.Npph
.Npph is a harmful PC virus that can infect computers with the Windows OS and lock up the user files located on them. The goal of .Npph is to keep the targeted files inaccessible until the computer’s owner issues a ransom payment.
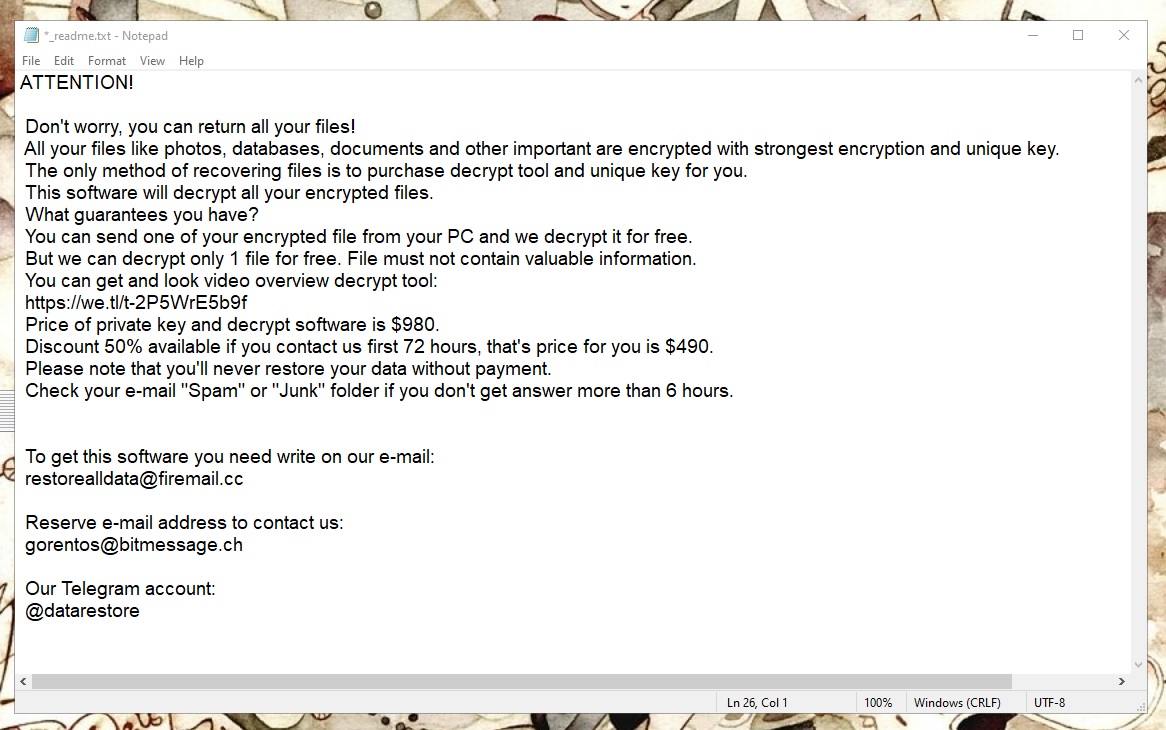
The .Npph virus ransom note
This type of online money extortion is very common nowadays and every day thousands of users fall victim to such viruses like .Ogdo, .Kasp, .Geno. This malware category as a whole is known as Ransomware due to the ransom demanded by the hackers at the final stage of the infection. After the virus attacks the computer of its potential victim and locks up the most important data saved on the machine, it places a ransom note somewhere on the computer. Normally, the note would be generated on the Desktop or within the folders where there are locked files. In either case, the end goal of the infection is the same – to get its victims to pay a set amount of money for the release of their most important files. According to the hackers responsible for the creation of this virus, only the correct payment of the ransom could release the inaccessible files that the virus has targeted.
The .Npph virus
The .Npph virus is a new malware variant of the Ransomware family that uses encryption to take the files of its victims hostage. The .Npph virus creates a unique decryption key during the encryption process and saves it on the servers of its creators.
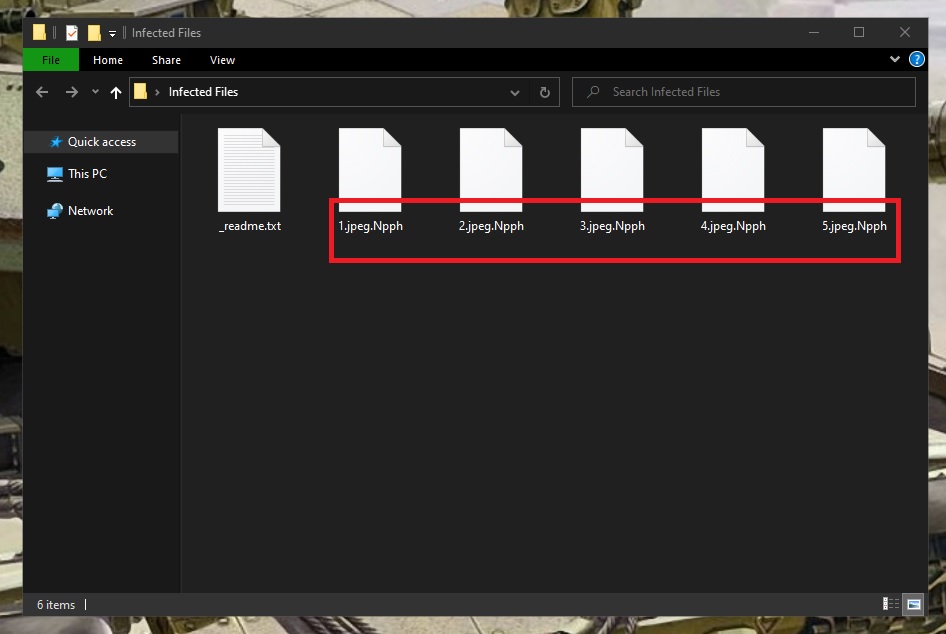
The .Npph virus encrypted files
Supposedly, the correct decryption key would be provided to the victim if the latter completes the payment. However, trusting the statements and promises made in the ransom note might not always be in your best interest. The problem with the ransom payment as a potential option, aside from the sheer size of the sum that needs to be paid, is that you don’t really know what would happen if you transfer the demanded money. Of course, you may indeed get the key and release your files with its help but the opposite scenario is also possible. For all you know, the criminals might send you the wrong key or no key at all, in which case you wouldn’t be able to do anything and your money would still be gone for good. Because of this risk that shouldn’t be ignored, our advice is to first try some of the other suggested solutions in such situations. There is no guarantee that another method would yield better results but at least you won’t be sending a big portion of your money to a group of anonymous online criminals.
The .Npph file encryption
The .Npph file encryption is the process that this virus uses in order to prevent you from accessing your personal data. The .Npph file decryption can be decrypted using its matching decryption key, however, this key is initially only available to the hackers.
As established above, paying for the key is risky business, so it’s much better to first opt for the free alternatives. Some potential recovery suggestions that do not involve paying the ransom will be shown to you in our guide, but you will first need to remove the Ransomware itself by following our removal steps in order to ensure that the files you potentially manage to restore don’t get encrypted all over again.
SUMMARY:
| Name | .Npph |
| Type | Ransomware |
| Detection Tool |
Remove .Npph Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment