How does the .Todar Virus work?
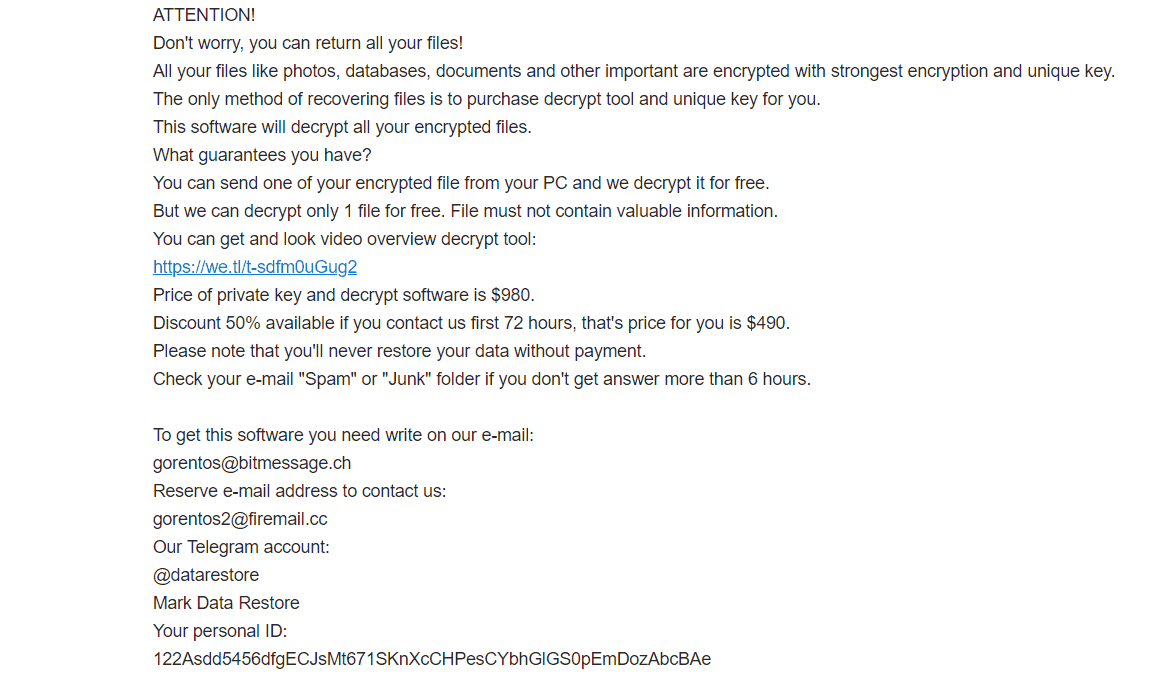
The .Todar Virus will show you this message, which contains instructions for paying the ransom.
Ransomware (ransom + malware) is a category of computer infections that affect both mobile devices and Mac/PC machines. The representatives of this malware category like Lapoi, Darus, Tocue, can be extremely harmful if the attacked user keeps important data in their device. The Ransomware infections use different ways to block access to the entire device or all the files stored on it and then ask for a ransom to be paid for the computer’s or the data’s liberation. In this post, we will explain some of the most important characteristics of these nasty computer threats and will tell you how to deal with them. What is more, we will stop our attention at one new Ransomware-based infection which goes under the name of Todar. The main objective of this infection is to encrypt all the important files and documents that the victim keeps on their machine, and then to ask for a ransom payment (usually in the form of bitcoins or some other cryptocurrency) in order to provide a decryption key for the liberation of the encrypted information.
If you have fallen victim to the secret file encryption of Todar, you have most probably been greeted by a scary message, which prompts you to follow certain payment instructions. The message probably has given you a set of steps to complete in order to fulfil the payment as well as a deadline, which you must keep. However, since you are reading this, you most probably have decided to seek some alternative ways to deal with the infection and its ransom demands. That’s why below we have prepared a specially created guide which will show you how to detect and remove Todar and how to potentially save some of your flies for free.
How do this .Todar File spread?
