Touch Here Site
Touch Here Site is a browser hijacker that can redirect your web searches to unfamiliar webpages and spam the screen of your browser with pay-per-click ads, banners, and pop-ups. Touch Here Site can also replace the homepage, the main search engine or the new tab page with its own custom ones.
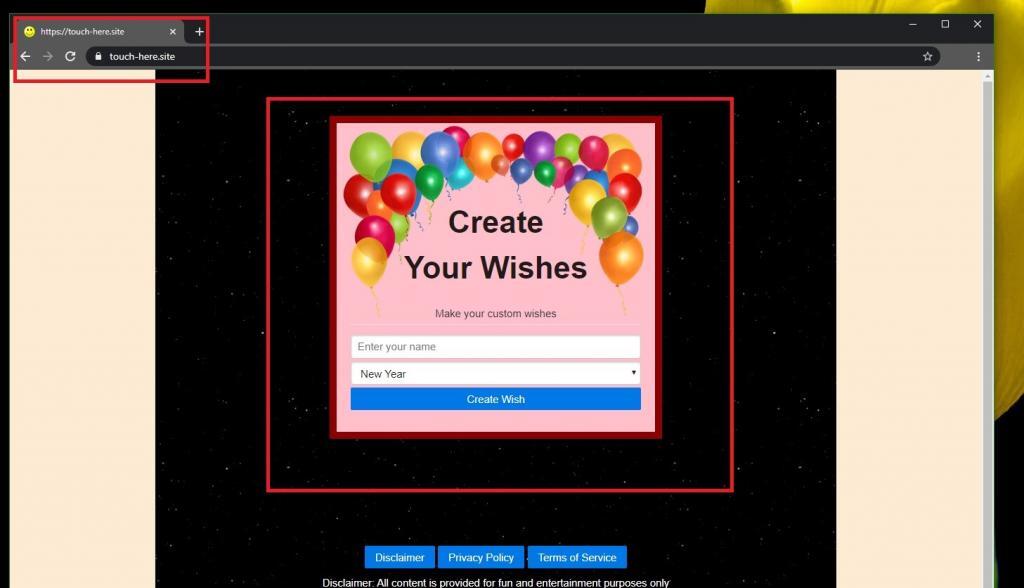
If your Chrome, Firefox, Edge, or Safari browser has started to behave strangely and you have found some unusual changes in its settings, such as a new toolbar or perhaps a new homepage, then this is an indication that it has been hijacked by a browser hijacker such as Touch Here Site. Such software is not as dangerous as, say a Ransomware or a Trojan Horse virus, but it tends to be quite irritating because it typically redirects users to various partnering websites and pages full of pop-up ads and banners that they had no intention of visiting.
What adds to the irritation is the fact that, when the users try to remove the imposed modifications and change their homepage and search engine back to the one they had before, they realize they can’t uninstall the newly set components. The moment they restart their browsing app, they get once again faced with unwelcome browser changes.
Luckily, since you are on this page, you’re not going to have to get used to these changes. Below, there is a thorough removal guide to help you effectively uninstall Touch Here Site and remove all of its unwanted components from any of the web browsers that might have been affected. Before you scroll to the instructions, though, we encourage you to familiarize yourself with what a browser hijacker really is and what it can do.
The Touch-here.site Malware
Touch here site is a piece of software designed to generate numbers amounts of online ads on the screens of web users and to redirect user searches to specific sponsored websites. Touch here site main goal is to promote and gain more visibility for different products and services and, in turn, to generate revenue for the developers of the program.
Each redirect and ad that a browser hijacker displays and gets clicked upon generates income. This is how this software makes money for its owners. So, naturally, there’s plenty of motivation for the people behind programs like Touch Here Site to show tons of pop-ups, banners, box messages, and various other online ads to increase the chances of you you clicking on them.
However, daily exposure to random commercials may not only be irritating but may also hide security risks. We specifically need to point out the possibility of clicking on misleading adverts or landing on low-quality web pages which could have been compromised by real viruses and malware, including Trojans, Spyware, and Ransomware. Besides, the presence of ad-generating programs such as Touch Here Site in the system may potentially lead to system performance issues such as sluggishness, browser unresponsiveness, and sudden crashes which can certainly be unpleasant. Therefore, we generally advise our readers to remove browser hijackers and uninstall their components in order to regain full control over their browsers and surf the web in peace.
SUMMARY:
| Name | Touch Here Site |
| Type | Browser Hijacker |
Touch Here Site Removal from Android
We are sending you to another page with a removal guide that is regularly updated to counter the latest tricks malware creators use. It will show you how to:
1. Locate and clean up your phone’s apps if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Reply