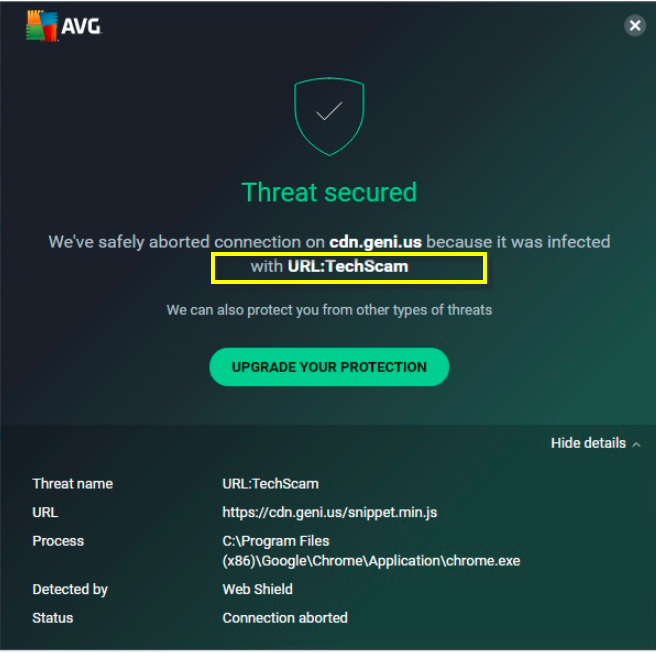
TechScam
TechScam is a Trojan Horse variant known for its ability to stay disguised in the attacked system by mimicking legitimate system processes. Threats like TechScam are primarily used as illegal tools for cryptocurrency-mining, user espionage, Ransomware distribution, and for coordinating DDoS attacks.
The Trojan Horse infections amount to an impressive percentage of the total malware infections, which could be encountered online. In general, three out of every four Internet contaminations are caused by a representative of this malware category. Therefore, chance of accidentally bumping into a nasty Trojan-based threat is quite high. In case that your computer has recently been infected with one of the newest representatives of this malware type, you really have a reason to be concerned about your PC’s safety. New Trojans are much more sophisticated and difficult to remove and their criminal creators arm them up with a whole set of malicious abilities. Speaking about new Trojan threats, on this page, we have focused on a recently reported malicious program which goes under the name of TechScam. A significant number of web users have already been compromised by this particular infection and that’s why, in the next lines, we have decided to help anyone of our readers who might be in a similar situation and offer them some effective and removal methods, which can help them get rid of the sneaky threat.
The dreaded reputation of TechScam comes from its ability to perform numerous criminal tasks and to spread online with the help of commonly encountered types of web content which the malware uses as disguise. The majority of the victims usually get contaminated after they have been tricked into clicking on a legitimate-looking email message or attachment, an interesting picture, a spam pop-up or a misleading ad. Many may also catch the infection by visiting a phishing site or by carelessly installing infected torrents and free software setups from non-reputed developers. The most important thing if you have already been compromised, however, is to detect and remove the danger on time. This is best done automatically, with the help of a reliable antimalware tool, or manually, with the help of a removal guide like the one below.
The reason we usually recommend the use of professional removal software, (especially to users, who have no malware-removal experience) is because the victims may not be able to detect all the hidden malicious data that the Trojan may manage to remain inside the system. Also, there is a certain risk of deleting vital system files by mistake because, oftentimes, the malware tries to mimic regular system files and processes in order to stay stealthed detection. And if not correctly identified, not only may TechScam keep on performing its criminal activities undisturbed, but may even insert other nasty viruses such as Rootkits or Ransomware without the users’ knowledge. Basically, the scale of the damage such a sophisticated threat could cause depends on what the hackers are after. They may use the Trojan for criminal tasks like theft of passwords and of sensitive personal information, espionage, system corruption, data destruction, distribution of other malware and much more. That’s why the successful elimination of such a great cyber threat from your computer really requires all your attention. It is highly advisable that you use trusted anti-malware software to scan your entire system and carefully follow the suggested removal steps for optimal results.
SUMMARY:
| Name | TechScam |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Usually, the infection tries to hide deep in the system, without triggering any visible symptoms. |
| Distribution Method | Typically found inside spam messages, malicious emails and attachments, infected links, torrents, pirated content. |
| Detection Tool |
Remove TechScam Virus
If you are looking for a way to remove TechScam you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for TechScam and any other unfamiliar programs.
- Uninstall TechScam as well as other suspicious programs.
Note that this might not get rid of TechScam completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment