Detplock
Detplock is a Trojan-based virus that can hide in a computer and activate various malicious processes. There are cases in which Detplock can serve as a backdoor for other malware and insert Ransomware or Spyware inside the infected computer.
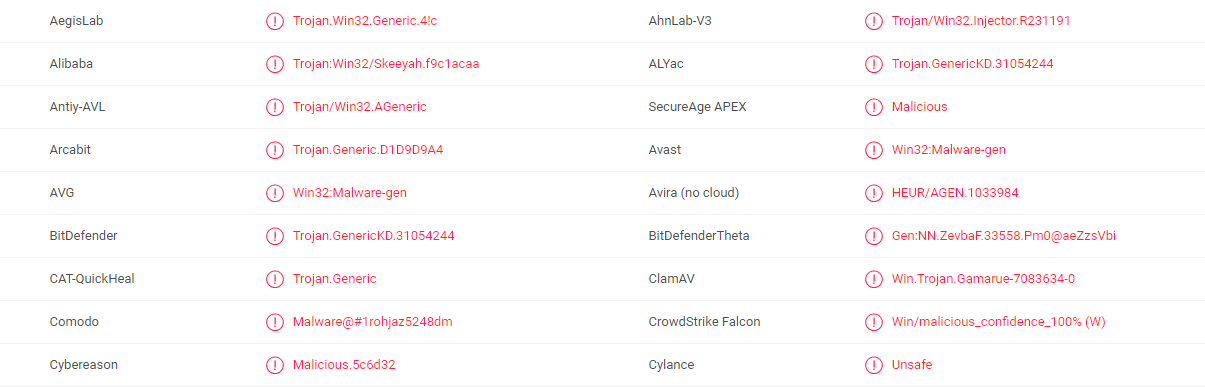
The Detplock Trojan can be detected by multiple antivirus scanners.
In the world of malware, there is one family, whose members are really hard to be spotted by the victim users, and may be used for a great number of evil activities by the hackers that create them. This is the Trojan horse viruses group and today we are going to explain how a certain version of such malware works – Detplock. For more information in general about this malware family, as well as some particular details about Detplock, please continue reading.
These viruses are extremely dangerous, partly because their scope of possible usages could be really big. They are very different and all of them are greatly concerning. We are going to explain the most common possibilities of using Trojans in the paragraphs below. What’s more, we will elaborate on the potential sources of these viruses, as they could be numerous and greatly varying as well. What all these viruses have in common and the same family is their ability to exploit certain vulnerabilities of your system to get in. Also, all of these malware versions are perfectly capable of self-integrating into your PC – they do not even need indirect permission from you to enter your system. After that all of them tend to secretly start to implement what they have been programmed to and you may not be able to notice these activities before the virus has completed the whole process.
The Detplock Trojan
The number and the nature of the possible usages Detplock and other Trojans can vary greatly. In fact, we can hardly name all of them. That is why we have compiled a list of the most widely-spread ones, so that you can have a slight idea of what might be going on inside your system.
- Data corruption / system destruction. Detplock might be programmed to crash your system or to destroy some of the files you keep there. This might not be personal – sometimes the hackers just have fun like this. However, this potential usage is very disturbing, as you might lose important files or need to reinstall the entire system.
- Means of transport for other hazardous programs. Trojans are often used for sneaking other versions of malware inside your PC. Usually, the transported viruses are Ransomware-based, which means the files you consider important are in great danger, as Ransomware tends to encrypt them with a specific double-component key and then insist that the harassed user pay ransom for them. This is one of the most disturbing potential usages of Trojans, as you get two malware infections simultaneously.
- Draining system resources. The hackers could be after your system resources. They may need them for a variety of dishonest activities like sending spam and mining crypto currencies. In this case your computer could be transformed into a bot. It could be remotely controlled and various crimes could get committed on your behalf. You may even end up being accused of something you have never done. So, this usage is not harmless at all.
- Personal information and credential theft that might result in various crimes. Hackers might use Detplock to record your key strokes. As a result the hackers might steal any of your account credentials. Consequently, the hackers could be able to drain your bank deposits or hijack your social media accounts, thus assuming your identity. This one is among the most hazardous possible usages of Trojans as a whole.
The ways your system might end up contaminated with Trojans
- Via spam letters from your email and their attachments. This possibility is very common. Hackers often integrate Trojans into emails and their attachments (images, archives, documents). That is why you should avoid all the suspicious ones both inside your Inbox and your Spam Folder.
- Via malicious pop-up advertisements on the web. This is also a pretty common way of spreading Detplock and other Trojans around. The fake ads you may come across are not as harmless as the usual pop-ups and banners. They might redirect you to malware-containing web pages, which might result in contamination. Our advice is to stay away from all sorts of online ads.
- Via shareware, torrents and streaming websites. Another possible way of catching a Trojan is if you use any suspicious websites that spread torrents, videos, images or anything for free on the Internet. Often such pages contain various viruses. Visit only websites you really trust to stay safe.
In case you need to remove Detplock from your PC
Fortunately, we have developed a specialized guide to help you with that. Stick to the instructions carefully and you will be able to remove this dangerous infection.
SUMMARY:
| Name | Detplock |
| Type | Trojan |
| Detection Tool |
Detplock Trojan Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment