Tool Extension
If your computer has been infected by a program called Tool Extension, you have landed yourself what is popularly referred to as a browser hijacker. Tool Extension integrates with widely used web browsers such as Firefox, Chrome and Edge and spams them with online ads.
The ads can come in every shape and size ranging from screen-wide banners and blinking box messages to annoying popups that come out of nowhere and beyond. And don’t rely on your ad blocker or other such tool to stop them. Thanks to Tool Extension, these ads are generated from within your own system, hence no popup blocker will be able to prevent them from showing up on your screen.
This is also valid for the sudden page redirects that you may have started experiencing ever since Tool Extension appeared on your computer. These can take place at any point during your browsing sessions and will force you to land on a variety of different sponsored web locations. Typically, these will be sites that are trying to promote and/or sell some type of product or service. And as for the page redirects themselves, they may take place within the same tab, or they may open new ones, and sometimes they may even open new browser windows.
The Tool Extension Virus
Aside from the advertising materials that software like the Tool Extension virus can generate in your browser, these type of applications are also known for their ability to meddle with the browser’s settings. This is actually how hijackers such as the Tool extension virus get their name. And most vividly this is seen in the changes they tend to make to the browser’s homepage as well as to the default search engine.
But what has a tendency to shock users is when they try and revert these setting and reconfigure their browser so that it has the old settings again. As soon as they restart their browsing program, the hijacker will have reinstated its own configurations and that will be that. Thus, unless you thoroughly remove Tool Extension or Editor Extension without leaving any residual components, you won’t be able to restore your browser to its pre-hijacker state.
That is why we have designed the below removal guide. With its help, you will be able to completely uninstall this browser hijacker and resume an ad-free browsing experience without the annoying page redirects and other effects. And if you would rather have the removal process handled automatically, we also have a professional removal tool available for you on this page.
Keep in mind that removing Tool Extension isn’t just doing yourself a favor in terms of the irritation and frustration you will be saving yourself. It’s actually beneficial to the overall safety of your system because there’s a certain risk associated with these types of programs. Namely, as a result of their endless ads and redirects, there’s a danger of landing on compromised web locations that could potentially be harboring viruses and different malicious code. So if you’d rather avoid the risk of getting infected by some ransomware or Trojan horse virus, removing Tool Extension is certainly the way to go.
SUMMARY:
| Name | Tool Extension |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Remove Tool Chrome Extension Virus
Uninstalling Tool Extension may be difficult if you’re not familiar with browser hijackers, but following these easy steps should make it much easier:
- To regain control of your browser once it has been hijacked, open it and select the main menu icon.
- Second, choose More Tools (or Add-ons).
- The next step is to find and open the Extensions tab.
- The browser’s extension list will display all currently installed extensions. If you want to get rid of the Tool Extension extension, select Remove/Trash Bin.
- If there are additional extensions that are interfering with your browser experience, it may be a good idea to remove them too, as this will not harm your OS in any way.
- To see how the browser performs after the removal of the unwanted extensions, try opening a new tab and surfing for a while.
You may need to use the detailed methods below to search for and remove any additional potentially unwanted components that may have been installed on your system, in case that annoying pop-ups and Tool Extension-related notifications continue to appear in your browser after deleting any extensions you suspect are hijacker-related.

A restart of the system in Safe Mode will be needed in order to begin the Tool Extension removal process. before you do that, however, please bookmark this guide in your browser, so you can easily reload the page after the system reboots.
Next, click on this link and follow the steps there to enter Safe Mode in Windows. Once you do that, get back to this page and move to step 2.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
This step involves searching your PC for and ending any Tool Extension-related background processes.
To do that, open the Task Manager by pressing CTRL+SHIFT+ESC and then selecting the Processes tab (the “Details” Tab for Windows 8 and 10). Look at the list of running processes and right-click on any process that you think is hijacker-related, then click on Open File Location to see its files:

After that, you may check the files of that process for hijacker-related code using the sophisticated online virus scanner provided below.

Stopping the process and then deleting any hijacker-related files is the next thing that you need to do if the scanner detects a danger during the scan. To end a suspicious process, right-click on it in the Processes tab and select End Process.

Next, use the Windows key and R key combination to open a Run box on the screen. In it, type appwiz.cpl, then click OK.
This will directly lead you to a Control Panel window where you can see all the programs that are currently installed on your system.

Search for and remove Tool Extension from your list of installed apps by selecting it and clicking the Uninstall button at the top. Do the same for any other outdated or potentially unwanted software that you are not using. Keeping your computer clean of such software will reduce the risk of potential vulnerabilities.
Next, type msconfig in the Windows search field and open the System Configuration app. To see if Tool Extension has been added to the Startup tab, click on it and take a look at the list of startup items. If you spot something unusual, make sure you research it online and then remove its checkmark if there is enough information that proves it is related to the hijacker. Save your changes by clicking on the OK button.


