This page aims to help you remove the Trojan.worm Ransomware Infection. Our removal instructions work for Chrome, Firefox and Safari, as well as every version of Windows.
Trojan.worm
Trojan.worm is regarded as a type of a browser hijacker. Threats like Trojan.worm are known to cause different problems like changing of the user’s designated home page or even the preferred browser of choice.
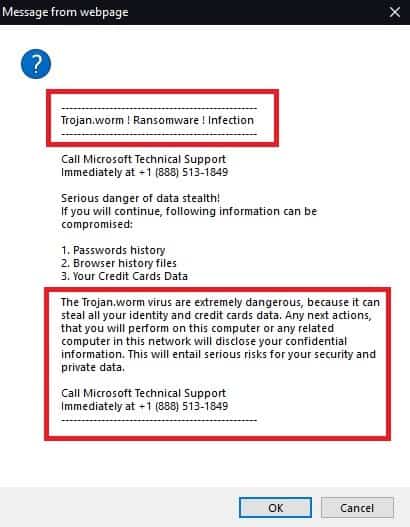
The Trojan.worm Ransomware Infection will display pop up windows and messages
If you want to maintain a safe and secure computer, you should definitely take care of every piece of software which might have a potentially unwanted behavior or might have ended up on your system without your permission. Unfortunately, there are many applications on the Internet which may get installed on your PC by default along with other applications or due to your negligence and Trojan.worm is one of them. This application is considered to be undesirable because it operates as a typical Browser hijacker. The Browser hijackers, are pieces of software, famous for their ability to irritate the web users with various annoying ads, pop-ups, banners and automatic page redirects. They are usually the source of some undesired homepage or search engine changes in the users’ browser and oftentimes affect popular browsing programs like Chrome, Firefox, Explorer, and others. If left to operate on the system, applications like Trojan.worm are generally not as harmful as a Trojan horse or a Ransomware virus. However, they can be very annoying when they trigger random page-redirects and expose you to various unfamiliar and unwanted advertisements. Therefore, it is usually advisable to uninstall any browser hijackers from the system as this is the only effective way to remove their nagging advertising activities. Fortunately, on this page, our “How to remove” team has prepared the exact steps to do that. So, if you want to quickly and safely uninstall Trojan.worm from your machine, we suggest you pay close attention to the steps in the Removal Guide below.
Message from webpage Trojan.worm Ransomware Infection
Researchers have labeled Trojan.worm a browser hijacker. Security problems such as Trojan.worm are known to cause website redirects, intrusive advertisements and even phishing attempts.
If you notice an application which starts to modify your browser settings and affects the way you surf the web, what would you do? Yes, you most probably you’d would like to find out what kind of software this is and whether it can do something harmful to your PC. Usually, the modifications that Browser hijackers such as Trojan.worm tend to impose are very obvious and also very annoying. They take place immediately after the application becomes part of your system. Letting the hijacker operate on your computer usually leads to automatic page-redirects to various sponsored websites, links, offers and ads of different types. New toolbars, search engines or homepage domains may also get incorporated and replace your preferred ones.
Obviously, this is something that most of the users won’t enjoy. It is also probably not the best idea to keep such software on your system and let it take control over your web surfing without asking for your permission. After all, if you are aware of the Internet threats, letting a third party application automatically redirect you to predefined web locations may hide certain security risks. For instance, if you happen to click on a misleading link, a contaminated piece of content, a sketchy website, an ad or a pop-up, you may land on some really nasty malware.
However, we need to clarify here that exposing you to computer viruses such as Ransomware, nasty Spyware and Trojans is not the goal of a piece of software like Trojan.worm. The primal purpose of such an application is to advertise and to earn revenue for its developers thanks to Pay-Per-Click ads or sponsored ads positioning. This explains the never-ending stream of commercials of various kinds that Trojan.worm tries to force on you. Still, despite not having malicious intentions, a hijacker may indirectly open up the way for other nasty threats into your computer if you are not careful with what you click on. That’s why, if you have such an application on your system, you should better try to avoid its redirects and sponsored ads until you fully uninstall it.
The Trojan.worm Ransomware Infection
Trojan.worm is a browser hijacker type of a security nuisance. Trojan.worm is categorized by the website redirects and pop-up ads it causes but it could potentially lead to even more serious problems.
The creators of browser hijackers and similar ad-generating or page-redirecting applications usually profit from the clicks and the site visits their software generates. That’s why, it is not surprising that most hijacker developers try to distribute and install these applications on as many computers as possible. For that, they use some very common and technically legitimate methods of installation known as “software bundling”. The browser hijacker usually becomes part of the system when the users download a software bundle (a set of applications, mostly free ones) and install it via the Quick/Automatic options without checking for optional or added components which might be included in the setup and could be potentially unwanted. Luckily, a simple click on the Advanced/Manual/Custom options can reveal these additional components and let you disable them from the bundle.
SUMMARY:
| Name | Trojan.worm |
| Type | Browser Hijacker |
| Detection Tool |
Remove Trojan.worm Ransomware Infection
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment