*[email protected] is a variant of Stop/DJVU. Source of claim SH can remove it.
[email protected]
The purpose of [email protected] is not to corrupt some crucial system files in your computer or to spy on your activities without you knowing it. Ransomware like [email protected] will not delete personal data from your computer or give remote control over the infected machine to the hackers who are responsible for the malware attack.
However, despite all this, ransomware viruses and their cryptovirus subcategory in particular are among the worst forms of malware that could potentially find their way to your computer and files. Unlike Trojans, spyware, rootkits and other categories of malware that may corrupt data, spy on you or block your antivirus, a typical cryptovirus would use a rather harmless computer process called file encryption to fulfill its quite nefarious purpose.
The [email protected] virus
The goal of the [email protected] virus is to make it impossible for you to open, use, edit or modify all potentially important personal data stored on your computer. The [email protected] virus uses a complex encryption algorithm to render your files completely inaccessible.
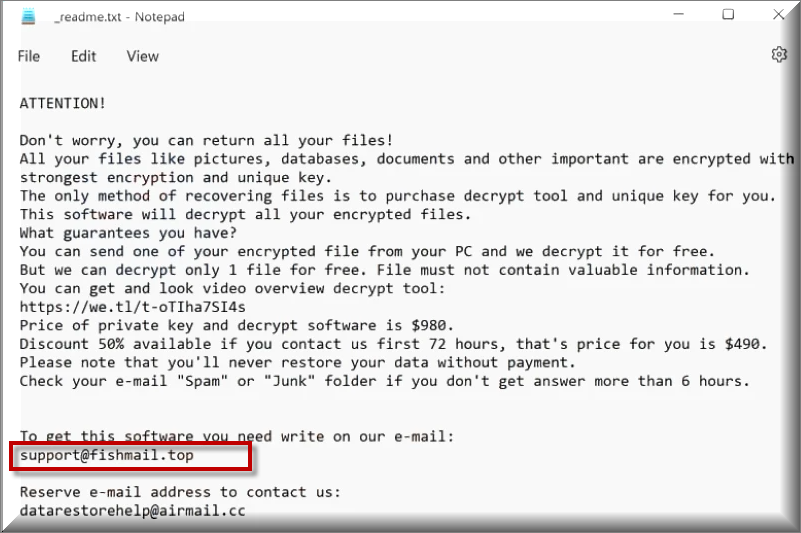
Naturally, if you find out that all important files in your system won’t open no matter what you do, you’d be eager to find a way to get them to be accessible again. This is normally the point where the hackers tell you about their “offer”, namely the option to pay them a certain amount of money (usually in the form of some cryptocurrency like Bitcoin). And in exchange, they promise to send a decryption key for your files that can allow your computer to read through the encryption placed on the data.
Of course, trusting such promises made by hackers who are blackmailing you isn’t exactly a very good option. After all, you may simply end up wasting a significant amount of money and still remain without the means to open any of your data. [email protected] is a nasty cryptovirus that works in this way and if you have come here because of this exact infection, you might want to read and apply the following removal steps that should help you eliminate the ransomware.
The [email protected] file encryption
It must be noted that the [email protected] file encryption makes the future of the locked data uncertain. You can try paying the ransom and that may still not get the [email protected] file encryption removed.
Sadly, however, even if you use the guide from this page and manage to remove [email protected] from your computer, you may still fail to recover the inaccessible data. The removal of the virus itself is typically not enough to bring down the decryption and though we have also offered our readers some potential restoration solutions for the locked-up files, we cannot promise that any of them will work for each user. Trying the guide out, however, will at least help you clean your PC which is an important step towards handling the situation as that would, at the very least, make your system safe and prevent [email protected] from locking-up any new files that get created or downloaded onto your machine.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
*[email protected] is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove [email protected] Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*[email protected] is a variant of Stop/DJVU. Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*[email protected] is a variant of Stop/DJVU. Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt [email protected] files
Ransomware threats are difficult to deal with, and the main reason for that is their encryption. Removing the malware that has encoded your data, oftentimes, does not make it accessible as it was before the attack. That’s why decrypting data encrypted by ransomware may be challenging even for specialists. Furthermore, ransomware decryption solutions may be very different for each ransomware variant. If you are determined to try everything possible to recover your files, our first recommendation is to check the encrypted files’ appended file extensions to identify the specific ransomware variant that you are faced with.
Using a sophisticated anti-virus tool (like the one on our website) to do a comprehensive virus check is a must before any data recovery can begin. After making sure there isn’t a virus, you can start to look into file restoration options.
New Djvu Ransomware
STOP Djvu is a ransomware variant that has been wreaking havoc by locking users out of their data and asking a ransom payment from them. Victims in many parts of the globe have reported becoming the targets of this threat. Files encrypted by this new variant usually get a [email protected] extension. People that have lost access to their data, however, should not give in to the ransom demands since there are decryptors, like the one at the link below, that may be able to assist them regain encrypted data.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Download the STOPDjvu executable file from the link above, and read the license agreement and the associated instructions before starting the decryption process. Keep in mind, however, that this tool may not be able to decode all types of encrypted data, particularly those that were encrypted using unknown offline keys or online encryption techniques.
If the manual steps in this article are not adequate to address the problem, you may want to turn to a strong antivirus software to get rid of [email protected] swiftly and efficiently. If you’re disturbed about the safety of a particular file, you may run a manual check of that file using our free online virus scanner.

Leave a Comment