In this step, you need to open the Hosts file on your computer to look for any unexpected alterations or indicators of hacking, such as new IP addresses. You can do that by pressing Windows key and R together and then pasting the following line in the Run box:
notepad %windir%/system32/Drivers/etc/hosts
Then click OK and locate Localhost in the Hosts file. It normally should be at the bottom of the file. Check to see if any unfamiliar IP addresses have been added to Localhost without your permission.

If you see anything strange, please let us know in the comments below, so we can check it out.
After that, close the Hosts file and open the Network Connections by searching for it in the Windows search field. Then, proceed with the following instructions.
- Right-click on the network adapter currently in use and select Properties.
- In the new window, look for Internet Protocol Version 4 (ICP/IP), select it and then click the Properties button bottom right.
- Once you’ve set the DNS to Obtain DNS Server Address Automatically, click on Advanced.
- Remove any rogue DNS entries from the Advanced DNS tab by selecting it and then clicking Remove. To make the modifications take effect, click OK.


Tool Extension may have made changes to your browsers without your awareness, and here’s how to undo them. The Tool Extension invasion can only be stopped if these actions are taken on all browsers installed on your computer, regardless of how frequently you use them.
The shortcut icon for your web browser should be right-clicked. Next, select Properties from the pop-up menu.
For Firefox and Internet Explorer, (or Edge), the steps are identical to those shown in the example images of Chrome.

Go to the top menu with many tabs in the Properties window and select Shortcut from the tabs. Keep an eye on the Target area and delete anything after .exe. Then click “OK”.

![]() Remove Tool Extension from Internet Explorer:
Remove Tool Extension from Internet Explorer:
To reach the Manage Add-ons option, open Internet Explorer and click the gear icon in the upper-right corner of the browser’s window.
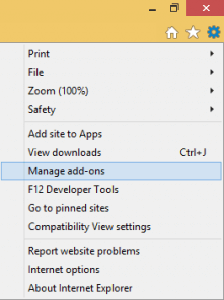
If you find the browser hijacker, uninstall it from the Add-ons list.
Select Internet Options from the menu that appears after clicking the gear icon a second time. Change the home page’s URL if you don’t like the one that you see there. Once you’ve entered the URL you want to use as your default home page, click “Apply”.
![]() Remove Tool Extension from Firefox:
Remove Tool Extension from Firefox:
When you’ve launched the Firefox browser, go to the Firefox menu button in the upper-right corner of the screen and select “Add-ons”. Next, open Extensions from the Add-ons menu on the left side of the screen.
Check to see whether your browser returns to normal after you remove any extensions that you believe are interfering with its functioning.

![]() Remove Tool Extension from Chrome:
Remove Tool Extension from Chrome:
Google Chrome should be closed in order to go to this location of your system:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
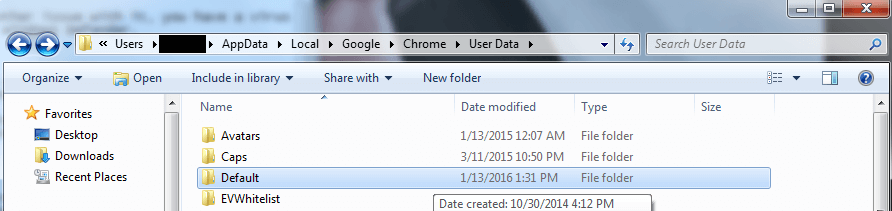
The “Default” folder under User data should be renamed to “Backup Default“. After that, restart Chrome and check if the hijacker has been eliminated from the browser.

Browser hijackers have been known for their ability to alter the registry in order to extend their presence in the system. You will learn how to remove system registry entries that are associated with hijackers in the sixth step of this guide.
Start with typing Regedit in the Windows Search field and press Enter. After you do that, a window for the Registry Editor will pop up on your screen. By clicking CTRL+F and putting Tool Extension in the Find dialog box, you may search for files that are matching the hijacker’s name. Search the registry for any similar entries and remove them.
If your search doesn’t turn up anything, the following three locations can be manually searched in the Registry Editor’s left panel:
- HKEY_CURRENT_USER—-Software—–Random Directory.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
Look for folders and subfolders with strange-sounding names in each of the directories listed above. You must use extreme caution while removing any files or directories associated with Tool Extension.
Attention! When in doubt about which registry files and folders are linked to the browser hijacker, better leave them there and don’t make any changes, as deleting a legitimate entry may corrupt your OS. To avoid this, on this page, we’ve included a link to a powerful malware-removal tool that can detect and remove the Tool Extension-related files for you, or you may use our free online virus scanner to check specific suspicious-looking files for malware.

Leave a Comment