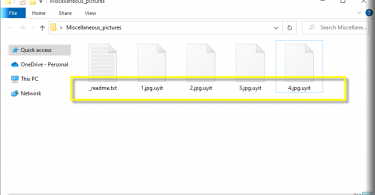
*Uyit is a variant of Stop/DJVU. Source of claim SH can remove it. Uyit Uyit is a ransomware cryptovirus that targets most popular file types on the computers of its victims. Uyit encodes these files using a complex encryption algorithm, thus...
Tag - STOP ransomware
Aawt Virus
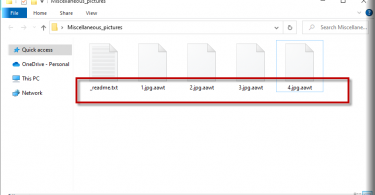
*Aawt is a variant of Stop/DJVU. Source of claim SH can remove it. Aawt Aawt is a virus of the Ransomware file-encrypting variety and it is capable of blocking all important data on your computer. The purpose of Aawt is to force you to make a...
Qqri Virus
*Qqri is a variant of Stop/DJVU. Source of claim SH can remove it. Qqri Qqri is a ransomware virus that belongs to the file-encrypting subtype. This makes Qqri among the most dangerous types of malicious code in existence. Every year ransomware...
.Kolz Virus
.Kolz .Kolz is a ransomware computer virus that will scan your computer for certain data formats and encrypt all files that belong to them. The goal of .Kolz is to blackmail you for the access key to the files that it has locked with the encryption...
.Npph Virus
.Npph .Npph is a harmful PC virus that can infect computers with the Windows OS and lock up the user files located on them. The goal of .Npph is to keep the targeted files inaccessible until the computer’s owner issues a ransom payment. This type of...
Kook Virus
.Kook .Kook is a malicious computer program used as a blackmailing tool that is able to block access to important user data. .Kook launches a data encryption process the moment it enters the system and usually shows no symptoms while encrypting the...
Vawe Virus
Vawe Vawe is a harmful Windows PC virus that will put your data under lockdown and keep it unavailable until you pay a ransom. Vawe can be described as a file-encrypting Ransomware virus that seeks to extort money from its potential victims. The...
Usam Virus
Usam Usam is a ransomware virus of the file-encrypting subtype. This means that Usam applies an encryption algorithm on specific target file types when it infects a computer. However, these are file types are numerous and pretty much include all the...
.Tabe Virus
.Tabe .Tabe belongs to the class of malicious code known as ransomware. More specifically, .Tabe falls into the subcategory of file-encrypting ransomware. If .Tabe has infected your computer, then you were likely informed about this via a desktop...
Kkll Virus
Kkll Kkll is malicious piece of code that locks all of your valuable files and then asks you to pay ransom for them. In order to restrict access to the victims’ files Kkll applies data encryption and changes the file extensions to its own. If...