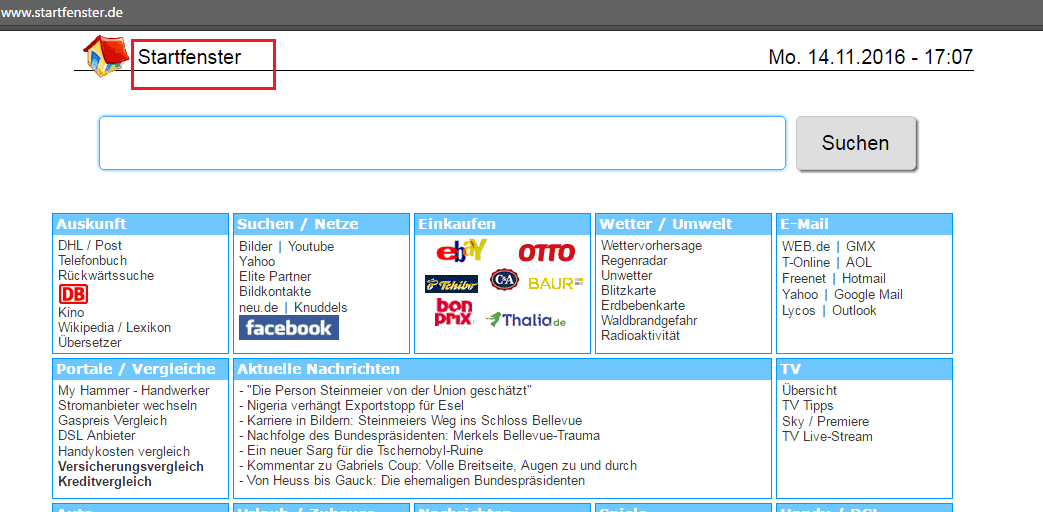
The StartFenster Virus will redirect your searches and display pop up ads
Why does the installation process always matter?
The actual infection process, in case you have caught StartFenster from a bundle, occurs only after you have allowed the program to proceed. However, you may have done that unknowingly as it usually happens. Everything depends on the feature you choose from the installer. Many people just prefer to go with the flow and select the easiest existing method by using the Default option. This is the most serious mistake you can make when it comes to cyber security, by doing that you will almost always end up catching something, either ad-displaying programs or serious threats like Trojans and Ransomware. The only sensible choice you can make while installing any program on your PC is to choose the Custom feature of the wizard and to carefully read all the agreements and licenses. Doing that will almost certainly ensure your cyber safety.
Additional advice on prevention
Of course, we can list some useful prevention tips here, which include maintaining your anti-virus program in good overall condition by updating it and renewing your license. Also, it is very important that you learn to be particularly picky when it comes to browsing the web. All kinds of suspicious software, webpages and letters in your email should be avoided. Read and educate yourself about the possible threats and you will know what to do. As for removing this hijacker, we have created a set of removal instructions below. They are very useful and not difficult to follow, so you should be hijacker-free in no time.
SUMMARY:
| Name | StartFenster |
| Type | Browser Hijacker |
| Detection Tool |
Remove StartFenster Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment