*Source of claim SH can remove it.
We created the information below to guide you in removing the TellYouThePass Ransomware and instruct you on how to avoid repeat infections. Removing it is only half the battle. The other part is closing down the CVE-2024-4577 vulnerability and ensuring there’s nothing on the infected PC that can restore the TellYouThePass Ransomware.
What type of threat is the TellYouThePass Ransomware?
TellYouThePass is a “commodity-level” ransomware that first emerged in 2019. This has been stated several times in news outlets, but it’s very little consolation to actual victims of the malware. In plain terms: TellYouThePass ransomware isn’t very sophisticated, but when it has completed encrypting your files, there is no difference between it and other ransomware. You have a very low-chance to recover your files if you don’t have backups.
Recently (June 2024) TellYouThePass Ransomware gained renewed attention for exploiting recently found vulnerabilities like Apache’s Log4j. But, unlike other cybercriminal groups, TellYouThePass doesn’t maintain a public blog or repository of victim data, which adds a layer of unpredictability to its operations. It targets both businesses and private individuals, with an unscrupulously broad scope in terms of potential victims.
In the past we observed TellYouThePass Rnsomware exploiting CVE-2021-44228, but much more recently it targeted the newly found CVE-2024-4577 vulnerability. The ransomware gang is currently exploiting the newly patched exploitable remote code execution very heavily in in PHP. This allows attackers to deliver webshells and execute their encryptor payloads on target systems.
The attacks you are likely here for began on June 8, just 48 hours after PHP’s maintainers released security updates. The attackers used publicly available (on Github) exploit code. This involved executing arbitrary PHP code using the Windows mshta.exe binary to run a malicious HTML application. The group shows a clear preference for exploiting known vulnerabilities in open-source web development languages. This unfortunately means TellYouThePass Ransomware is not limited to Windows, but can also infect Linux users.
How TellYouThePass exploits CVE-2024-4577
This information is best suited to tech-savvy individuals:
Several PHP versions before 8.3.8 have a significant vulnerability when used with Apache and PHP-CGI. If certain code pages are set, Windows might use a”Best-Fit” behavior, replacing characters in the command line given to Win32 API functions. Such behavior causes the CGI to mistake those characters as PHP options, which in turn allows a criminal to pass options to the PHP binary. We are placing this here as a simple explanation in case you want the context of what’s going on.
If we lost you here, we recommend contacting a sys admin or just use SpyHunter as recommended in our ads.
TellYouThePass uses the Windows mshta.exe binary to run an HTA file, which is a container for a VBScript with a base64-encoded string. The string decodes into a binary, loads a .NET variant of the ransomware into the host’s memory, and at that point you are already infected with TellYouThePass Ransomware. The malware the sends an HTTP request to a command-and-control (C2) server in the form of a fake CSS resource request. From then on it operates like a standard ransomware – it encrypts the files on the infected machine.
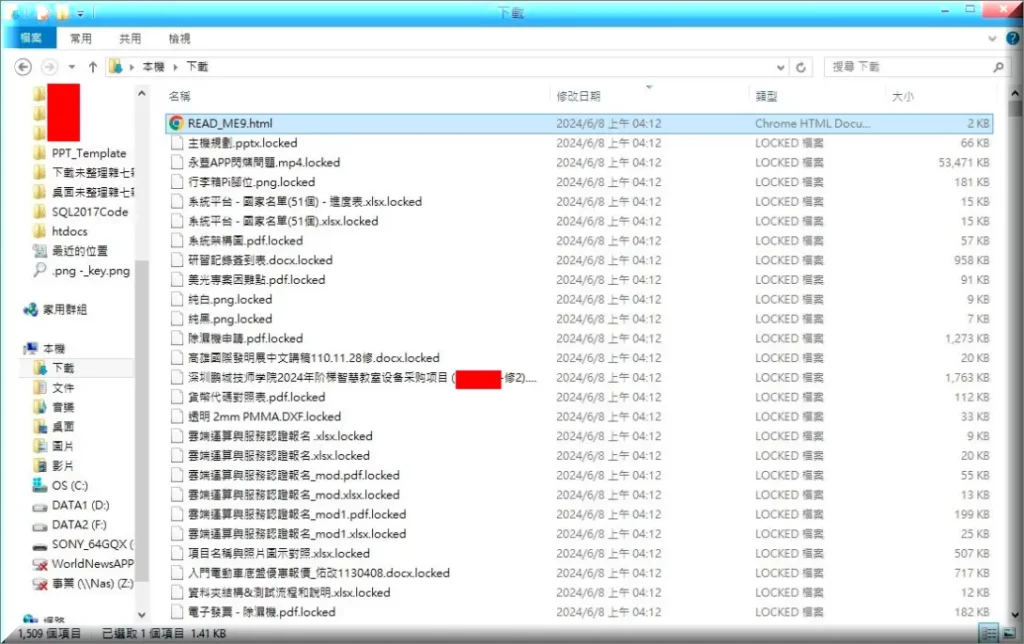
After it’s done with the encryption, TellYouThePass Ransomware places a ransom note titled “READ_ME10.html” with instructions on how to restore the files. Most victims unfortunately notice the infection only at that point, which is too late to do anything about it. The current ransom demand is set at 0.1 BTC (about $6,700). Several online websites are currently infected with and can act as vectors if this persists.
How to avoid repeat infections by TellYouThePass Ransomware
There are ways you can mitigate the exploit of the PHP flaw and prevent further attacks by TellYouThePass Ransomware (or another malware that follows suit). First, you can patch the affected systems – which sounds like a no-brainer. But it is an essential step. Many websites don’t update regularly in fear of breaking functionalities in the back or front-end, but this will ensure the virus doesn’t return.
Second don’t run PHP with CGI mode enabled. As you can see with Log4j, it’s challenging to update every system impacted by a flaw in a web scripting language. You can migrate to a more secure architectures like Mod-PHP, FastCGI, or PHP-FPM. In general PHP CGI is outdated and problematic.
You can also follow other best practices, but those are more general and not directly related to TellYouThePass Ransomware. Regularly take stock of all assets and applications in your work environment. You can patch any vulnerabilities affecting them. Use Web firewall technology to stop attacks an since you are here, we recommend buyin an anti-malware program as a first line of defense.
What can you do to mitigate the damage done by TellYouThePass Ransomware?
It’s very crucial to act immediately and shut down the infected device if you catch TellYouThePass Ransomware early on. Isolate the infected system immediately from other devices on the network or the ransomware can spread across them This helps contain the infection and stops further encryption of files.
Next, identify the strain of ransomware you’re dealing with. Knowing it’s TellYouThePass this means the files will be appended with a .LOCKED extension. You can find specific decryption tools or resources here but they likely won’t help you. Unfortunately, there’s no guaranteed method to decrypt files without paying the ransom, but reaching out to cybersecurity firms can provide options.
Backup restoration is your best bet to restore the files, but this is only viable if you have backups in the first place. If you DO have them, make sure they are stored offline or TellYouThePass Ransomwaare can spread to them. Make sure to clean your systems thoroughly before restoring your system to a pre-attack state to avoid re-infection.
SUMMARY:
| Name | TellYouThePass |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
*Source of claim SH can remove it.
Remove TellYouThePass Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt TellYouThePass files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment