Taargo
Taargo is a harmful software program recognized as a file-attacking Ransomware virus. Ransomware threats like Taargo are known for using data encryption in order to make their victims’ files inaccessible and then ask for a ransom payment for the decryption key.
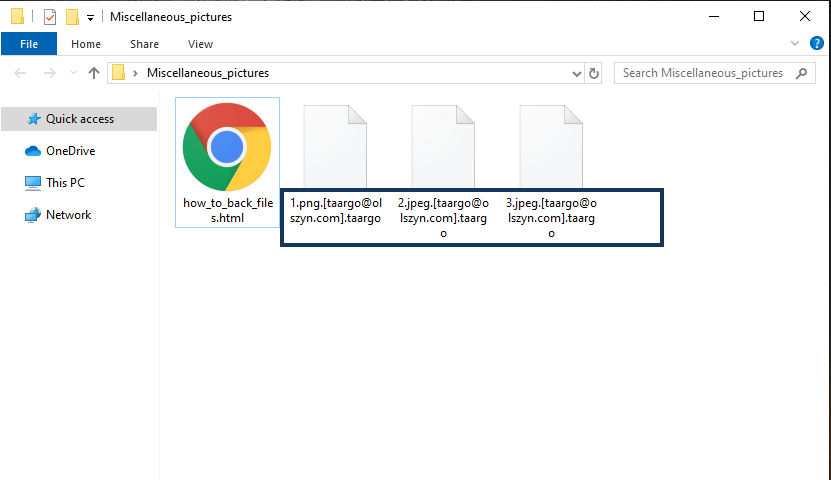
The Taargo Ransomware will encrypt your files and leave a message in a how_to_back_files.html file.
This is currently one of the most widespread forms of malware and even though most Ransomware viruses only lock the user’s files without causing any damage to the infected system, they can still be particularly problematic. This is especially true if the attacked user has some highly important data files stored on the computer that haven’t been backed up. Backing up important data is a very good practice in general and it is even more so when it comes to keeping files safe from Ransomware attacks. If you have backed up your valuable files on an external drive or using a cloud service, the Ransomware that attacks your computer won’t be able to get to the backup (unless you connect it to your computer while the virus is still there) and you will still have safe and accessible copies of the files you value the most.
One of the main reasons encryption Ransomware is such an effective type of malware is because most users don’t have the habit of backing up their important files, which gives the hackers behind Taargo and other similar threats the needed blackmailing leverage when the virus attacks and locks the files on the computer.
The Taargo virus
The Taargo virus is a file-encrypting Ransomware virus that targets the most important files on the attacked machine and blocks them. The Taargo virus then places a banner or a notepad file on the Desktop where the ransom payment instructions are specified.
Many users who really value those of their files that have gotten locked go straight for the ransom payment in hopes of bringing their data back as quickly as possible. Although this may work in a lot of cases, be it at a certain cost, it is generally inadvisable to pay the money as your first course of action. You simply cannot know how honest the hackers are in their promises of giving you the correct decryption key for your files after you complete the payment. Also, there may be alternatives that might help with the restoration of your files without the need for you to send your money to the hackers. Some potential alternatives will be explored in our Taargo removal guide that you can find below this article.
The Taargo file extension
The Taargo file extension is a special string of letters that is added to the names of the encrypted files in place of their original extensions. The Taargo file extension isn’t a real file extension because it doesn’t match any existing data format.
This extension keeps your locked files unrecognizable to any program you may have or download and it cannot be removed manually. The only way to make the extension go away is by decrypting the files. In our guide, we will offer you some possible alternative methods of recovering your data and we advise you to try them first, instead of going straight for the ransom payment. Also, be sure to remove the virus before you try the recovery suggestions so as to prevent future encryption of your new or restored old files.
SUMMARY:
| Name | Taargo |
| Type | Ransomware |
| Detection Tool |
Remove Taargo Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment