Top News Feeds
If Top News Feeds has been installed on your computer, then you’ve got yourself a browser hijacker. Browser hijackers like Top News Feeds are generally harmless ad-generating pieces of software.
The Top News Feeds.net virus
However, there are certain hidden elements to their activities that we believe users ought to be aware of. So, if Top News Feeds is what brought you to this page, we recommend you stick around to the end of this post to find out what it’s all about.
The Topnewsfeeds.net Virus
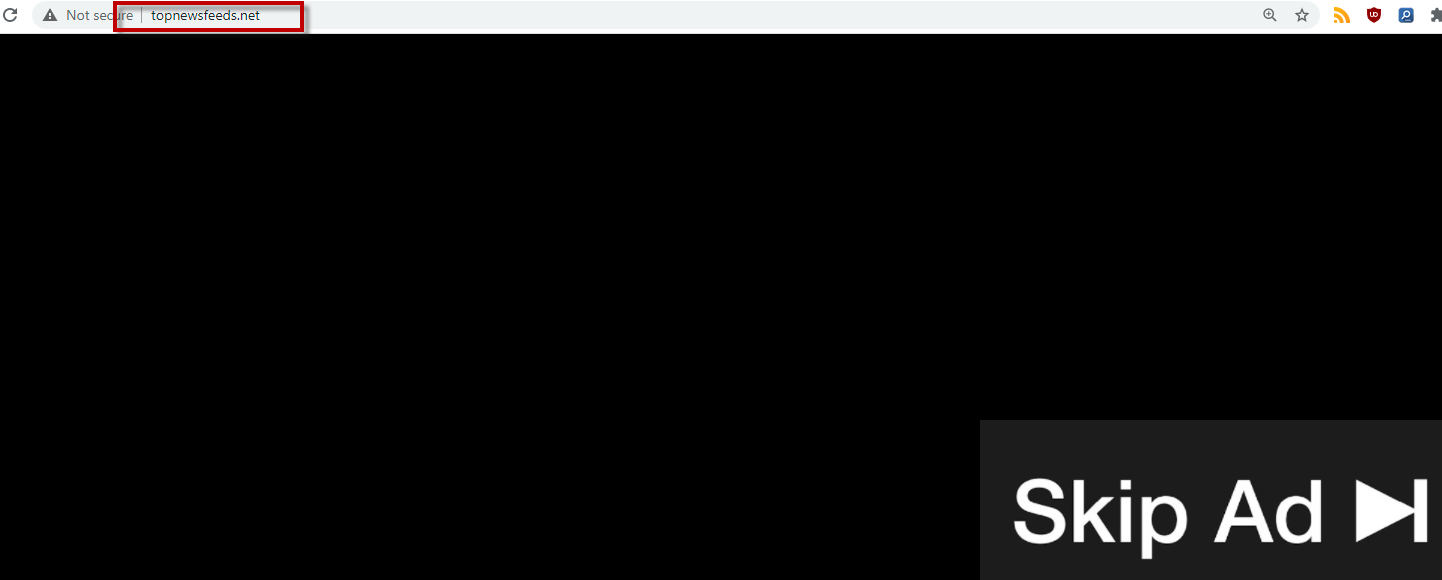
One of the leading giveaway traits of the Topnewsfeeds.net virus browser hijacker infection is the substituted homepage and/or default search engine in your browser. Speaking of which, a program like the Topnewsfeeds.net virus can integrate with pretty much any browser (Chrome, Firefox, Edge, Safari, etc.).
In addition, the hijacker installs ad-generating components that can launch streams of endless ads on the screen of your computer. Popups, banners, in-text links, box messages – anything you can think of. And one of the most annoying things is that no thanks to this browser hijacker, you can constantly be redirected to various sponsored websites that you have no interest in seeing at all.
How can you prevent the installation of Top News Feeds?
To answer the above question we first need to answer another one. Namely, how does a program like Top News Feeds end up in your system to begin with?
Well, there are several possibilities, including following a link from a spam email or if you were already infected with another program of this type beforehand. However, the most common and most likely way you could have landed Top News Feeds or Poshukach is from within a program bundle. These are software packages that are a distributed together and are typically available on torrent sites, open source download platforms or pages that specialize in distributing freeware and shareware. The trick is, though, that there is one main install – the program that you’ve likely sought out willingly. And “bundled” in its installer are one or more other components, such as browser hijackers or adware.
If you recall recently downloading some program that more or less fits that description, then you’ve found your culprit. Chances are you ran the automatic or default setup and that’s how you also installed whatever added content was in the installer. However, if you were to click on the Custom/Advanced settings, you would have been able to avoid this. You would have had the opportunity to customize the setup and will have been given the chance to opt out of those added installs. In other words, this is what you should stick to from now on when configuring new software on your PC.
Is Top News Feeds a virus?
Luckily, Top News Feeds is not a virus and you don’t need to be concerned that it will damage your system. But its constant page redirects have the capacity of exposing you to malicious threats such as ransomware, Trojans, etc. Therefore, it’s a good idea to keep far away from all the promotional content you’re bombarded with. And the easiest way to protect your computer from this point on is to simply remove the pesky Top News Feeds right away. Please refer to the instructions in the removal guide below to see how to do that.
SUMMARY:
| Name | Top News Feeds |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Popups, banners, box messages, in-text links and various other online ads flooding your screen like never before. |
| Distribution Method | Spam messages, other browser hijackers, certain web ads and program bundles. |
| Detection Tool |
Remove Top News Feeds Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.

![]()
- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Top News Feeds from Internet Explorer:
Remove Top News Feeds from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
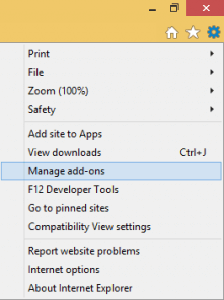
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Top News Feeds from Firefox:
Remove Top News Feeds from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Top News Feeds.net from Chrome:
Remove Top News Feeds.net from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
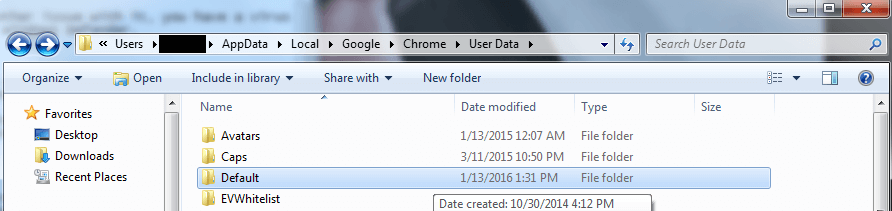
Rename it to Backup Default. Restart Chrome.
![]()
Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment