Usam
Usam is a ransomware virus of the file-encrypting subtype. This means that Usam applies an encryption algorithm on specific target file types when it infects a computer.
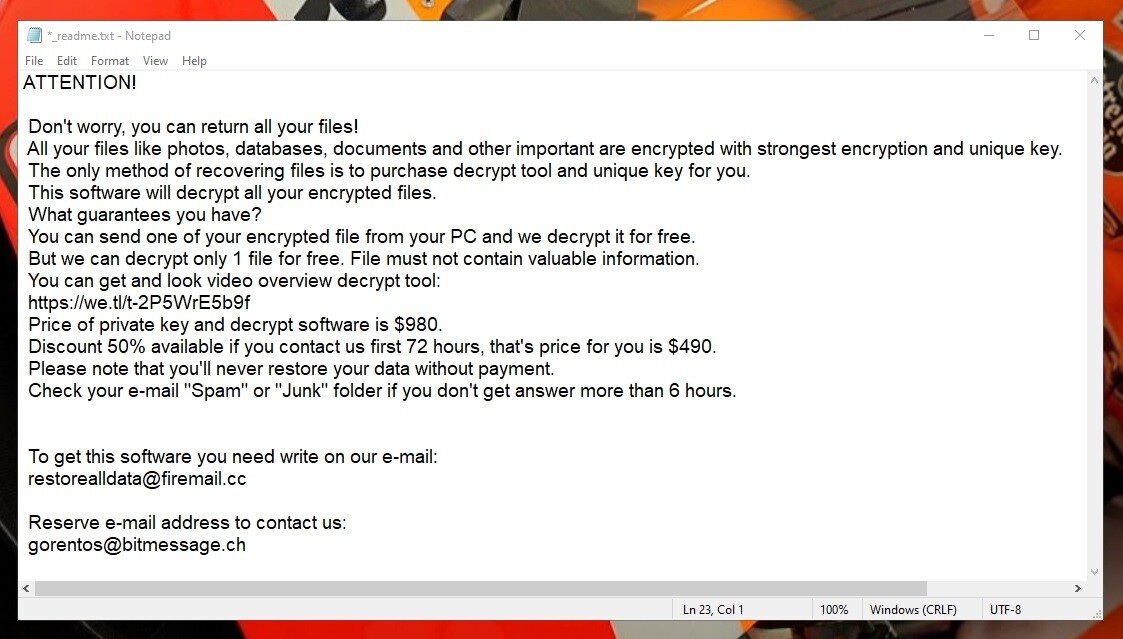
The Usam Virus ransom message
However, these are file types are numerous and pretty much include all the most commonly used formats. For example, Usam will most likely have encrypted your images, videos, music, any office documents, PDFs, etc. And what this means in layman’s terms is that as a result of Usam’s activity on the infected machine, all these files will become inaccessible to the victim. There won’t be a program or software application in existence that could possibly open or read these files, hence you won’t be able to use them.
That is, of course, unless you decide to pay the hackers behind Usam a hefty amount of money in bitcoin (or whatever other cryptocurrency they demand) in exchange for a decryption key. The decryption key, in turn, is unique for each instance of infection. And after you receive it, it is said to reverse the encryption and make your data usable again. But that’s in theory.
In fact, this classic blackmail scheme is quite flawed and there’s actually no guarantee that you will in fact regain access to your precious information. There are many things that can go amiss and we won’t waste your time trying to list them all. But what is important to know is that you also have other options, and none of them will require you to send your hard-earned cash to some anonymous cybercriminals.
We have put together a detailed removal guide for you just below this post, which we encourage you to follow in order to remove Usam from your system. And after you’ve done that, you will reach the second part of the guide, which contains alternative file recovery methods.
The Usam virus
The Usam virus uses a strong encryption algorithm to lock its victims’ files. However, although the process can take a long time to complete, the Usam virus typically runs in the background without exhibiting any symptoms.
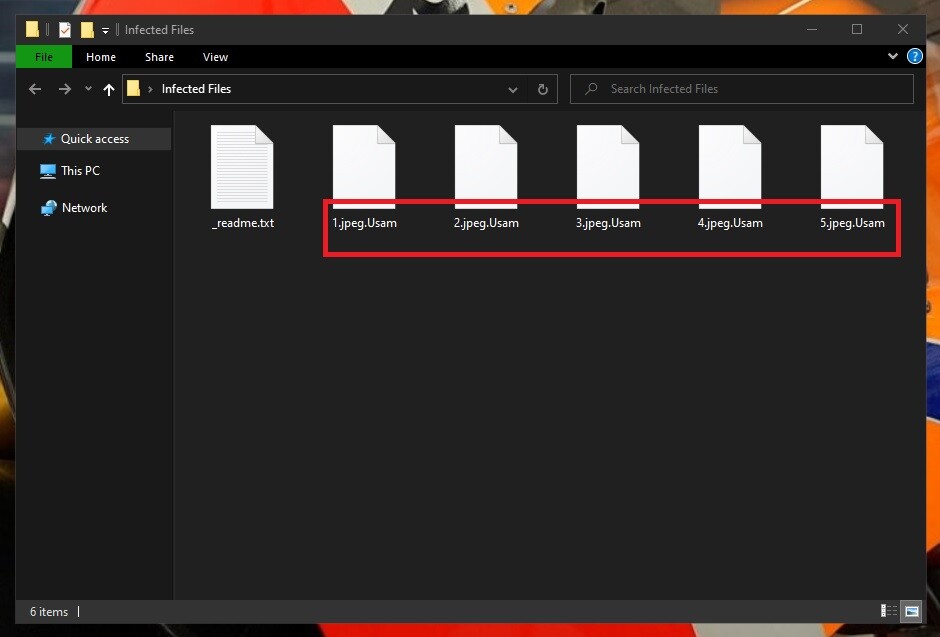
The Usam Virus encrypted data
This is one of the things that makes malware of this type so dangerous. And another is that it usually also won’t trigger a response from your antivirus system, making it all the more treacherous. Some ransomware variants are even capable of disabling your antivirus software altogether.
However, on some occasions it may in fact be possible to intercept a ransomware attack before it’s over. In this case a significant system slowdown is usually what would give the infection away. And if you happen to notice an unfamiliar process using up all of your computer’s CPU and RAM, shut your machine down immediately.
The Usam file distribution
The Usam file distribution can take place using a variety of different means, most commonly malvertisements and spam. And very commonly there’s also a Trojan (Auto Refresh Malware, Wup.exe) or other backdoor virus aiding the Usam file distribution.
So with that in mind, we would also recommend running a full system scan for additional malware after you have dealt with this variant.
SUMMARY:
| Name | Usam |
| Type | Ransomware |
| Detection Tool |
Remove Usam Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

my all files encrypt with .usam extension . unable to decrypt .
getting message
File: F:\personal documenys\HOME\PROPERTY TAX.pdf.usam
No key for New Variant online ID: Xp4EAgHrpqVIqbkFAIq7ylq47e8Y9A7lkv349R6O
Notice: this ID appears to be an online ID, decryption is impossible
with emsisoft
pl help
Hi Sk Mahi
you can go to this page How to decrypt ransomware and try the methods there.