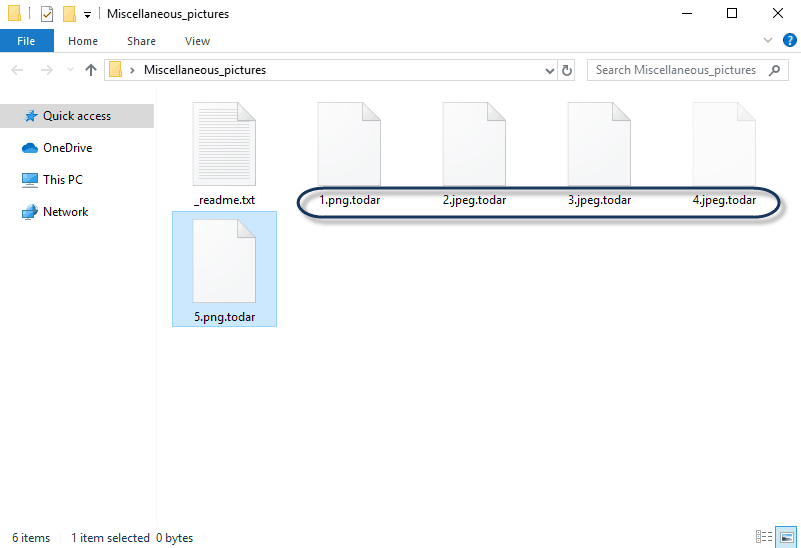
.Todar Virus Ransomware is from the STOP/ DJVU family, it will encrypt your files with .Todar extension.
Typically, a Ransomware cryptovirus isn’t a form of malware that anyone can create. This is a type of malware that requires high programming knowledge. However, unfortunately, thanks to its growing popularity, malware developers have created specialized toolkits that make it possible for even people with little to no programming experience to create their own customized Ransomware viruses .
Ransomware is transmitted through several means: links on pages of dubious reputation, programs that in general seem legit as Windows or Adobe applications, or via email attachments. Different social engineering techniques are used to make the victim click on the carrier of the infection as this is required for the contamination to take place. Once the users interact with it, the harmful program silently nests itself inside the OS and begins the encryption of the files stored there.
The next step, after all the data has been locked, is usually to inform the victim about the demanded money payment. Here, each hacker uses their own method, but usually, the attacked user finds out about the infection through a scary message on the screen which also serves to provide specific ransom-payment instructions,.
Unfortunately, if you pay the ransom, there is no guarantee that the cybercriminal will give you the key to decrypt the “hijacked” files. Therefore, it is a good idea to explore other recovery solutions, which do not involve paying a ransom and are focused on removing the infection from the system. That’s why we suggest you take a look at the Todar removal guide below and make use of its instructions.
SUMMARY:
| Name | Todar |
| Type | Ransomware |
| Detection Tool |
Todar Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
those were the IPs. I got this virus but after i ran my anti virus and deleted all infected files, my pc went well. But still got the .todar files. Most of the affected files are my downloaded programs but not on the installed ones. Is it oky if i remove the .todar in my file names to restore the files?
You should remove the IPs from the Hosts file. You can also try to change the extension but it will probably not restore the locked files. For file-recovery suggestions, try the instructions in our How to Decrypt Ransomware article.
dear sir
i am using that software but not recover my data
Update to STOPDecrypter v2.1.0.20 with more OFFLINE keys.
OFFLINE ID: ZivCxija0GBwtwtwD0q4JRy80spT6lUyybPYhot1
Extensions: .lapoi
OFFLINE ID: Q2fNGjIEoR7J8UnURFiIH13JGa23UqaNUDz4ret1
Extensions: .todar
i check my files in ID Ransomware – Identify What Ransomware Encrypted Your Files
result
This ransomware may be decryptable under certain circumstances.
Please refer to the appropriate guide for more information.
Identified by
ransomnote_email: gorentos2 @firemail .cc
sample_extension: .todar
sample_bytes: [0xC8B5 – 0xC8CF] 0x7B33364136393842392D443637432D344530372D424538322D3045433542313442344446357D
Click here for more information about STOP (Djvu)
please help me please
please
my data is not Decrypter
i chang my pc with new pc my data was not decrypt
please help me