This page aims to help you remove .Truke Virus Ransomware for free. Our instructions also cover how any .Truke Virus Ransomware files can be recovered.
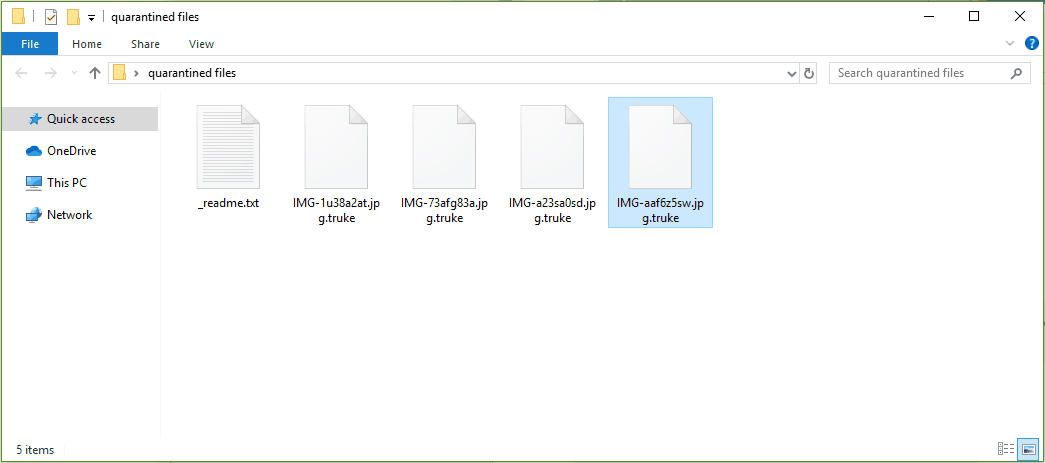
The .Truke Virus will leave _readme.txt file in your computer with instructions for you to follow.
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
*Redacted for security reasons*
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
The World Wide Web undoubtedly gives countless possibilities to customers all over the globe. Nonetheless, the dangers that are hiding there are also numerous, which is the reason why one has to be really careful when going on the internet. One particularly hazardous type of malware which is going to be the focus of the present post is called Ransomware. The main purpose of Ransomware cryptoviruses is to blackmail its victim, pressuring them to carry out a ransom transfer to the cyber-criminal who controls the cryptovirus program. Inside the paragraphs below, we’ll be putting an emphasis on a particular Ransomware, that’s able to lock-up your personal files, rendering them unavailable to anyone who doesn’t have the decryption key. After blocking the access, the malicious program requests a ransom payment which is required to be issued by the victim, assuming they would like to obtain the decryption key for unsealing the encrypted files. If you are reading this, the chances are that you have already confronted this unpleasant malware, labeled .Truke Virus. And you are not the only one. Numerous unlucky web users have recently become victims of this stealthy virus, and some of them have asked our “How to remove” team for help. That’s why in the next lines you will find some critical information which might help you remove .Truke Virus and give a try to some alternative file-recovery methods, which don’t involve paying ransom to the online hackers.
Important specifics about .Truke Virus and Ransomware in general
What you should bear in mind about Ransomware is the fact that all the virus infections that fit in this category are quite different from the majority of the other malware. A very important thing that web users should know about this kind of computer threats is that most security programs may not be effective enough against them. The reason for this has to do with the fact that Ransomware infections like .Truke Virus don’t normally try to directly damage anything on your computer, so there is nothing that can trigger a security warning from your antivirus program.
Normally, data encryption isn’t a damaging method – this is one of the most commonly used file-protection method which finds its implementation in many sectors where digital data should be kept safe from unauthorized access. The issue arises from the actual way this encryption method is utilized by the virus. .Truke Virus Ransomware, for instance, is part of the .DJVU family and uses the encryption to prevent its victims from accessing their personal files and to blackmail them. One more disturbing aspect of this kind of infections is the fact that the symptoms of such malware are rather challenging to detect and almost invisible, which makes the detection and removal even harder. Nonetheless, in case you identify some particularly unusual System behavior, it is advisable to turn the device off and contact an expert.
Do not panic and, most importantly, do not send your money to some anonymous hackers in case of infection. This is because the success of the Ransomware blackmail scheme relies mainly on the panic of the victims and their impulsive decisions. At the same time, there are no guarantees about the successful recovery of the encrypted files even if you fulfill all of the ransom demands. That’s why most security experts, including our “How to remove” team advise that it is of tremendous importance to explore all the alternatives when dealing with infections like .Truke Virus and never instantly satisfy the demands of the hackers that stand behind them.
SUMMARY:
Remove .Truke Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply