Topi
Topi is a ransomware-based malware that relies on a blackmail scheme to extort money from its victims. Topi can make any digital information unavailable to the user by encrypting it with a complex algorithm and then demanding ransom in exchange for decrypting it.
To date, Ransomware infections are the most harmful cyber threats that you can encounter. Topi falls precisely into this category of cyber threats because it specializes in file encryption and money extortion. To perform its agenda, the virus needs to enter your system first. And, this often happens with the help of a Trojan horse virus. The two versions of malware are often included in spam emails and their attachments and when you open one, the Trojan detects a vulnerability in your PC which then is exploited by Topi. The infection with Ransomware can also occur when you click on a fake ad, or you get redirected to a compromised website that contains the virus.
The Topi virus
The Topi virus is a harmful piece of software that serves the criminal intentions of a group of anonymous hackers. What the Topi virus does is it secretly invades a targeted computer, encrypts the files found on it and then demands ransom in order to decrypt them.
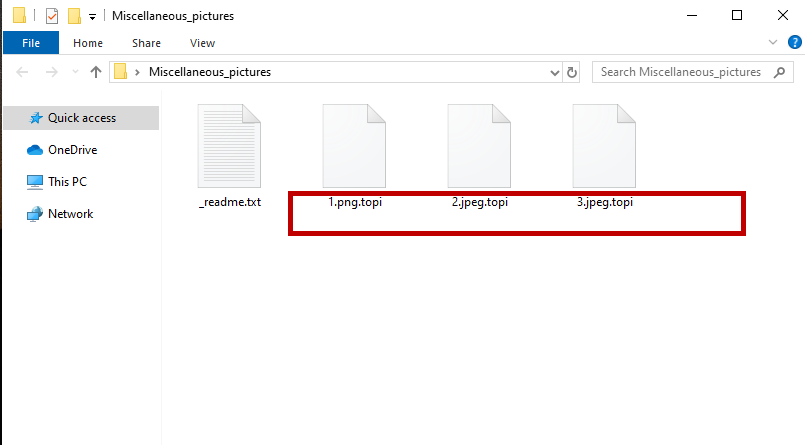
Scanning the entire disk for valuable files is what Topi usually does the moment it gets into the system. It checks which files the victims use the most and then compiles a list of all these files for encryption. The malware applies very complicated encryption that makes all the listed files inaccessible. Normally, at the end of the process, you get a ransom-demanding alert on your screen that provides you with instructions on how to regain access to your files by paying ransom. A decryption key is usually promised in exchange for your ransom payment.
The Topi file recovery
The Topi file recovery is a complicated process that requires a special file decryption key. If you don’t have a file decryption key, the Topi file recovery may also be possible if you use your personal file backup sources or system backup copies.
Unfortunately, most of the time the ransom payment is not a solution to the Ransomware problem. For one, there is always a risk that after you transfer your money, the hackers behind Topi may just disappear and leave your files forever encrypted. Therefore, if we were you, we would rather explore other possibilities that can help us to remove the infection and restore important files instead of rushing with a ransom payment. Some of these alternatives include consulting a specialist. Another way to handle such malware is to try to remove it with the help of a comprehensive removal guide such as the one that you will find below.
Once you clean the computer, you can safely connect your external drive or your cloud storage from where you can recover copies of your files. Another thing that can be done is to buy special Ransomware-removing software that can handle the infection. Prevention is always the most effective solution when it comes to all types of cyber threats. Some more special tips about keeping Ransomware away involve simply avoiding the possible sources of the virus as well as keeping important files backed up.
SUMMARY:
Remove Topi Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply