Trojan.Multi.GenAutorunReg.a
The constantly growing number of malware infections caused by a virus called Trojan.Multi.GenAutorunReg.a is the reason why we have assembled the article below. We have tried to explain everything about Trojan.Multi.GenAutorunReg.a’s nature and the potential serious damage such a program could result in.
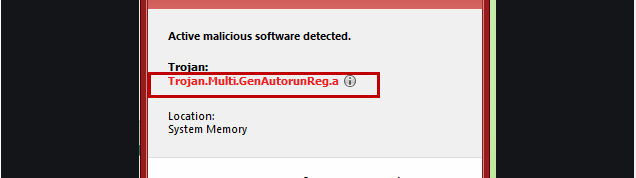
The Trojan.Multi.GenAutorunReg.a Virus can steal your sensitive data
Hopefully the details below will be enough to help you understand the essence of your current issue. In order to assist you in removing this virus, we have attached a guide. Make sure you follow all the instructions and your problem should be easily solved.
What is typical for any Trojan virus?
When it comes to malware infections, most of them are caused exactly by various versions of Trojans. These viruses are indeed the most widely spread and multifunctional ones. They can be distributed in practically any way. We have mentioned some of the most common ones in the next paragraphs. What’s more, they could have such diverse purposes that the possible consequences coming from them might be really varying. Of course, we have discussed the main usages of this type of malware below. The common denominator of all these viruses is their ability to become incorporated in your system in a stealthy way, without directly or indirectly asking for your permission. Also, one more common threat is their ability to stay hidden until the time comes to show their true face (just like the horse they are named after from the famous Trojan War tale).
Possible ways of distributing Trojan.Multi.GenAutorunReg.a:
- Such viruses could be incorporated into web pages, torrents and shareware.
- They might come from video-sharing websites.
- Another possible scenario is to get infected after opening a contagious letter from your email or any attached file, even and image or text document. (Typically, in such a case the Trojan could be distributed together with a Ransomware virus. This possibility is among the worst ones.)
- You may sometimes see some suspicious but genuine-looking update requests on your screen. Please, do not fall into this trap. Such alerts might actually lead to infected pages and you may become a victim of Trojan.Multi.GenAutorunReg.a.
- One more way of catching such malware is via any fake pop-up ad you may come across on the web. Such ads can either directly contain the malicious script or they might redirect you to web addresses containing the virus.
Potential purposes Trojan.Multi.GenAutorunReg.a could have
A virus like Trojan.Multi.GenAutorunReg.a could be exploited for a number of different harmful purposes. Some of them we will mention in the list below. Nonetheless, we cannot name every single usage in one article only, as the range of possibilities of a Trojan is truly spectacular.
- The hackers might just feel the need to DESTROY something. Unfortunately, this might be your system. It could be crashed with such malware. Some of your data might get destroyed, deleted, corrupted or even encrypted. Your OS might get so damaged, that an entire reinstallation might be necessary.
- The cyber criminals behind Trojan.Multi.GenAutorunReg.a might want your MONEY or your IDENTITY for some reason. That is why Trojans are often exploited for recording account credentials, which will later allow the hackers to drain your bank account or hijack your online identity. Some online crimes could also be committed on your behalf, which may lead to legal actions being taken against you for something you never did.
- Sometimes such viruses are used for simply sneaking other malicious programs into your system. Trojans are very often used to transport Ransomware. This scenario is an awful one, as Ransomware is a type of malware specialized in encrypting data and demanding ransom for it. No guarantee is given for the recovery of the hijacked data, no matter whether the victim user refuses or accepts to complete the requested payment.
- The hackers could also be prone to physically abusing people. Some of them use such malware to hack your PC and record your every step – both online and in the real world. They turn on all your devices, such as mics and cameras, to spy on you all the time. Also, they keep track of all your cyber activities. Such a case is particularly disturbing.
What to do to remove such a nasty virus?
If you are looking for a way to get rid of Trojan.Multi.GenAutorunReg.a, you will find plenty of opportunities. In our opinion, you should use our Removal Guide for that purpose. Carefully following the instructions will get your issue resolved.
SUMMARY:
| Name | Trojan.Multi.GenAutorunReg.a |
| Type | Trojan |
| Detection Tool |
Remove Trojan.Multi.GenAutorunReg.a
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

You ought to remove those IP’s from the Hosts file and save the changes afterwards.
First try deleting the shady IP’s and then go back to dllhost.exe.