Trojan.Gen.Npe
Trojan.Gen.Npe is a Trojan horse virus and should not be underestimated. It is extremely harmful and no one can say for sure what its purpose really is. All Trojan-based software is considered malicious.
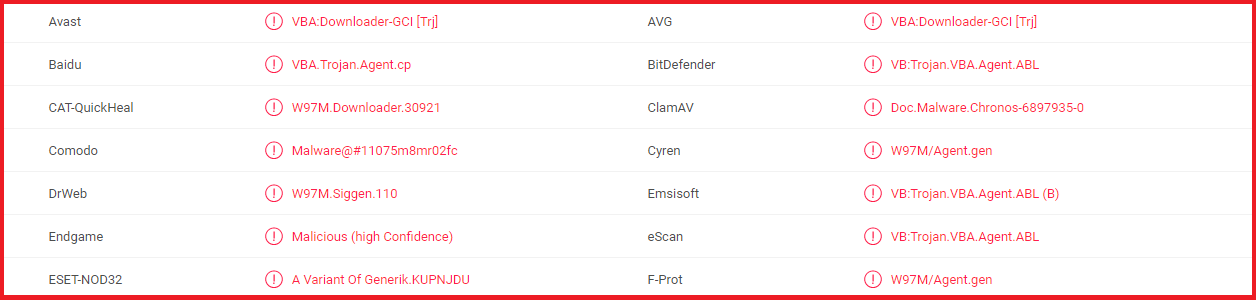
Multiple virus scanners from VirusTotal detect Trojan.Gen.Npe.
About Trojans in general
All Trojan-based software is considered malicious. The viruses in this group can exploit various distribution methods. They could also have very different usages and purposes. What is common among them all is that their activities are mostly subtle and stealthy – in most of the cases the user has no idea their computer has been contaminated. In fact, this is what the original Trojan horse from the famous tale did – stealthily infiltrated Troy and the naïve Trojans had no idea it was full of warriors and the worst was about to begin. The name of this malware family derives from this very myth exactly because of the way these viruses function.
Distribution methods of this malware
You should know that all the possible means of spreading Trojan.Gen.Npe and other forms of Trojans cannot be listed in only one article – they are too numerous and too varying. Nevertheless, we are going to mention the ones that have resulted in the most infections:
- Spam letters and their corresponding attachments in your email. Trojans often come as components of spam messages or as incorporated into their suspicious email attachments. In this case, unfortunately, these viruses are often not alone. They commonly travel with their closest malicious buddies – Ransomware-based programs. This basically means that your PC could get contaminated with two distinctive types of harmful software, which is pretty disturbing.
- Fake updates requests. It is possible that Trojan.Gen.Npe might come from clicking on a fake update notification that might be leading to a contaminated web page. This means that you should be very cautious when you update your system, as not all of the displayed update requests will be harmless and genuine. Some of them might be virus-generated, not coming from your OS.
- Another major source of Trojans is the so-called malicious online advertising. It’s possible that the virus has come to you as a component of a fake online advertisement, which unlike the normal ones, contains malware or can redirect you to websites, infected with different forms of malware.
- Torrents, shareware and free software. It is possible that an infection with Trojan.Gen.Npe might result from visiting, opening, downloading or using any free distributed shareware, torrent or program from the Internet. That’s why you should only use software from trusted webpages.
Possible results of an infection with Trojan.Gen.Npe
Another piece of very useful information that you should be aware of is why such viruses get created and what they could be used for. Here we have listed the most common activities of Trojan.Gen.Npe (which also apply to all other versions of Trojans):
- Destruction-oriented usage. Such malware-based programs might simply be exploited with the purpose to destroy or corrupt anything that they infect. This means that all your files are in danger, as well as the entire operating systems. Such contamination might result in a total crash of your computer and the need to completely reinstall your OS.
- Theft-oriented behavior. Trojan.Gen.Npe might act like a data thief. The hackers could have programmed it to copy and record all your account credentials –your social media profiles and online banking accounts, for instance. These cyber criminals either want to hack your online identity or drain your deposits. Either ways is extremely horrifying.
- Malware-spreading function. Trojans might be used for spreading Ransomware and other malicious programs. This is one of the most bothering usages, as your system gets infected with two totally different viruses, which could make it awfully difficult to remove either of them.
- Spying-related usage. In some cases Trojans could be used as tools for spying on you. Such a way of exploiting them includes programming them to remotely control your device and follow all your activities – via recording you through your web camera and microphone and via copying your key strokes.
Possible ways of fighting such a virus
To be honest, dealing with such malware can be difficult and confusing. However, we have come up with a possible solution. Make sure you go through the guide below and closely follow all the instructions in order to effectively remove Trojan.Gen.Npe from your system.
SUMMARY:
| Name | Trojan.Gen.Npe |
| Type | Trojan |
| Detection Tool |
Trojan.Gen.Npe Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment