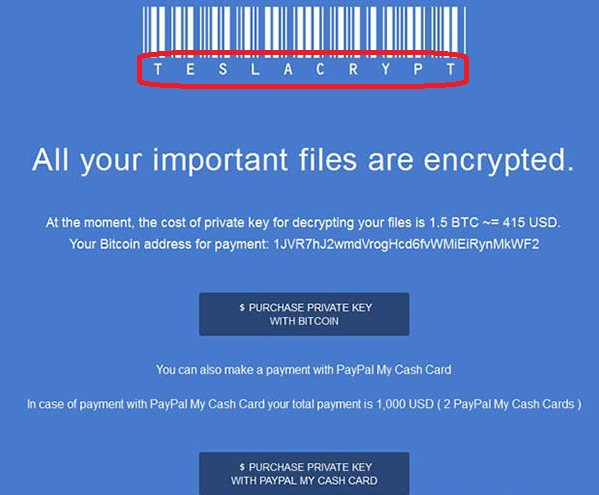
TeslaCrypt
If all of your files have recently acquired a strange extension and are unusable, then it is likely that you have been targeted with a ransomware virus. Judging from the file extension used this virus is probably TeslaCrypt Virus. It is a relatively new addition to the ransomware scene and it’s still viral, thus we decided to make a guide on how to handle it.
TeslaCrypt 4.0
The biggest reason why ransomware viruses like TeslaCrypt 4.0 are such a huge threat is the fact that files encrypted by them won’t return to their original state even if the virus is removed. The only way to decrypt these files is to obtain the necessary code, which is exactly what the hackers want to sell you. Fortunately, some alternative methods do exist, but they are far from perfect.
We’ll do everything possible to save your files without having to pay the ransom, so stay tight.
It is far easier to prevent your PC from becoming infected in the first place than it is to handle this virus. Please keep that in mind, because ransomware has been growing in popularity and it is not unlikely to encounter any of its brothers in the future. A computer infected by the TeslaCrypt 4.0 Virus (or similar ransomware) can be saved if quick action is taken.
While the ransomware will try to remain invisible once it gets inside your computer, it will take some time for it to encrypt your files. You can notice its presence if your PC is behaving much worse than usual and ordinary programs take a long time to load or function properly. The encryption process used by TeslaCrypt 4.0 is fairly CPU/RAM hungry, so if you open your Task Manager you may be able to spot the process. It will usually come from an “Unknown” manufacturer or have a blank space and it will consume a lot of memory and CPU power. If you spot anything like this it is advisable to immediately shut down the computer (pull the plug if necessary) and seek professional help.
Paying the ransom – is it worth it?
It is a sad fact that many people prefer to pay the ransom and this is precisely the reason why there are so many ransomware viruses in circulation – apparently extortion is a lucrative business. Unfortunately the stories of many people who tried to pay, but got burnt are untold. The reality is that you are extorted by cyber criminals to pay the money in BitCoins – an untraceable online currency. You get no guarantee that you will get your information back, but you can be assured that this money will be put into excellent use in the creation of a new ransomware agent. Our advice is to try and salvage as much of your encrypted files as possible and forget about payment altogether.
Distribution of TeslaCrypt 4.0
Believe it or not, Trojan horse viruses have become the primary way in which ransomware viruses reach our computers. Once a Trojan horse gets installed into your system it can communicate with a remote server and install the ransomware (and possible future versions of the same) on your PC. Since you already have a ransomware infection it is highly likely that you have a Trojan on boards as well. Unfortunately these things are pretty good at the hide-and-seek game, the only sure way to find it remains the use of security software. If you already have such a program have it do a scan on your PC, if you don’t or if it fails to produce any convincing results you can try the software we’ve found to be best in the field. Click on one of the banners in our page.
SUMMARY:
| Name | TeslaCrypt 4.0 |
| Type | Ransomware |
| Detection Tool |
Remove TeslaCrypt 4.0
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment